Task Software for Information Security
Task Management Tailored for Information Security Checks
Centralize your security tasks, monitor compliance milestones, collaborate with your team effortlessly, and maintain clear oversight throughout every audit phase.
Trusted by the best
The Need for Organized Security Checks
Why Information Security Teams Require Specialized Task Management
Handling information security without a structured system causes gaps, scattered data, and escalating risk — turning routine checks into complex challenges.
- Compliance deadlines become blurry — making it tough to confirm which audits are complete or pending.
- Security documentation piles up — policies and reports get misplaced or inconsistent.
- Incident tracking becomes inconsistent — missing logs or notes lead to incomplete investigations.
- Collaboration on remediation slows — unclear responsibilities and fragmented communication delay fixes.
- Audit preparations slip through — regulatory submissions risk being late without proper tracking.
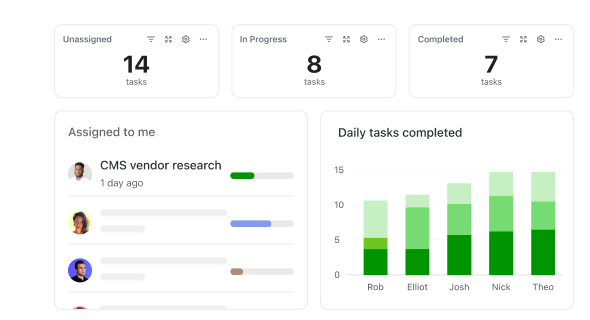
- Visibility into security posture fades — without clear progress indicators, risk remains unmanaged.
- Communication breakdowns occur — emails and chats scatter crucial security updates.
- Resource allocation conflicts arise — overlapping audits or tool usage hinder efficiency.
Conventional Approaches vs ClickUp
Why Traditional Security Methods Fall Short
Discover how ClickUp brings clarity and control traditional tools lack.
Conventional Methods
- Tasks scattered across spreadsheets, emails, and memory
- Security policies stored in disconnected documents
- Incident logs tracked manually with high error potential
- Remediation efforts lack clear ownership
- Compliance deadlines often missed
- Notes and reports dispersed across drives and chats
ClickUp Task Management
- Centralized security tasks with transparent statuses and priorities
- Organized policy repositories with tagging and notes
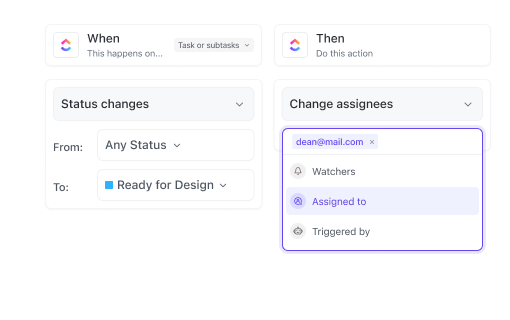
- Automated incident tracking with audit trails
- Defined ownership with real-time team collaboration
- Scheduled reminders and synced calendars for all compliance dates
- Searchable documentation linked directly to tasks
Use Cases
How Task Management Software Empowers Information Security Checks
See how clear task tracking minimizes risks and streamlines compliance workflows.
#UseCase1
Consolidating Security Data Across Teams and Systems
Policies, logs, and audit reports stay centralized — ClickUp ties all files and notes to the right tasks, making retrieval effortless.
#UseCase2
Maintaining an Audit Trail for Compliance and Accountability
Regulatory standards demand traceability. ClickUp records every task update, comment, and attachment to ensure full transparency.
#UseCase3
Capturing Evolving Risk Assessments Without Losing Context
Security threats evolve rapidly, but ClickUp keeps feedback and assessments organized with comments, mentions, and version history.
#UseCase4
Preventing Protocol Deviations in Routine Security Checks
Templates, checklists, and dependencies in ClickUp ensure every security step is followed precisely and documented thoroughly.
#UseCase5
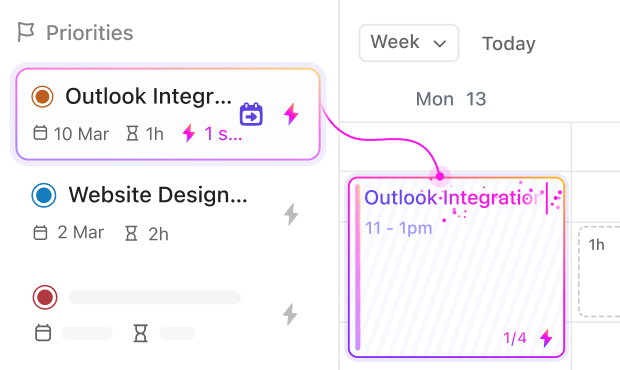
Tracking Regulatory Approvals and Compliance Deadlines
Multiple certifications and audits require vigilance; ClickUp’s workflows and reminders help you meet every requirement on time.
#UseCase6
Mapping Complex Incident Response Procedures
Incident handling workflows become clear and repeatable with task dependencies and statuses ensuring no step is overlooked.
#UseCase7
Avoiding Missed Security Audits and Reports
Managing multiple audits is challenging; ClickUp coordinates every checklist, report, and submission with timeline views and centralized files.
#UseCase8
Reducing Duplicate Efforts in Vulnerability Assessments
ClickUp tracks every scan and assessment as tasks with tags and notes, so teams avoid redundant work and share insights instantly.
