Zero Trust Architecture Knowledge Hub
Streamline Your Zero Trust Architecture Knowledge Base
Centralize all policies, protocols, network segments, and security controls into one accessible, searchable resource—ensuring your team always operates with the latest zero trust insights.
Trusted by the best
ClickUp vs Traditional Security Tools
Elevate Your Zero Trust Knowledge Management with ClickUp
Unite security knowledge and workflows in a single adaptable platform.
With traditional tools
- Security policies scattered across disconnected systems
- Manual updates prone to delays and errors
- Limited integration with security operations
- Fragmented access controls requiring duplicate content
- Time-intensive documentation processes without automation
With ClickUp
- Centralized Docs linked directly to security tasks and alerts
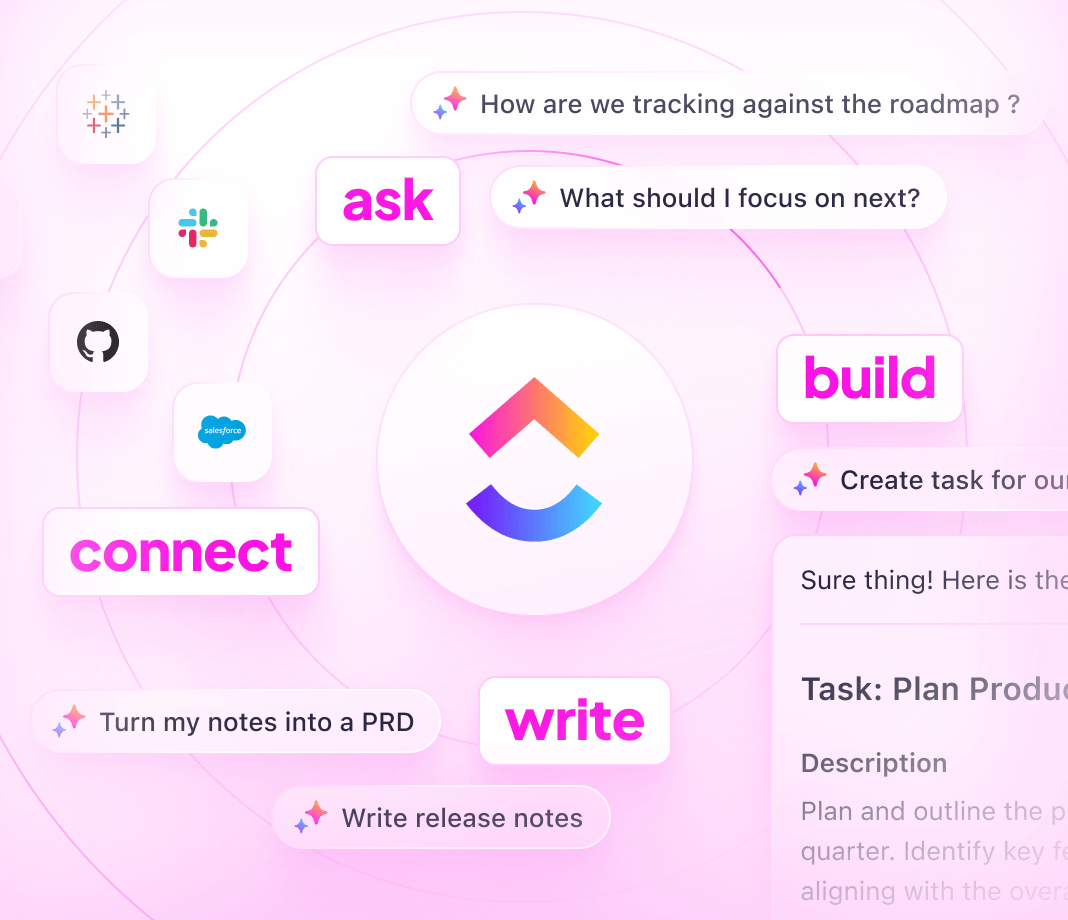
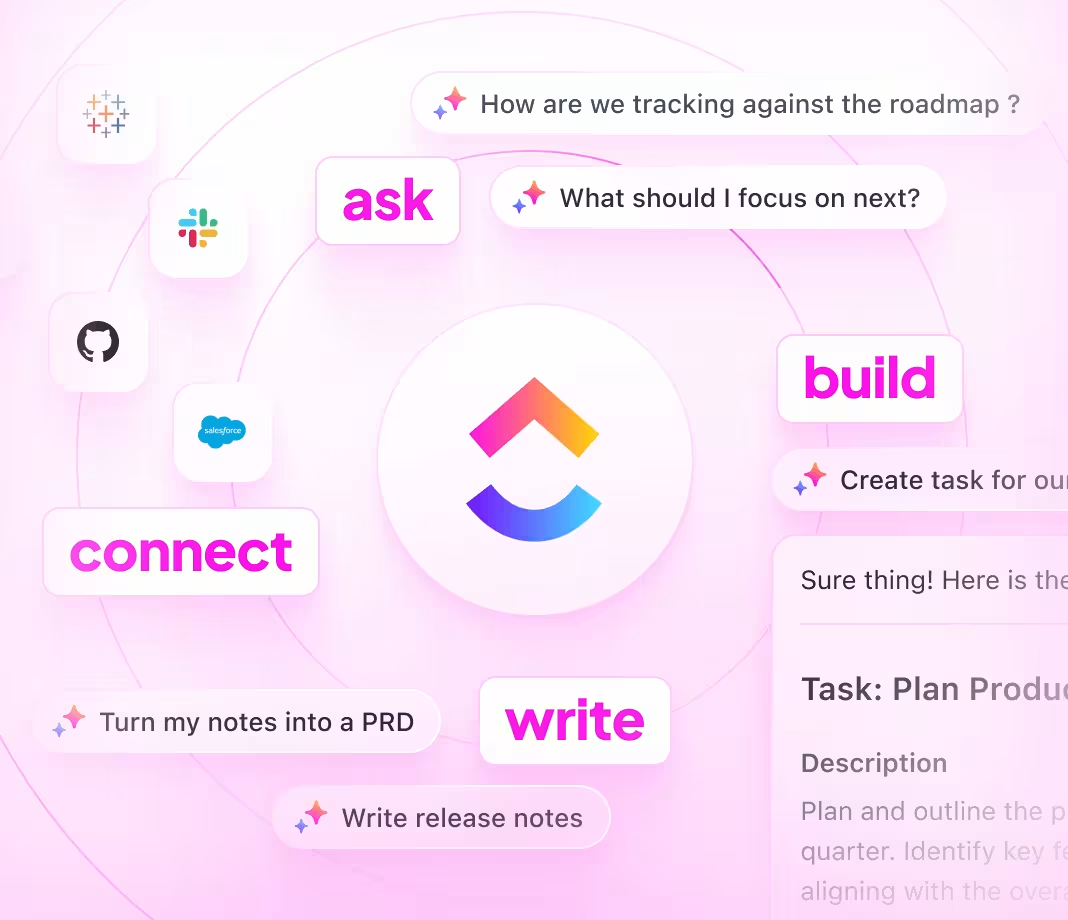
- Automated updates powered by ClickUp Brain AI
- Real-time syncing with security operations and incident management
- Granular permissions for internal, partner, and external stakeholders
- Streamlined workflows accelerating knowledge updates
Building Your Knowledge Base
Transform Your Zero Trust Architecture Knowledge Base in 6 Steps
Follow these steps to create a dynamic, authoritative resource for your zero trust framework.
1. Identify stakeholders and define zero trust objectives
- Determine who needs access (security teams, IT, partners)
- Clarify goals for compliance, threat mitigation, and monitoring
- Assign clear ownership for ongoing content management
2. Design an intuitive knowledge base structure
- Organize content into core domains: Identity, Device Security, Network Segmentation, Access Controls
- Include compliance standards, policy updates, and incident procedures
- Ensure easy navigation with table of contents and subpages
3. Standardize documentation templates across controls
- Use consistent formats for policies, configurations, and workflows
- Detail purpose, implementation steps, monitoring, and exceptions
- Document failure modes and remediation processes
4. Incorporate practical guides and threat response protocols
- Develop step-by-step instructions for security operations
- Include troubleshooting for common zero trust challenges
- Centralize incident response playbooks and escalation paths
5. Keep knowledge base current by linking to change management
- Connect documentation updates to network changes, audits, and security incidents
- Integrate with ClickUp 4.0 workflows for seamless updates
- Treat knowledge refresh as part of operational cadence
6. Implement access controls and continuous review cycles
- Set role-based permissions for sensitive content
- Schedule regular audits and feedback collection
- Use Brain Max to surface outdated or incomplete documentation
Harness ClickUp for Zero Trust Success
Unlock ClickUp’s Power to Build Your Zero Trust Knowledge Base
Centralize policies, automate updates, and align security operations with cutting-edge AI support.
