Secrets Management Knowledge Hub
Elevate Your Secrets Management with a Centralized Knowledge Base
Create a unified, searchable destination for your secrets workflows—covering access controls, rotation policies, audit trails, and incident responses—so your team always accesses the most current security protocols.
Trusted by the best
ClickUp vs Traditional Tools
Why ClickUp Transforms Secrets Management Knowledge Bases
Unify security knowledge and operational workflows effortlessly.
Traditional Secrets Management Tools
- Documentation scattered and disconnected from daily operations
- Manual updates prone to errors and outdated information
- Limited visibility into secrets lifecycle and access changes
- Rigid permissions causing duplication and confusion
- Time-intensive creation and maintenance processes
Using ClickUp for Secrets Management
- Integrates knowledge with execution: Docs, tasks, comments in one place
- Automate gaps into actionable tasks with clear ownership
- Link secrets documentation directly to workflows and incidents
- Granular access controls for internal teams and external partners
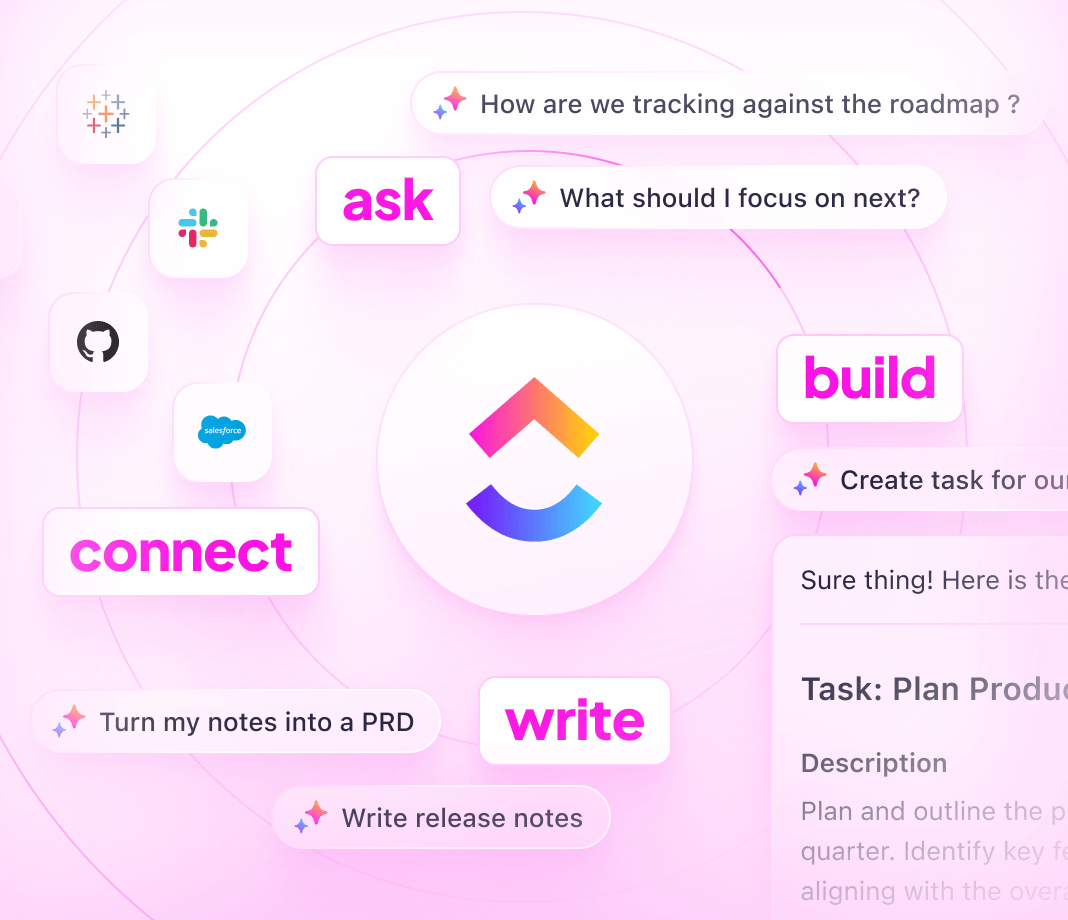
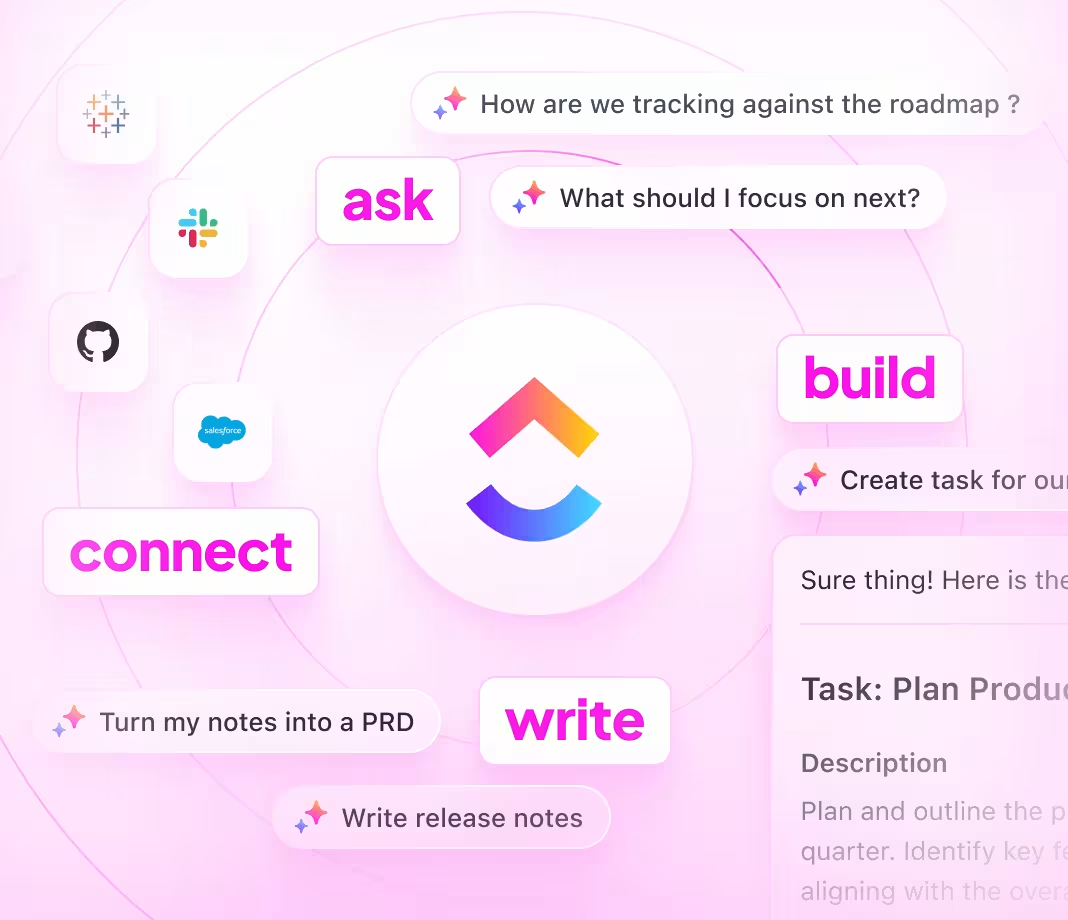
- AI-powered assistance accelerates drafting, summarization, and troubleshooting
Blueprint for Your Knowledge Base
How to Construct a Secrets Management Knowledge Base
Follow these 6 steps to build a secure, scalable, and maintainable resource.
1. Identify your users and define security documentation objectives
- Determine stakeholders: DevOps, security, compliance teams
- Outline workflows from secret creation to revocation and audit
- Assign documentation owners to ensure continuity
2. Design a clear, intuitive knowledge base hierarchy
- Centralize secrets policies, rotation schedules, incident logs, and access controls
- Organize by environment, system, and risk level
- Provide easy navigation with tables of contents and subpages
3. Standardize workflow documentation for consistency
- Use uniform templates for secrets management processes
- Include responsibilities, tools used, and security checks
- Document exception handling and emergency procedures
4. Incorporate practical guides and incident response protocols
- Develop step-by-step guides for onboarding, rotation, and audits
- Embed troubleshooting advice for common access issues
- Maintain a knowledge base of past incidents and resolutions
5. Keep documentation current by linking to operational changes
- Connect docs to deployment releases, access updates, and security audits
- Treat documentation updates as part of your security lifecycle
- Use ClickUp Brain to identify and fill knowledge gaps automatically
6. Enforce access controls and ongoing review processes
- Set role-based permissions for sensitive information
- Schedule regular reviews and update cycles
- Leverage Brain Max for proactive knowledge base optimization
ClickUp Knowledge Base Advantage
Unlock the Power of ClickUp for Secrets Management Knowledge
Keep your secrets documentation accurate, authorized, and aligned with every operational update.
