Strategies to Attract Clients for Cybersecurity Consultants
Centralize prospect tracking, outreach, engagements, and follow-ups in one streamlined system.
No credit card.
Identifying Obstacles in Cybersecurity Client Acquisition
Winning clients in cybersecurity seldom fails due to expertise alone. The breakdown happens when lead management, outreach, and onboarding processes are fragmented across multiple tools.
Common pitfalls include:
- No unified client pipeline: Leads scattered across LinkedIn, referrals, and emails remain untracked
- Inconsistent communication: Varied messaging and follow-ups per prospect
- Lost opportunities: Security inquiries lost amid scattered DMs, forms, and emails
- Delayed responses: Project workload hinders prompt client engagement
- Unclear prioritization: Difficulty distinguishing high-risk or high-value prospects
- Overwhelming content demands: Struggling to maintain thought leadership without a plan
- Manual administrative tasks: Contracts, compliance documents, and scheduling disconnected
- Scaling inefficiencies: Growing inquiries escalate chaos without repeatable workflows
Many cybersecurity consultants centralize client acquisition workflows so leads, tasks, conversations, and deadlines stay interconnected.
Comparing Traditional Cybersecurity Client Workflows to ClickUp
Expanding channels for outreach means more complexity to manage.
Traditional Approaches
- Leads scattered across LinkedIn, email, and contact forms
- Manual follow-ups and inconsistent reminders
- Lack of insight into client engagement stages
- Randomly planned content marketing
- Client data dispersed in multiple documents
- Difficulty prioritizing prospects effectively
- Missed deadlines and compliance requirements
- Switching between various apps slows productivity
How ClickUp Transforms the Process
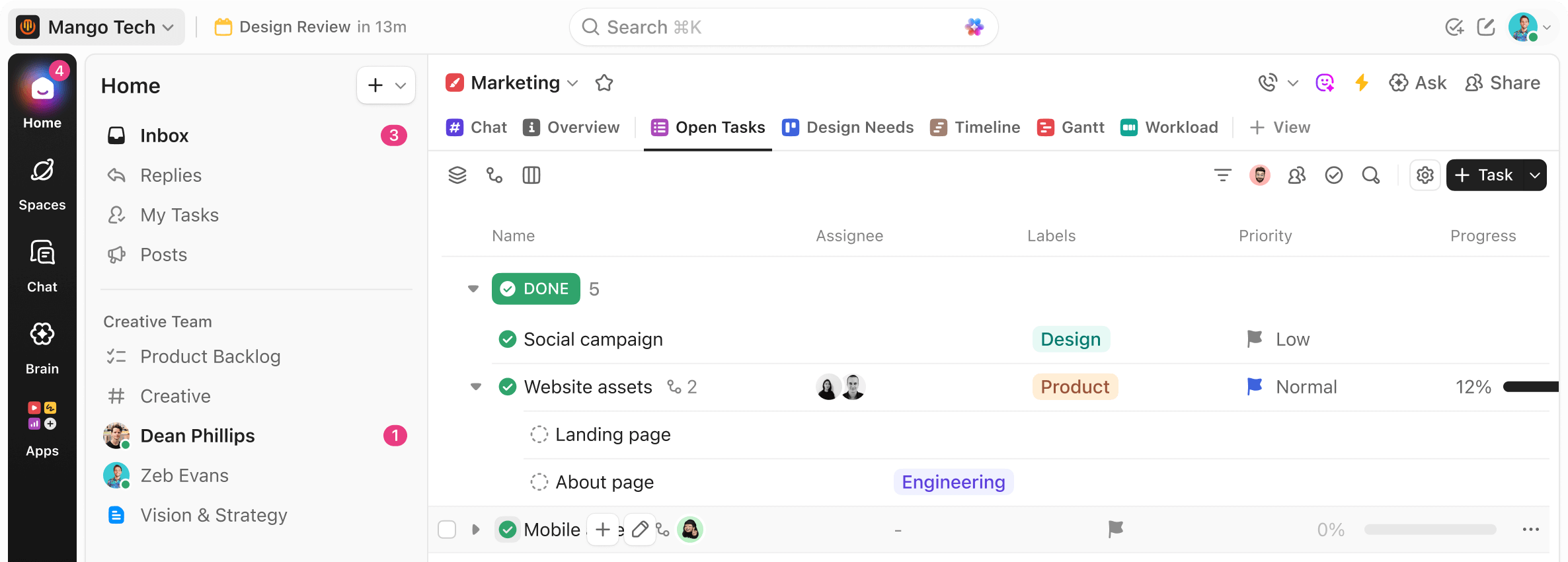
- Consolidate all client inquiries within one workspace
- Automate follow-ups and task assignments through workflows
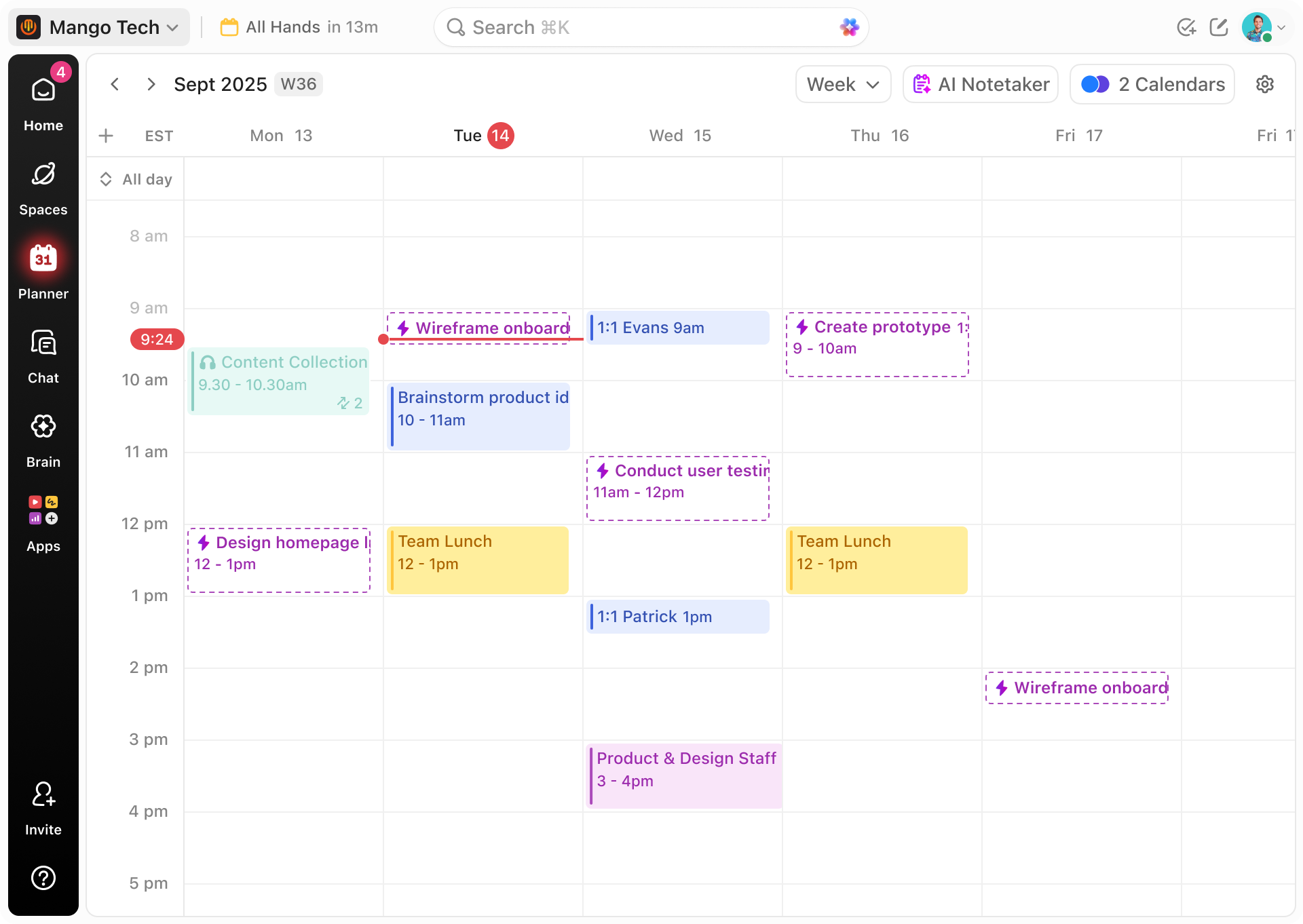
- Visualize leads with List, Board, or CRM-style views
- Schedule content and outreach campaigns seamlessly
- Store contracts, audit reports, and project files within tasks
- Tag prospects by industry, compliance needs, or urgency
- Set dependencies, reminders, and project timelines
- Collaborate and track engagements in a single platform
Building a Cybersecurity Client Pipeline That Delivers Results
Implement a systematic approach to convert security inquiries into retained clients.