Organize
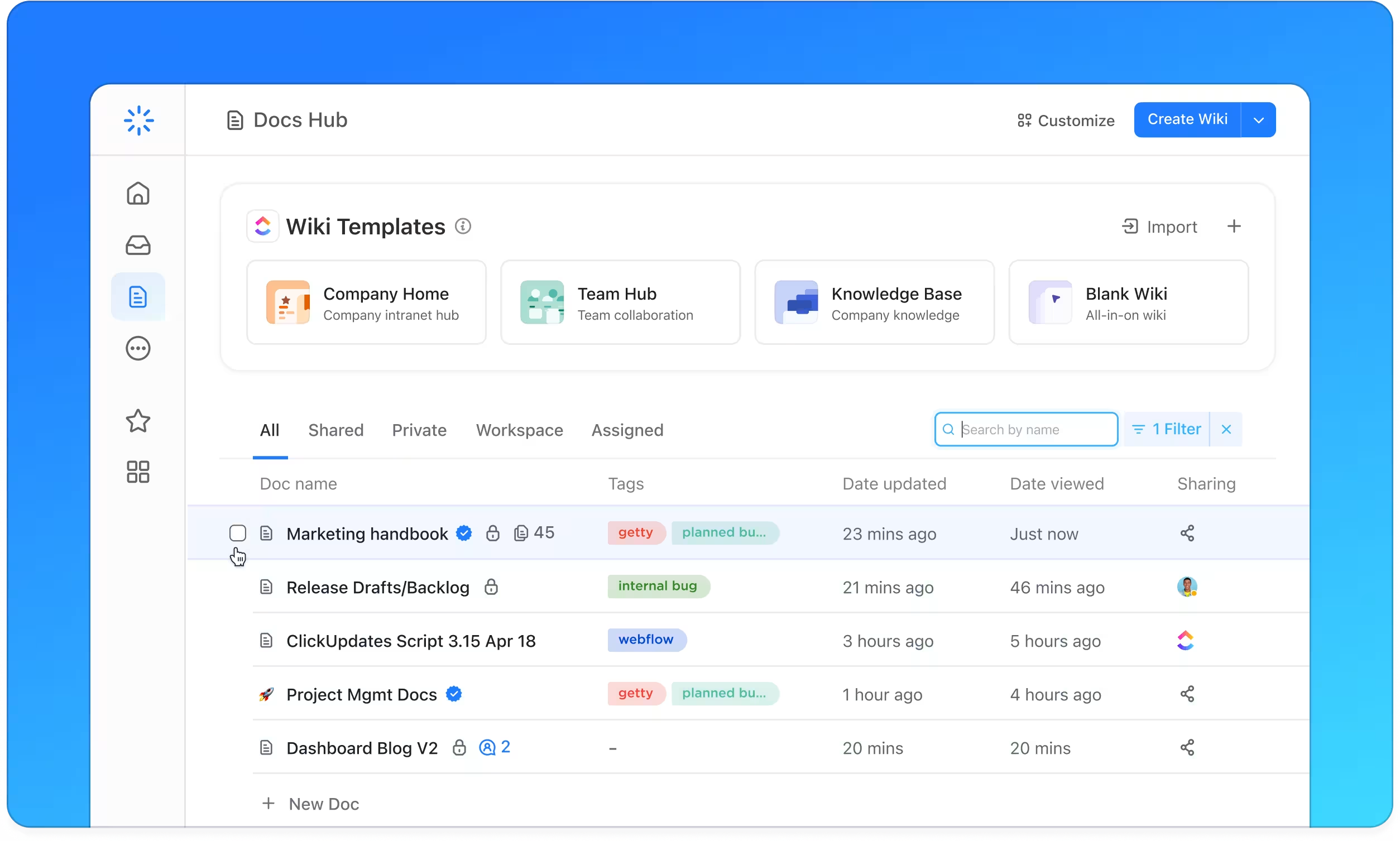
Structured Zero Trust Documentation with ClickUp Docs
- Identity and Access Management, Device Security, Network Segmentation, Monitoring
- Hierarchical navigation with clear tables of contents
- Consistent templates for policies and procedures
Why it matters: Your team finds critical security info fast, reducing incident response times.
Accountability
Assign and Track Ownership Seamlessly
- Convert gaps into actionable tasks
- Assign clear owners with due dates and review cycles
- Track documentation work alongside security projects
Why it matters: Continuous ownership ensures your zero trust knowledge base never falls behind.
Integration
Connect Documentation to Security Operations
- Link docs to network changes, audits, and incident tickets
- Use ClickUp 4.0 workflows to automate updates
- Tie feedback and alerts directly to documentation
Why it matters: Your knowledge base evolves in real-time with your security environment.
Zero Trust Knowledge Base FAQs