Implementing a Visitor Access Control System involves multiple coordinated tasks across security, IT, and facilities teams. This Work Breakdown Structure (WBS) template provides a comprehensive framework to organize these tasks into manageable sections, facilitating smooth project execution.
This specialized template helps you:
- Segment the project into key phases such as requirements gathering, hardware installation, software configuration, and training
- Assign responsibilities to security personnel, IT specialists, and vendors to ensure accountability
- Monitor progress in real-time, enabling timely adjustments and risk mitigation
Best of all, this template requires no coding or complex software—just ClickUp to get started and keep your Visitor Access Control System project on track.
Benefits of a Visitor Access Control System Work Breakdown Structure
Using this WBS template offers significant advantages for managing your visitor access control project:
- Clearly defines deliverables such as system design, hardware procurement, installation, testing, and user training
- Clarifies roles and responsibilities among stakeholders including security managers, IT teams, and external contractors
- Enhances communication by providing a shared visual roadmap accessible to all team members and stakeholders
- Improves project efficiency by identifying dependencies and critical path activities, reducing delays and cost overruns
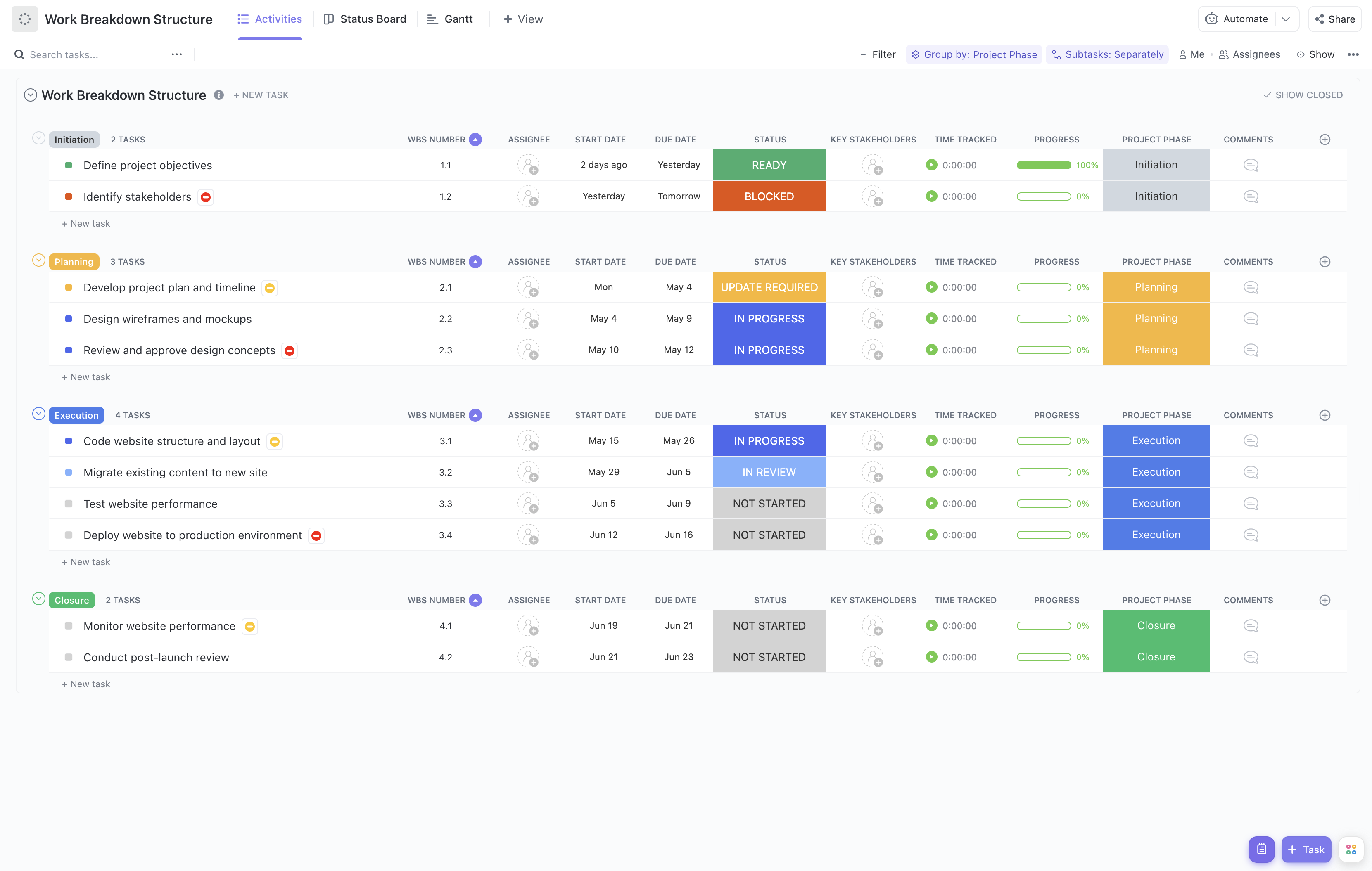
Main Elements of the Visitor Access Control System WBS Template
This template is structured to cover all essential components of the project:
- Project Initiation: Define scope, objectives, and key stakeholders for the access control system deployment.
- Requirements Analysis: Gather security needs, compliance requirements, and visitor management policies.
- System Design: Develop technical specifications, select hardware and software solutions, and plan integration with existing infrastructure.
- Procurement: Source access control devices, software licenses, and installation services.
- Installation and Configuration: Deploy hardware components, configure software settings, and integrate with security systems.
- Testing and Validation: Conduct functional tests, security audits, and user acceptance testing to ensure system reliability.
- Training and Documentation: Provide training sessions for security staff and create user manuals and operational procedures.
- Go-Live and Support: Launch the system, monitor initial usage, and establish support protocols for maintenance and troubleshooting.
By following this structured approach, your team can effectively manage the complexities of implementing a Visitor Access Control System, ensuring a secure and efficient visitor management process.