Task Management Tailored for Threat Hunters
Task Management Software Designed Specifically for Threat Hunters
Centralize your investigations, monitor threat timelines, collaborate with your security team effortlessly, and gain full visibility into every stage of your threat hunting operations.
Trusted by the best
The Need for Precision
Why Threat Hunters Rely on Specialized Task Management Software
Without a dedicated system, threat hunting becomes fragmented, error-prone, and inefficient—turning critical security tasks into chaotic workflows.
- Threat data scattered across tools — tracking indicators and alerts becomes confusing and unreliable.
- Investigation steps get lost — unclear task ownership and missing details delay response.
- Manual tracking increases errors — inconsistent documentation leads to overlooked threats.
- Collaboration breakdowns slow response — unclear communication hinders rapid decision-making.
- Deadlines for incident response slip — critical timelines for containment and remediation are missed.
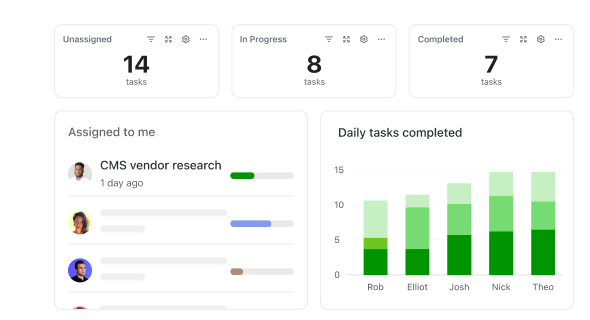
- Visibility into progress is limited — lacking clear status updates hampers threat assessment.
- Resource conflicts arise — overlapping tool usage and analysis efforts reduce efficiency.
- Context switching reduces focus — bouncing between platforms wastes valuable time.
Conventional Approaches vs ClickUp
Why Traditional Methods Fall Short for Threat Hunting
Discover how ClickUp brings clarity and control to security operations that conventional tools can't match.
Traditional Practices
- Threat indicators scattered across spreadsheets and emails
- Manual note-taking prone to errors and omissions
- Incident tracking lacks automation and consistency
- Collaboration hindered by siloed communications
- Deadlines for containment and reporting often missed
- Critical logs and evidence stored in disparate locations
ClickUp Task Management
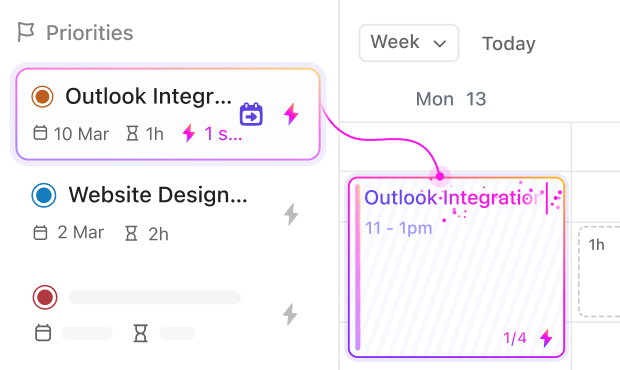
- Centralized threat tracking with prioritized statuses
- Structured investigation workflows with reusable templates
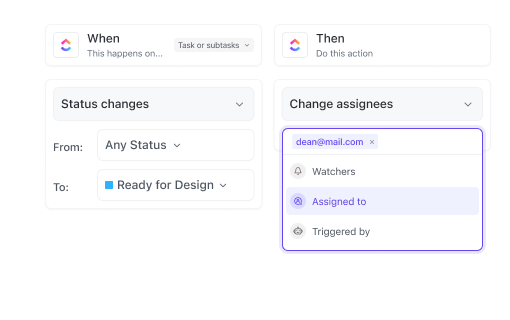
- Automated alerts and reminders for key deadlines
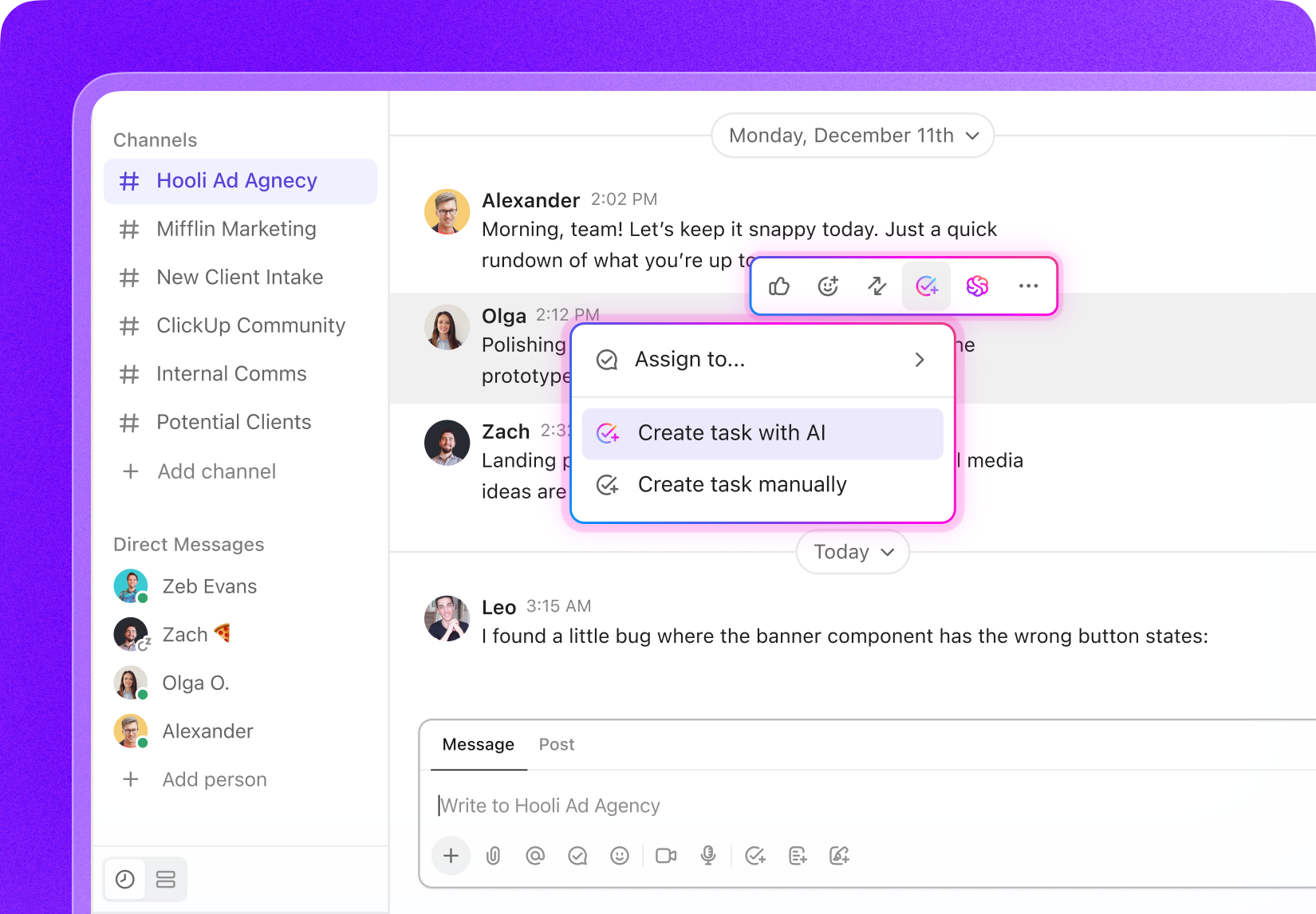
- Real-time collaboration with task ownership and comments
- Integrated evidence and logs attached to relevant tasks
- Advanced search capabilities across all investigation assets
Use Cases
Unlocking the Full Potential of Task Management for Threat Hunters
See how ClickUp streamlines your hunting process, reduces distractions, and sharpens focus.
#UseCase1
Consolidating Threat Intelligence Across Tools & Teams
Stop losing track of indicators, alerts, and analysis — ClickUp centralizes all data with searchable attachments tied directly to your investigation tasks.
#UseCase2
Maintaining an Audit Trail for Incident Response & Compliance
Ensure every step from detection to remediation is documented. ClickUp logs task changes, comments, and evidence for complete traceability.
#UseCase3