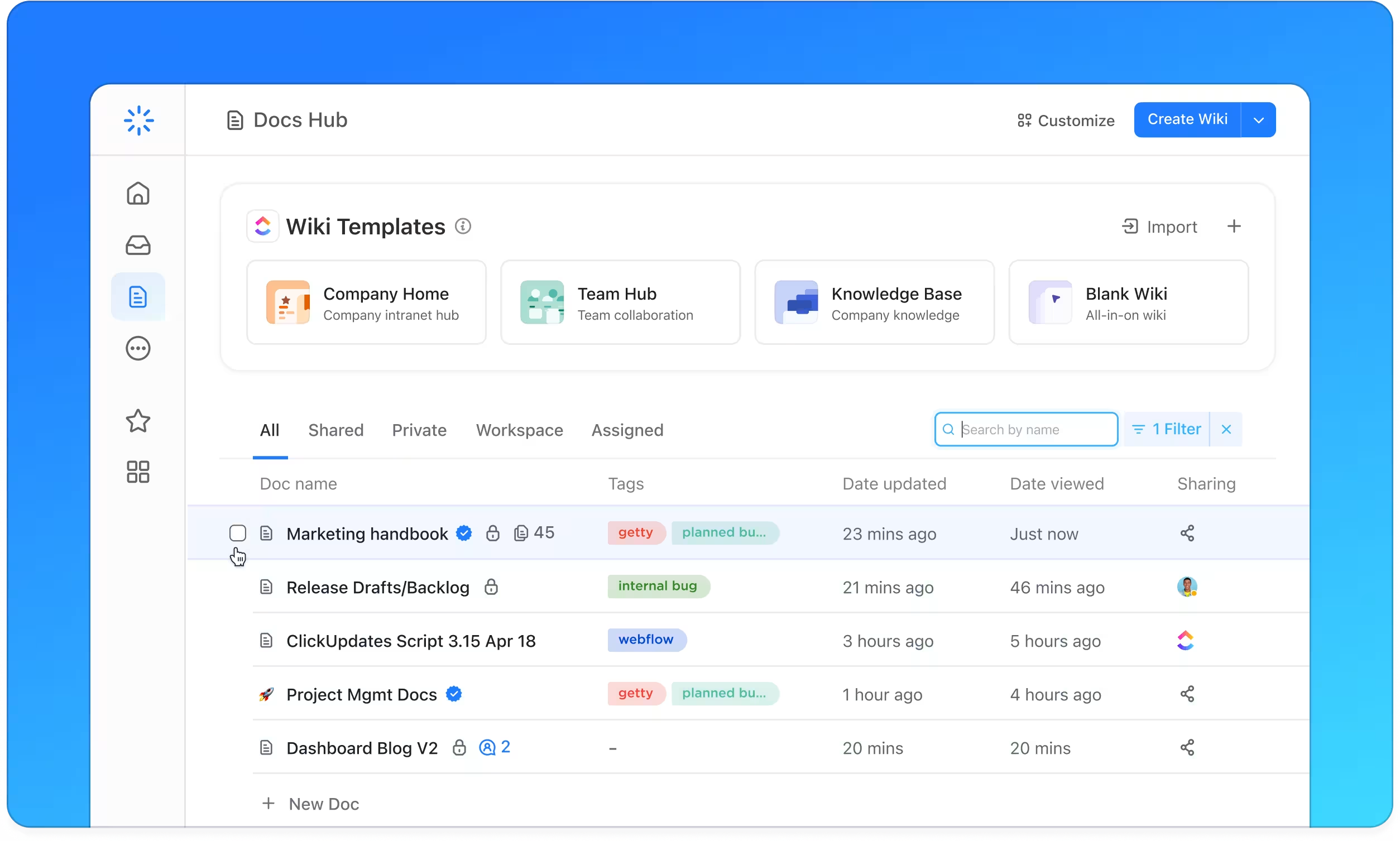
Organize
Structured Secrets Management Documentation with ClickUp Docs
- Policies, Access Controls, Rotation Procedures, Incident Reports
- Table of contents with nested pages for quick reference
- Consistent formatting for all workflow documents
Why it matters: Your team finds critical security info swiftly, reducing risk and downtime.
Manage
Accountable Documentation with Trackable Ownership
- Convert documentation gaps into assigned tasks
- Set owners, deadlines, and periodic review reminders
- Monitor documentation progress alongside operational tasks
Why it matters: Your knowledge base remains up to date because responsibility is clear.
Integrate
Documentation Linked to Secrets Management Workflows
- Connect docs to secrets rotation schedules, audit findings, and incident responses
- Tie updates to operational changes and compliance requirements
- Incorporate user feedback and support insights
Why it matters: Documentation evolves in step with your security environment.
ClickUp Secrets Management Knowledge Base