Rolling out identity access solutions across an organization involves numerous interdependent tasks, from requirements gathering to deployment and user training. Managing these activities effectively is crucial to ensure security compliance and operational continuity. This Identity Access Rollout Work Breakdown Structure (WBS) Template provides a structured approach to decompose the rollout project into clear, manageable tasks.
This specialized template helps you:
- Organize identity access rollout tasks into logical phases and deliverables for enhanced clarity
- Assign responsibilities to security teams, IT administrators, and stakeholders efficiently
- Monitor progress in real-time to identify bottlenecks and ensure timely completion
Best of all, no coding or specialized software is required—just ClickUp to get started with your identity access rollout planning and execution!
Benefits of an Identity Access Rollout Work Breakdown Structure Template
Using a WBS template tailored for identity access rollout projects offers multiple advantages:
- Clearly defines and organizes project deliverables such as policy development, system configuration, and user onboarding
- Provides transparency on roles and responsibilities across IT security, compliance, and end-user support teams
- Enhances communication between project stakeholders, ensuring alignment on goals and timelines
- Improves overall project efficiency by breaking down complex security implementations into actionable tasks
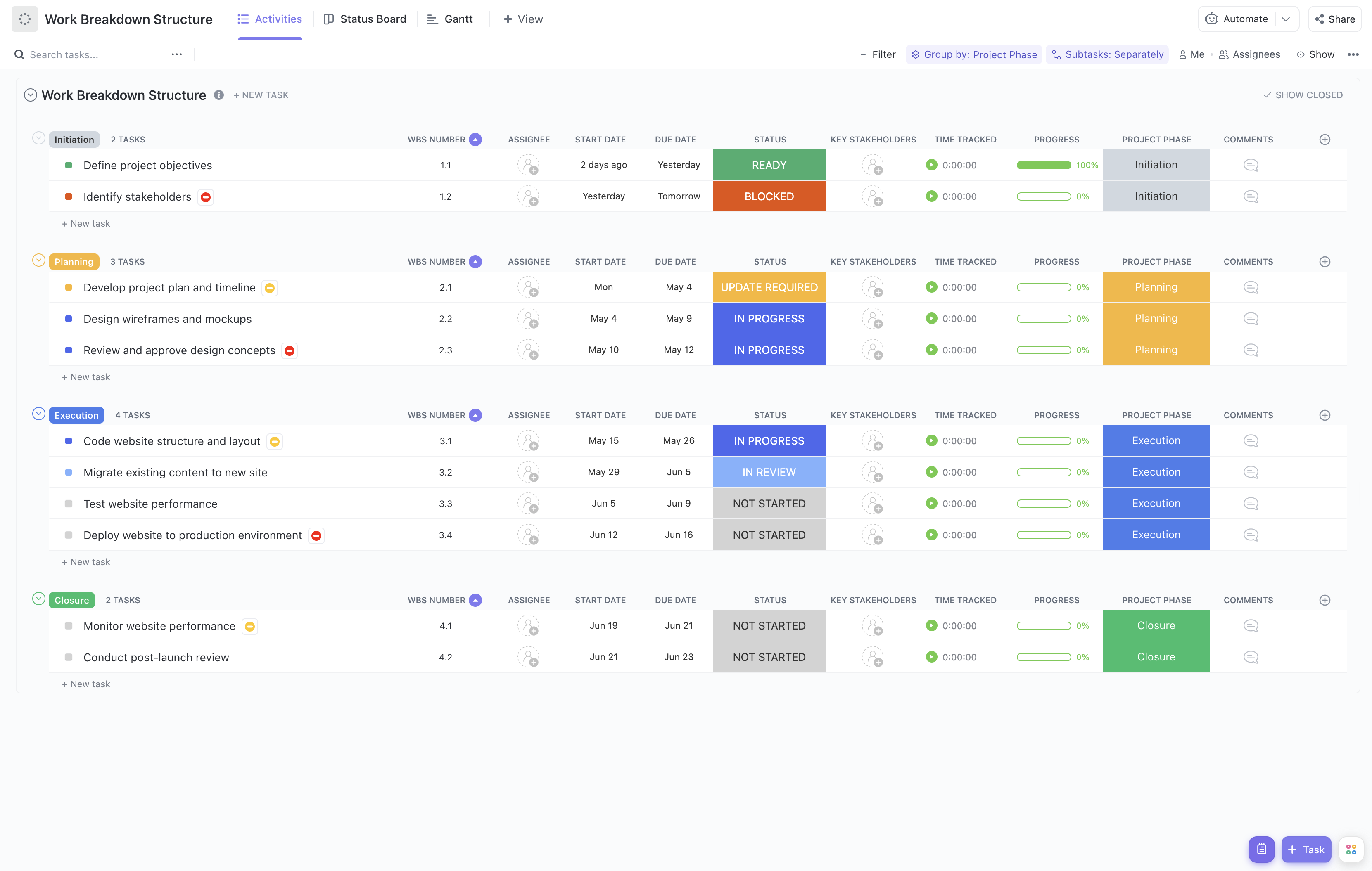
Main Elements of the Identity Access Rollout Work Breakdown Structure Template
This template structures the rollout project into key components including:
- Project Initiation:
Define scope, identify stakeholders, and establish governance for the rollout.
- Requirements Analysis:
Gather and document access control requirements aligned with organizational policies.
- Design and Planning:
Develop access models, define roles and permissions, and plan deployment strategies.
- Implementation:
Configure identity and access management systems, integrate with existing infrastructure, and conduct testing.
- Training and Communication:
Prepare training materials, conduct sessions for administrators and end users, and communicate changes.
- Deployment and Monitoring:
Roll out access controls to production, monitor system performance, and address issues promptly.
- Project Closure:
Finalize documentation, obtain stakeholder sign-off, and conduct post-implementation review.
By following this structured approach within ClickUp, your team can seamlessly coordinate the identity access rollout, ensuring security objectives are met while minimizing disruption to business operations.