Managing information security projects involves navigating complex regulatory requirements, risk assessments, and technical implementations. Breaking down these multifaceted projects into manageable components is essential for success. That's where ClickUp's Information Security Management Work Breakdown Structure Template comes in!
This specialized template helps you:
- Organize security tasks into clear, manageable sections such as risk assessment, policy development, and incident response
- Align security team members and stakeholders to their specific responsibilities quickly and efficiently
- Track compliance milestones and security objectives with real-time updates
Best of all, no coding knowledge or special software is required—just ClickUp, and you're ready to structure your information security projects for success!
Benefits of an Information Security Management Work Breakdown Structure Template
Using a WBS template tailored for information security management provides a visual roadmap for completing your security initiatives on time and within compliance standards. Key benefits include:
- Clearly defines and organizes critical security deliverables such as vulnerability assessments, security awareness training, and audit preparations
- Clarifies roles and responsibilities for security analysts, compliance officers, and IT teams
- Enhances communication between security teams, management, and external auditors
- Improves overall efficiency by identifying dependencies and prioritizing high-risk tasks
Main Elements of the Information Security Management Work Breakdown Structure Template
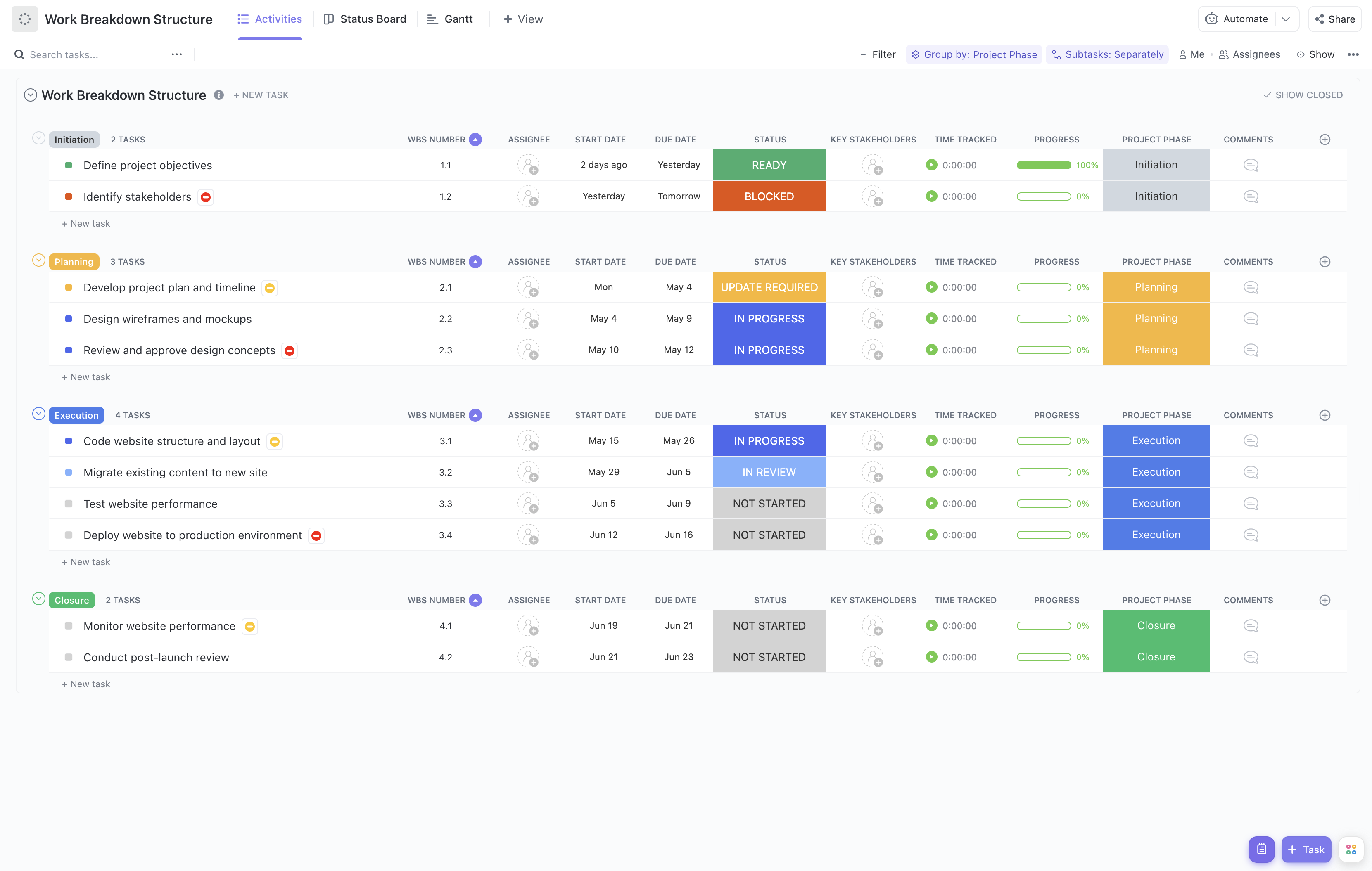
This template breaks down your information security project into hierarchical components, including:
- Project Initiation: Define scope, identify stakeholders, and establish security objectives
- Risk Assessment: Conduct asset inventories, threat analysis, and vulnerability assessments
- Policy and Procedure Development: Draft and review security policies, standards, and guidelines
- Implementation: Deploy security controls, configure systems, and conduct training sessions
- Monitoring and Review: Perform audits, monitor security events, and manage incident response
- Project Closure: Finalize documentation, conduct lessons learned, and ensure compliance reporting
Each task can be assigned to specific team members with due dates and progress tracking, enabling seamless collaboration and accountability across your information security management project.
With this template, you can confidently manage complex security projects, ensure regulatory compliance, and protect your organization's critical assets effectively.









