Construct a Robust Knowledge Base for Encryption Key Management
Centralize all critical information about encryption keys, policies, rotation schedules, and access controls in one searchable, secure location—empowering your security team with the latest insights and protocols.
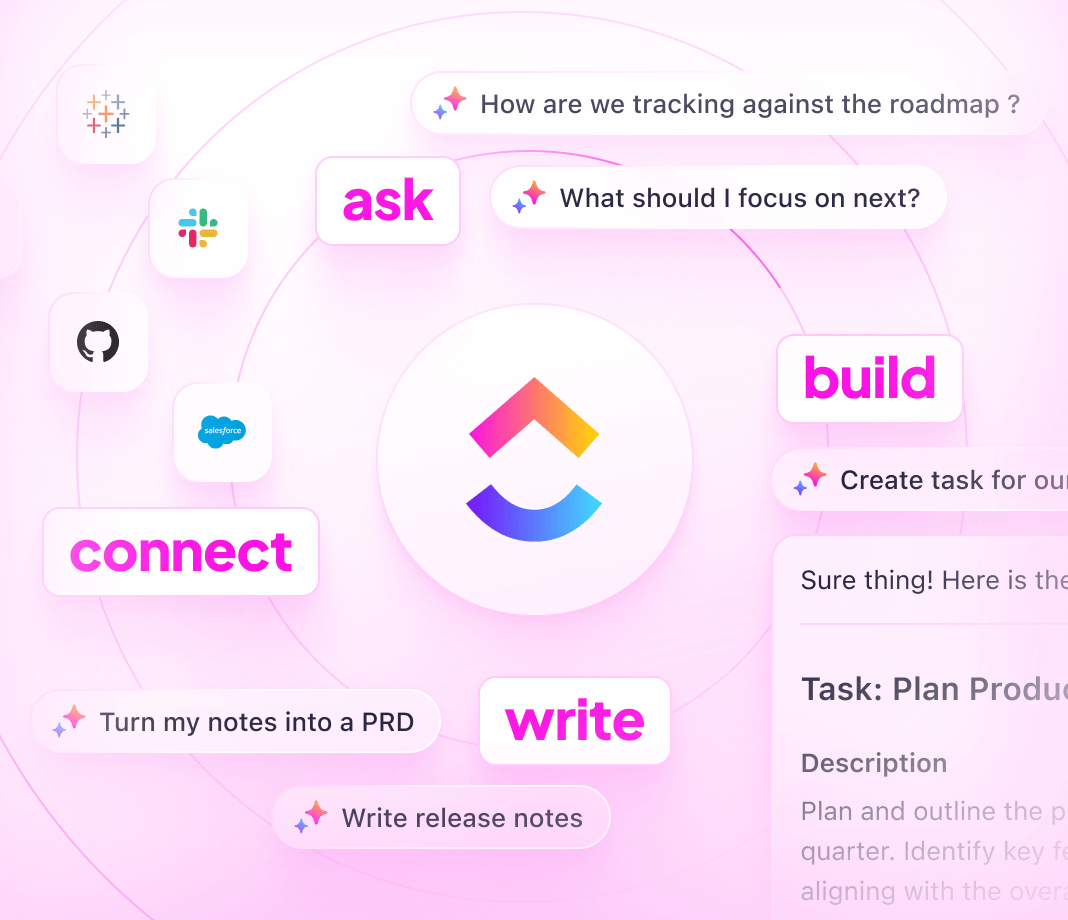
How ClickUp Elevates Encryption Key Management Knowledge Bases
Unify knowledge and action within a scalable platform designed for security teams.
Traditional approaches
- Key management info scattered across emails and isolated docs
- Manual updates lead to outdated procedures
- Lack of integration with operational workflows
- Permission controls are rigid and duplicative
- Entirely manual processes increase risk and delay
Using ClickUp
- Combine documentation, tasks, and communications in one platform
- Turn gaps in knowledge into actionable tasks automatically
- Link knowledge base entries with key rotation and incident tasks
- Fine-tune access permissions for teams, partners, and auditors
- Leverage ClickUp Brain AI for smart drafting, summarization, and troubleshooting
Steps to Develop an Encryption Key Management Knowledge Base
Follow these 6 steps to build a secure, maintainable, and accessible repository for all key management documentation.
1. Identify stakeholders and key management objectives
- Determine who accesses and maintains encryption keys
- Define compliance and security standards to cover
- Assign ownership for continuous documentation updates
2. Design a clear, logical knowledge base hierarchy
- Create sections for key policies, rotation schedules, access controls, and audit logs
- Use intuitive navigation for quick information retrieval
- Include changelogs for tracking procedural updates
3. Standardize document templates for key management processes
- Develop uniform formats for key lifecycle documentation
- Include critical elements: key purpose, generation method, usage guidelines, and revocation steps
- Detail error handling and incident response procedures
4. Incorporate practical guides and security best practices
- Publish how-to articles for key distribution and emergency rotations
- Add troubleshooting workflows for common key management issues
- Centralize compliance checklists and audit preparation materials
5. Maintain currency by linking documentation to operational events
- Connect updates to key rotation tasks, security incidents, and compliance audits
- Treat documentation as part of ongoing security operations
- Ensure the knowledge base evolves with your infrastructure
6. Control access and enforce review policies
- Set permissions for internal teams, external auditors, and partners
- Schedule periodic reviews and approval cycles
- Gather feedback to continuously improve documentation quality
Unlock Seamless Knowledge Management for Encryption Keys
Ensure your encryption key documentation stays organized, current, and integrated with your security workflows.
