Walk the Compliance Walk with ClickUp and Drata
Sorry, there were no results found for “”
Sorry, there were no results found for “”
Sorry, there were no results found for “”
Adam Markowitz is the co-founder and CEO of Drata, an advanced automation platform designed for continuous SOC 2 and ISO 27001 compliance.
Prior to Drata, Adam was the founder and CEO of Portfolium, an academic portfolio network for students and alumni to visually showcase their work and projects directly to employers, faculty, and fellow students/alumni. Portfolium was acquired by Instructure (NYSE:INST) in 2019.
He also worked as an aerospace engineer designing, analyzing and testing liquid rocket engines for NASA’s next-generation space launch vehicle as well as the Space Shuttle Main Engine. Adam earned a B.S. in Structural Engineering from UC San Diego and an M.S. in Astronautical Engineering from the University of Southern California.
With remote work and increasingly sophisticated security threats on the rise, if your organization is storing or processing any customer data in the cloud, then protecting that data must be a top priority. With an estimated 18 billion pieces of information exposed in the first half of this year alone, not having a strong security program in place could come at a frightening cost for SaaS companies.
So it shouldn’t be a surprise if a customer or prospective customer requests assurance over the controls you have in place to protect their data – nowadays, not having tangible proof of a trustworthy security program can be a major dealbreaker. 💔
One of the best ways to provide this assurance is through SOC 2 compliance— meeting SOC 2 compliance is considered the 🎇 gold standard🎇 of security and data protection.
SOC stands for system and organization controls.
That’s not the only acronym you’ll need to know, but we’ll start here for now. 😉
If you’re new to compliance, you’re also likely new to SOC 2. Don’t worry, a lot of companies are in the same boat, but a simple breakdown can give you an idea of just how handy SOC 2 compliance is.
Created by the American Institute of Certified Public Accountants (AICPA), SOC 2 is a set of control criteria that outline the requirements for the five categories:
Organizations like yours design and implement controls across the company in order to satisfy these criteria. A control is a process or policy you put in place to mitigate the risk of an event occuring that could compromise the security, confidentiality, availability, integrity, or privacy of sensitive data.
For example, a smoke detector is a control to detect if a fire is burning in your home, and a bicycle helmet is a control to prevent head injury while riding your bike.
The same concept applies to protecting data and implementing an effective security program.
Proving that you’ve designed and implemented effective controls to satisfy the SOC 2 criteria is accomplished in a SOC 2 audit, conducted by a certified public accountant (CPA). The result of your SOC 2 audit is a SOC 2 report, commonly known as an attestation report… fancy!
And, there are two types of SOC 2 compliance that serve different purposes:
P.S. The acronyms aren’t so bad, right? 😃
Just as project deliverables are a key component to completing a project, compliance is a key component to building a strong security program.
