Scope of work documents are an essential part of any project workflow. The right scope of work template ensures that everyone involved in a project is on the same page and working towards the same goals.
ClickUp's Scope of Work Template provides an easy-to-use, no-code framework to help you:
- Define the scope and objectives of your project
- Outline timelines, tasks, and deliverables
- Automate communication with stakeholders
Whether it's a one-off project or an ongoing effort, this template will help you manage everything from concept to delivery—all in one place!
Benefits of a Scope of Work Template
A scope of work template is a great way to ensure that everyone on your team is on the same page when it comes to tasks, deadlines, and expectations. Here are some of the benefits of using a scope of work template:
- Helps create a clear plan of action for the project
- Makes it easier to estimate time and cost for completing the project
- Ensures that everyone is properly informed and on the same page
- Helps keep the project on track and ensure that deadlines are met
Main Elements of a Scope of Work Template
ClickUp's Scope of Work Template is designed to help you capture and manage details about a project. This Doc template includes:
- Custom Statuses: Create ClickUp tasks with various custom statuses to keep track of the different stages of your project
- Custom Fields: Categorize and add attributes to manage your project to provide visibility to your product team and other stakeholders
- Custom Views: Start with this Doc template and build out your ClickUp workflow which includes List, Gantt, Workload, Calendar, and more
- Project Management: Improve project tracking with screen recording, collaborative editing, automations, AI, and more
How to Use a Scope of Work Template
Creating a Scope of Work document can help ensure that your project is a success. Following these steps can make the process easier:
1. Establish goals
Before creating a Scope of Work document, it’s important to establish the goals and objectives of the project. This includes the purpose, deliverables, timeline, and budget.
Create a Doc in ClickUp to gather the project’s requirements and goals.
2. Identify stakeholders
Identify all the stakeholders involved in the project, including the client, team members, and any other parties who need to be informed.
Use tasks in ClickUp to list all the stakeholders and assign them to specific roles.
3. Describe the scope of work
In the document, clearly define the scope of work by outlining the tasks, deliverables, timeline, and budget.
Create custom fields in ClickUp to track all the necessary scope of work information.
4. List any limitations
It's also important to include any limitations in the document, such as any restrictions on the use of materials, equipment, or personnel.
Create tasks in ClickUp to list any limitations and assign them to specific stakeholders.
5. Review and revise
Once the document is complete, review it with all stakeholders to ensure that everyone is in agreement. If changes are needed, make sure to revise the document accordingly..
Set a recurring task in ClickUp to regularly review and revise your Scope of Work document.
6. Sign and distribute
Once the document is finalized, have all stakeholders sign it and make sure to distribute a copy to everyone involved.
Use Email in ClickUp to sign and distribute your Scope of Work document.
Get Started with ClickUp's Scope of Work Template
Project managers and contractors can use this Scope of Work Template to help everyone stay on the same page when it comes to defining project goals and outlining work expectations.
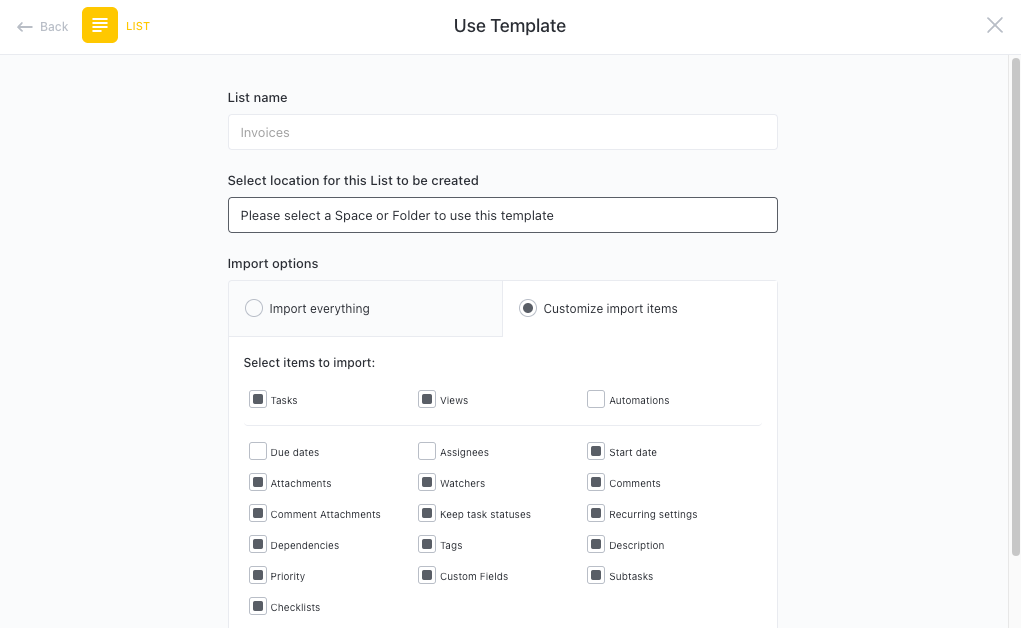
First, hit “Add Template” to sign up for ClickUp and add the template to your Workspace. Make sure you designate which Space or location in your Workspace you’d like this template applied.
Next, invite relevant members or guests to your Workspace to start collaborating.
Now you can take advantage of the full potential of this template to create and manage scopes of work:
- Set up a project for each scope of work
- Create tasks and assign team members to each task
- Collaborate with stakeholders to discuss details and create content
- Organize tasks into categories to keep track of progress
- Set up notifications to stay up-to-date on progress
- Hold regular meetings to discuss progress and any issues
- Monitor and analyze tasks to ensure maximum productivity
Get Started with Our Scope of Work Template Today