#UseCase9
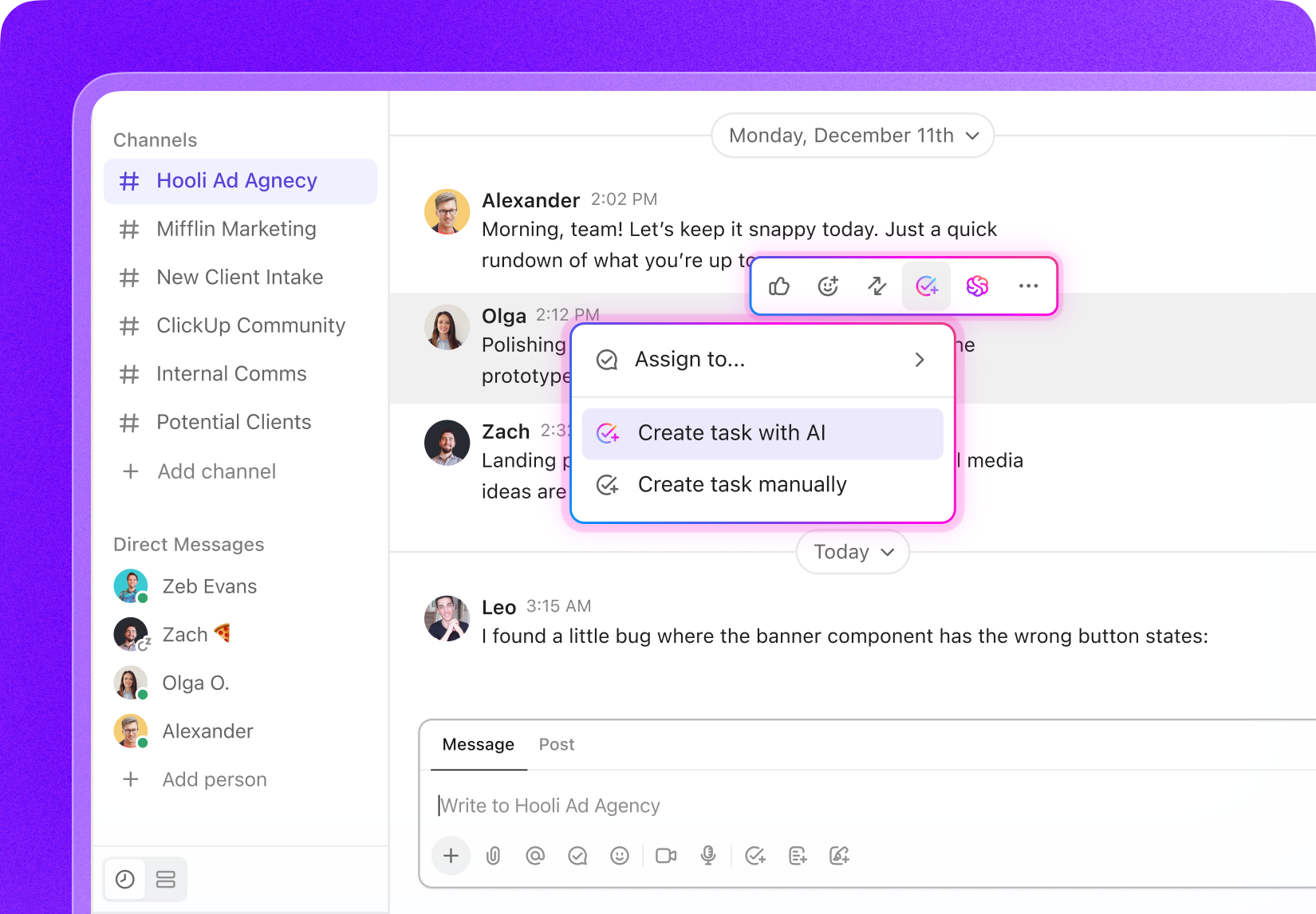
Transforming Security Meetings into Clear Action Plans
Discussions turn into assigned tasks with owners, deadlines, and checklists — ensuring follow-ups are always completed.
Key Beneficiaries
Who Benefits Most from ClickUp in Information Security
For security teams seeking a unified platform to manage every aspect of compliance and risk.
If you’re a Security Analyst
Stay ahead of vulnerabilities, track remediation tasks, and maintain compliance without juggling multiple tools.
If you’re a Compliance Officer
Organize audit schedules, monitor regulatory requirements, and ensure timely submissions with clear workflows.
If you’re part of a Cybersecurity Team
Coordinate incident responses, share updates in real-time, and maintain consistent security protocols across your organization.
How ClickUp Supports
How ClickUp Streamlines Information Security Checks
Manage audits, incidents, and policies without switching between tools.
Centralize Everything
Store literature, datasets, protocols, drafts, and grant docs in one workspace — no more scattered files.
Plan Research in Phases
Break projects into proposal, literature review, experiments, analysis, and writing with task lists and Gantt timelines.
Standardize Experiments & Fieldwork
Use templates and checklists for repeatable, error-free lab or field procedures.
Collaborate Across Teams
Assign tasks to co-authors, lab members, or collaborators. Shared boards and dashboards keep everyone aligned.
Turn Meetings Into Actionable Tasks
Convert supervisor or lab meetings into tasks with owners, checklists, and deadlines.
Stay on Top of Deadlines & Funding
Track grants, conferences, and submissions with automated reminders and calendars.