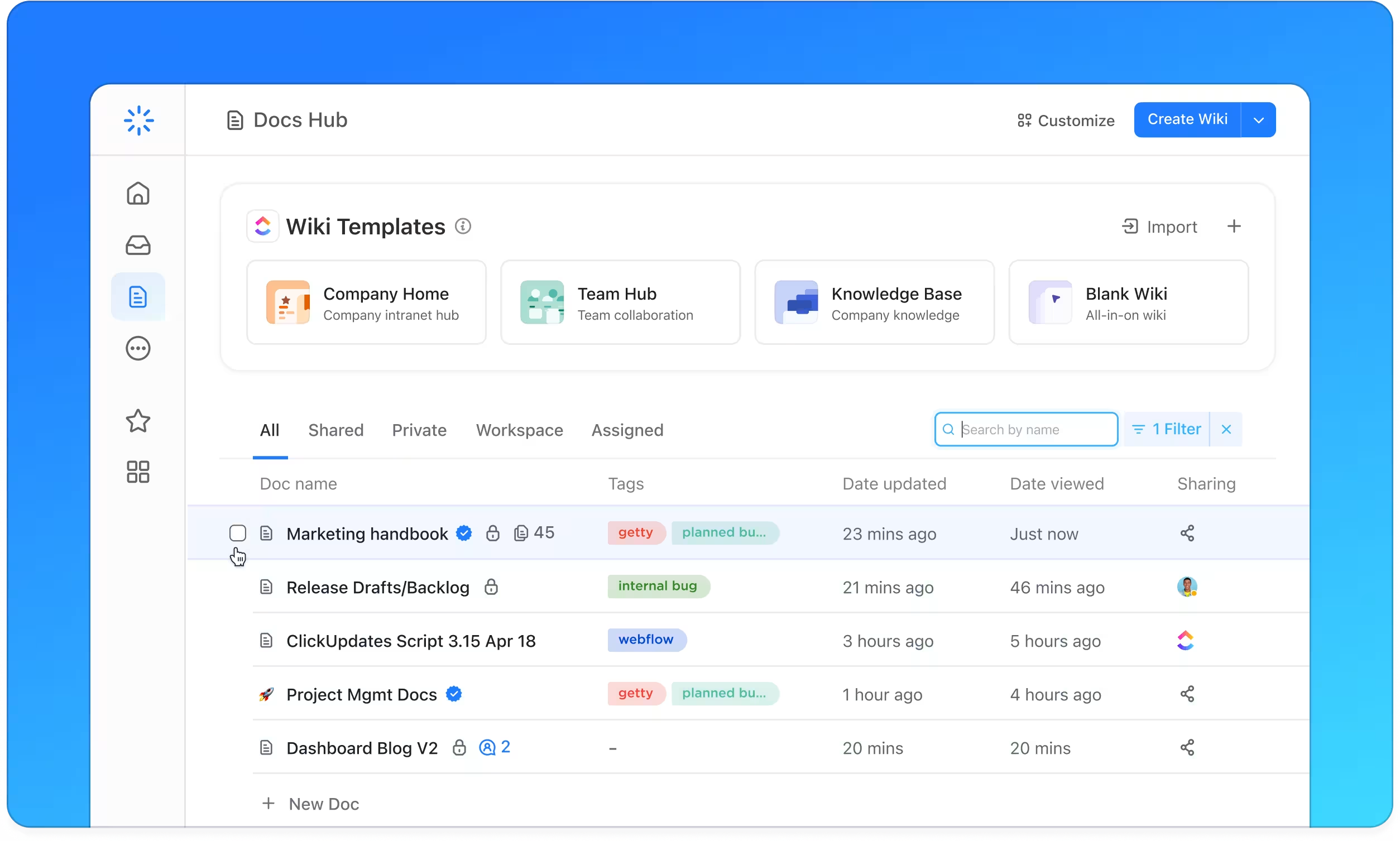
Comprehensive Key Management Documentation with ClickUp Docs
- Key policies, rotation plans, access roles, audit logs
- Table of contents and nested subpages for effortless browsing
- Consistent document formats across all key types
Why it matters: Security teams quickly locate critical info, reducing errors and delays.
Clear Ownership and Accountability Tracking
- Transform knowledge gaps into actionable tasks
- Assign document owners with deadlines and review schedules
- Manage documentation updates like operational projects
Why it matters: Documentation accuracy is maintained through defined responsibilities.
Documentation Aligned with Security Operations
- Link docs to key rotation cycles, incident responses, and audit activities
- Connect findings from security reviews and postmortems
- Integrate user feedback and support tickets into knowledge base updates
Why it matters: Keeps procedures relevant and aligned with evolving security needs.