So what does a “clean” SOC 2 report mean?
It means that you’ve taken the right steps and implemented the right policies, procedures, and controls to meet the SOC 2 criteria. Companies that have been interested in working with you can now have peace of mind that you’re taking the right steps to protect their data. Next time you get a customer question about your company’s security program, a clean SOC 2 report will go a long way.
Taking the proper steps to obtain a SOC 2 report is well worth the journey. Don’t lose a deal because you can’t prove compliance. Once you have SOC 2, you can move seamlessly into achieving additional frameworks (ISO 27001, HIPAA, etc.) as your company expands.
Starting the journey can be daunting, especially if you’re still learning about compliance along the way. Up until now, most companies spent hundreds of hours collecting thousands of screenshots, building out static spreadsheets, and taking their engineering team away from a product roadmap in order to achieve SOC 2.
No wonder so many companies, especially those in early stages with limited resources, have often been hesitant to jump on the SOC 2 bandwagon…even when it means accelerating business and closing more deals.
Now, there are ways to make compliance way less scary than that dentist appointment you’ve been avoiding.
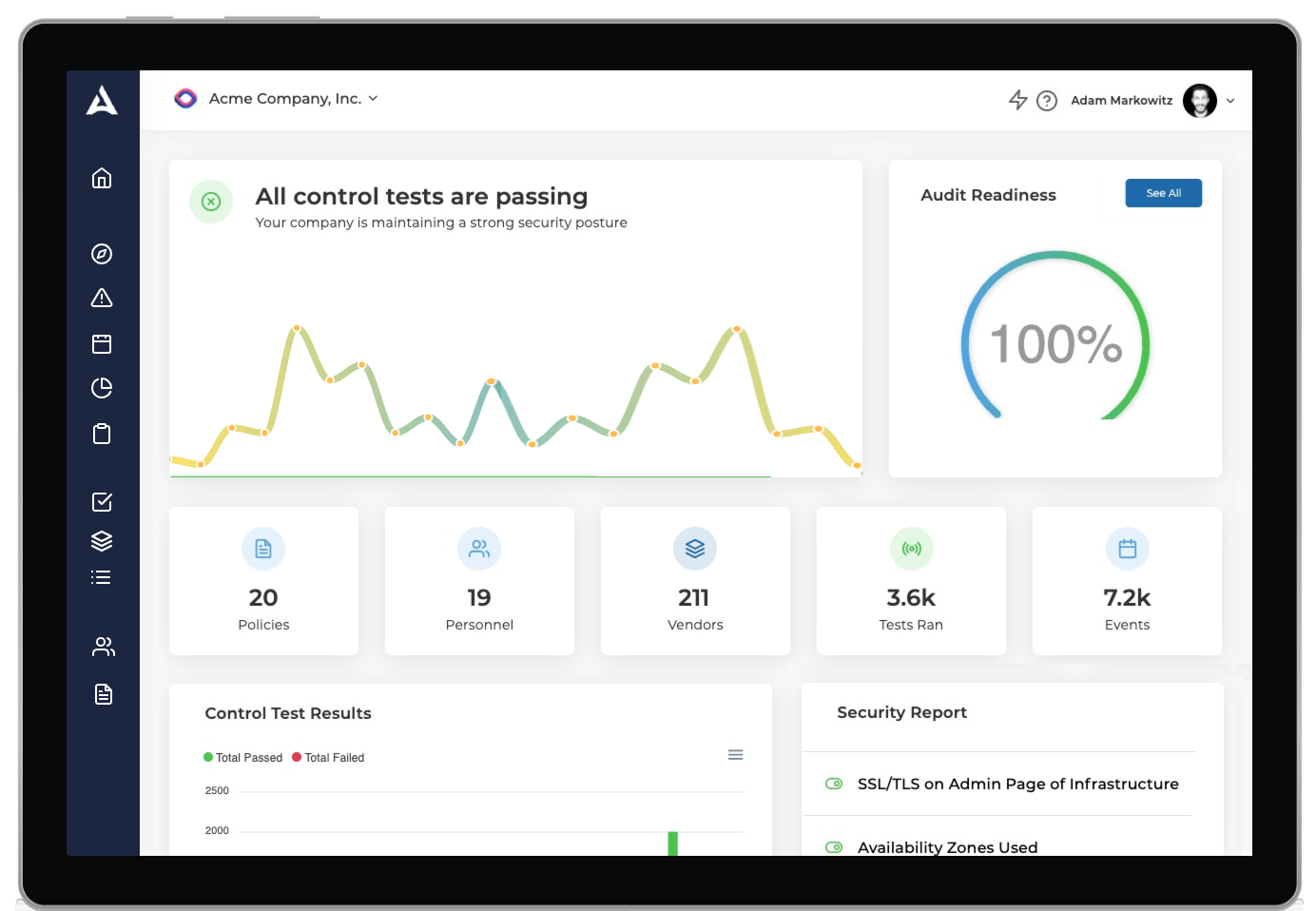
Drata is a security and compliance automation platform that greatly streamlines the tasks required for a successful SOC 2 audit. Rather than treating compliance like a static checklist, Drata helps you achieve and maintain compliance in one platform and easy-to-read dashboard. We’re the wind beneath your compliance wings, if you will.
We could go on and on about what makes Drata so great, but here’s what sticks out:
There are a ton of other awesome features from Drata, including alerts, templates, and training. And nothing says “trust” like when your customers ask for a security report, and you know exactly where it is and how to share it.
ClickUp and Drata are now fully integrated so you can connect your account, run tests to uncover pesky security snags, and nip them in the bud right away.
Just like evidence collection, these tests are also automated, so your team will regain valuable time to focus on the business.
Connect ClickUp and Drata together to get ahead of an incident and manage your vulnerabilities in order of priority so you can pass future audits with flying colors!
If your security posture is a spine, think of compliance as a chair. Can you sit in a chair that’s old or lacks full support, or even sit without a chair at all? Sure, but will your posture get worse because of it? Are those pains that start as minor nuisances poised to become something more debilitating? Absolutely.
Is it too late to fix because of where your posture is at now? Definitely not. An advanced automation tool like Drata is that super comfortable ergonomic chair that immediately improves your posture and keeps you sitting upright, both today and far into the future.
If you’re looking to stop slouching with security, consider Drata.
Find out more about how Drata integrates into your business and keeps your data safe with continuous, automated compliance. 🔐

Pavitra M
Max 16min read

Sudarshan Somanathan
Max 18min read

Praburam Srinivasan
Max 18min read

© 2026 ClickUp