Managing Dynamic Feedback from Security Analysts
Threat landscapes shift rapidly. ClickUp keeps feedback organized with threaded comments, mentions, and version control — so your team adapts instantly.
#UseCase4
Preventing Investigation Drift During Extended Cases
Long investigations risk losing focus. ClickUp’s templates, checklists, and task dependencies maintain consistency and thoroughness throughout.
#UseCase5
Tracking Compliance Requirements and Reporting Deadlines
Stay on top of regulatory mandates and reporting timelines with customizable workflows, automated reminders, and progress dashboards.
#UseCase6
Mapping Complex Threat Analysis Pipelines
From data collection to threat validation, ClickUp’s statuses and custom fields help you visualize and control every phase of your analysis.
#UseCase7
Avoiding Missed Alerts and Response Windows
ClickUp schedules and monitors essential alerts and containment actions, ensuring swift response to evolving threats.
#UseCase8
Eliminating Duplicate Investigations and Data Overlap
Track each threat as a task with tags and linked evidence to prevent redundant efforts and maximize analyst productivity.
#UseCase9
Turning Security Meetings into Actionable Defense Plans
Convert brainstorming sessions into assigned tasks with clear owners, checklists, and deadlines to accelerate incident resolution.
Key Beneficiaries
Who Benefits Most from ClickUp in Threat Hunting
Ideal for security analysts, incident responders, and threat intelligence teams seeking streamlined workflows.
If You’re a Security Analyst
ClickUp helps you prioritize alerts, document findings, and coordinate investigations without juggling multiple tools or losing critical information.
If You’re an Incident Responder
Standardize response protocols, track containment steps, and communicate effectively with your team to resolve incidents faster and with confidence.
If You’re Part of a Threat Intelligence Team
Coordinate analysis across global members, manage shared intelligence feeds, and maintain clarity on evolving threats with centralized task tracking.
How ClickUp Empowers Threat Hunters
Step-by-Step Support for Every Phase of Threat Hunting
Manage alerts, investigations, and reporting without switching platforms.
Centralize Everything
Store literature, datasets, protocols, drafts, and grant docs in one workspace — no more scattered files.
Plan Research in Phases
Break projects into proposal, literature review, experiments, analysis, and writing with task lists and Gantt timelines.
Standardize Experiments & Fieldwork
Use templates and checklists for repeatable, error-free lab or field procedures.
Collaborate Across Teams
Assign tasks to co-authors, lab members, or collaborators. Shared boards and dashboards keep everyone aligned.
Turn Meetings Into Actionable Tasks
Convert supervisor or lab meetings into tasks with owners, checklists, and deadlines.
Stay on Top of Deadlines & Funding
Track grants, conferences, and submissions with automated reminders and calendars.