Map Your Client Acquisition Channels
- Identify sources: LinkedIn, referrals, conferences, or security marketplaces
- Develop Docs for service offerings, compliance packages, and outreach templates
- Convert lead sources into trackable workflows
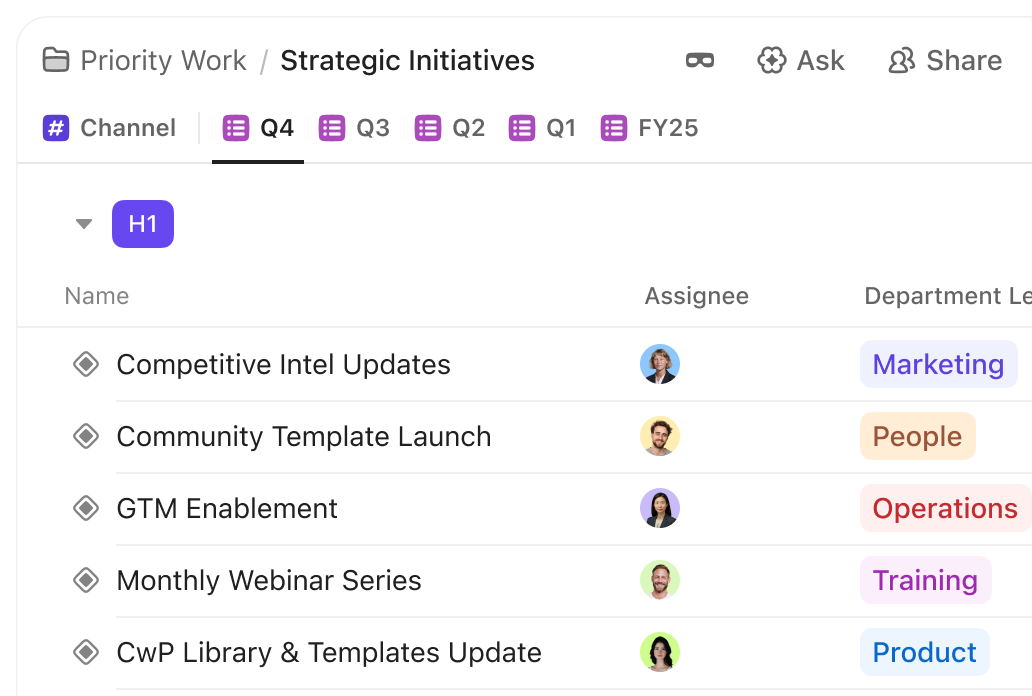
Establish a Consistent Lead Pipeline
- Save and reuse workflows for incoming prospects
- Automate follow-up tasks and responses
- Define stages like Lead → Assessment → Proposal → Engagement
Design Targeted Marketing Campaigns
- Schedule webinars, whitepapers, or email campaigns in calendar views
- Coordinate promotions without disjointed tracking
- Analyze which channels yield quality leads
Maintain Outreach Context and Continuity
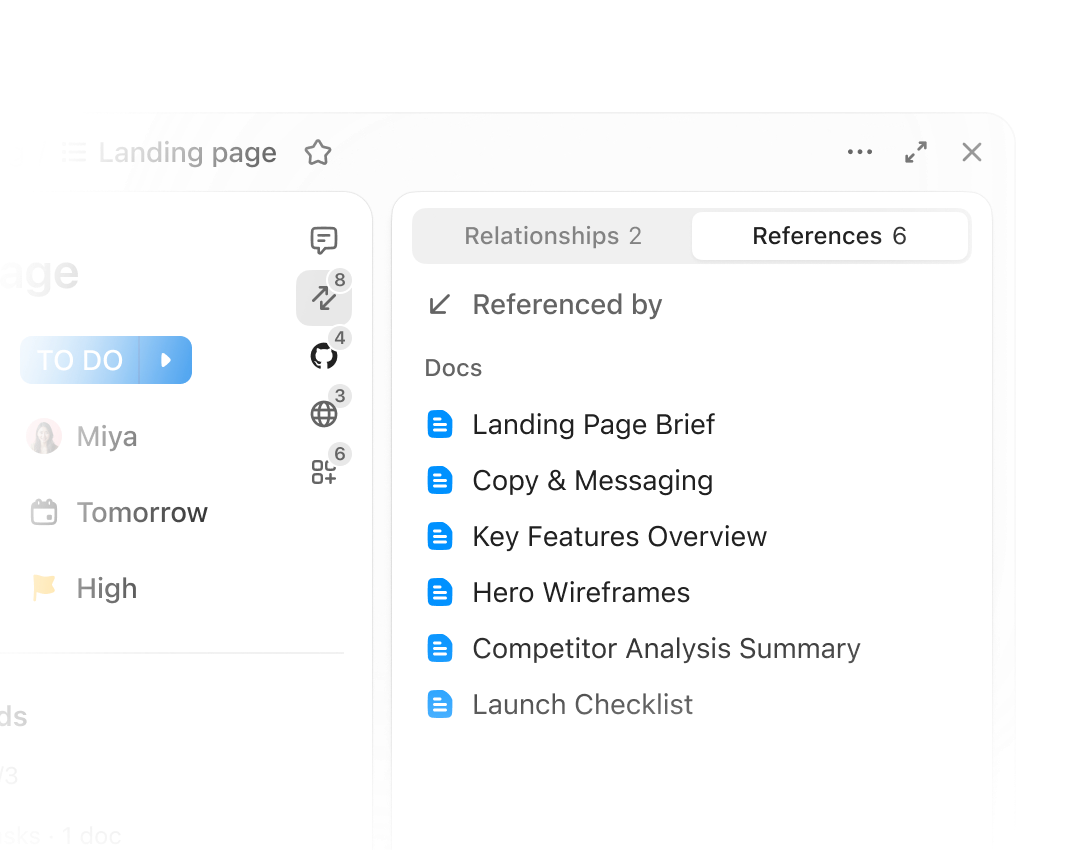
- Attach audit summaries, compliance checklists, and client notes to tasks
- Assign follow-ups and deadlines
- Keep conversations centralized and accessible
Streamline Client Onboarding Processes
- Automate workflow creation upon new inquiry submissions
- Centralize contracts, project plans, and deliverables
- Minimize redundant communications
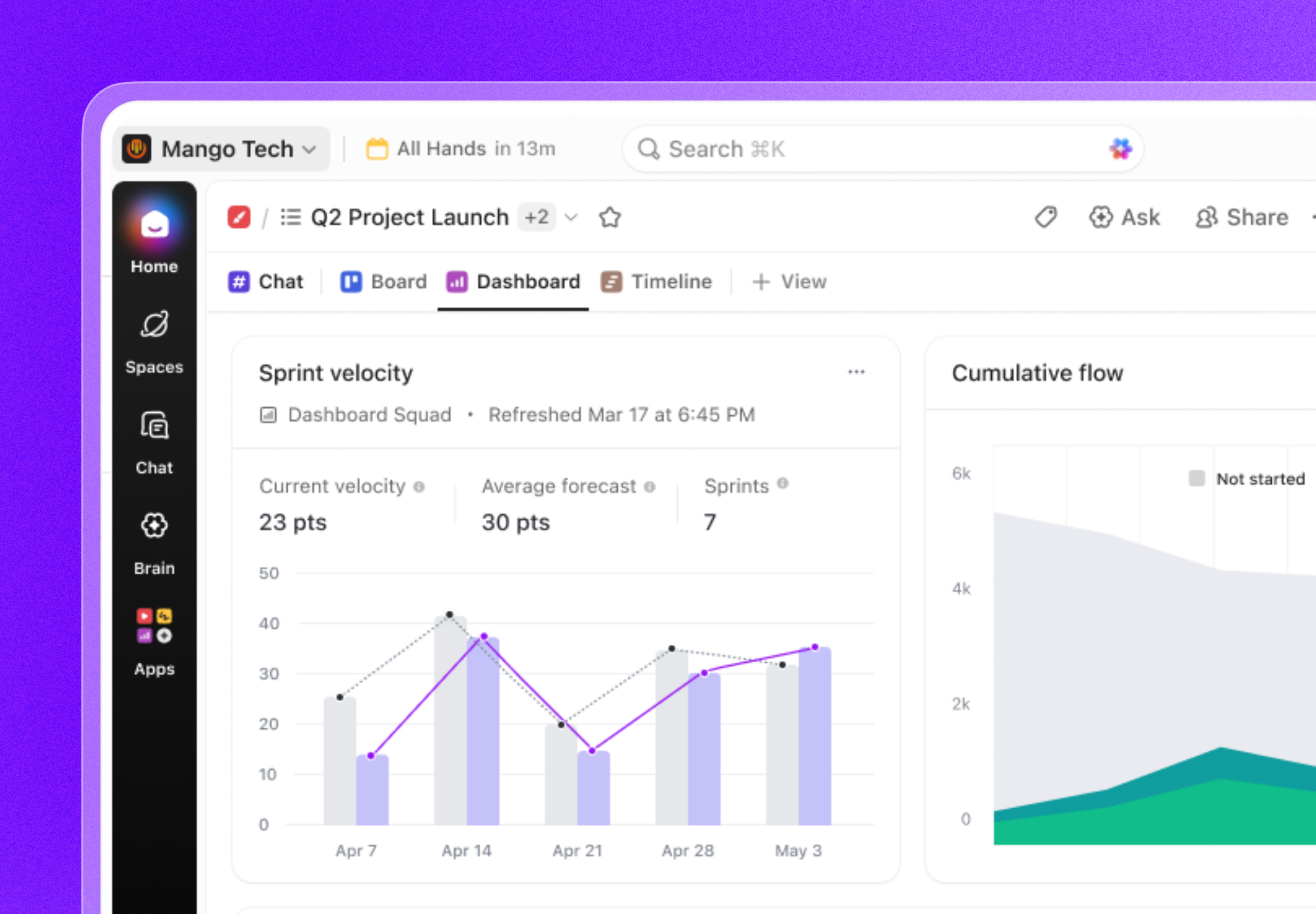
Monitor Pipeline Performance with Dashboards
- Track lead volume and conversion rates
- Visualize project milestones and deadlines
- Identify effective client acquisition strategies
Convert Prospects into Cybersecurity Engagements
Who Gains from a Cybersecurity Client Pipeline
Independent Cybersecurity Consultants
Managing assessments, reporting, and outreach solo can disrupt steady client growth.
- Capture leads via Forms → Auto-generate tasks
- Schedule marketing efforts → Plan social posts and newsletters
- Leverage AI-powered content generation with Brain → Save time on proposals
- Link audit reports, contracts, and notes to clients
- Track inquiries visually from initial contact to project completion
Small Cybersecurity Teams or Firms
- Coordinating multiple consultants handling assessments, remediation, and marketing introduces communication challenges.
- Assign owners for leads and follow-ups
- Collaborate on proposals, compliance documentation, and approvals
- Manage shared calendars and project deadlines
- Centralize client communications and documentation
How ClickUp Empowers Cybersecurity Consultants to Close Deals
Plan with Docs
Manage Leads Through Tasks
Track prospect status, consultations, and contract stages with clear ownership and timelines.
Accelerate Content Creation with Brain
Visualize Progress with Custom Views
Toggle between List, Board, Calendar, or Timeline to oversee projects and campaigns.
Collaborate Using Forms and Comments
Automatically collect inquiries and centralize feedback within workflows.
Monitor Metrics with Dashboards
Track client acquisition progress, campaign effectiveness, and upcoming deliverables in real time.
Common Questions on Securing Cybersecurity Clients
Centralize Cybersecurity Client Management