Cybersecurity Threat Intelligence Hub
Build a Centralized Knowledge Base for Cybersecurity Threats
Create a comprehensive, searchable repository for threat indicators, attack vectors, mitigation strategies, and incident reports—so your security team stays ahead of emerging risks.
Trusted by the best
ClickUp vs Traditional Security Tools
Why ClickUp Transforms Cybersecurity Knowledge Management
Unify threat data and response workflows in one dynamic platform.
With traditional tools
- Threat intelligence scattered across disconnected platforms
- Manual updates lead to outdated or incomplete information
- Poor integration between knowledge and incident response
- Limited access controls force duplication and confusion
- Time-consuming documentation slows down security operations
With ClickUp
- Consolidate threat data, investigation tasks, and collaboration in one workspace
- Automate updates and link knowledge to live incidents
- Fine-grained permissions for internal teams and external partners
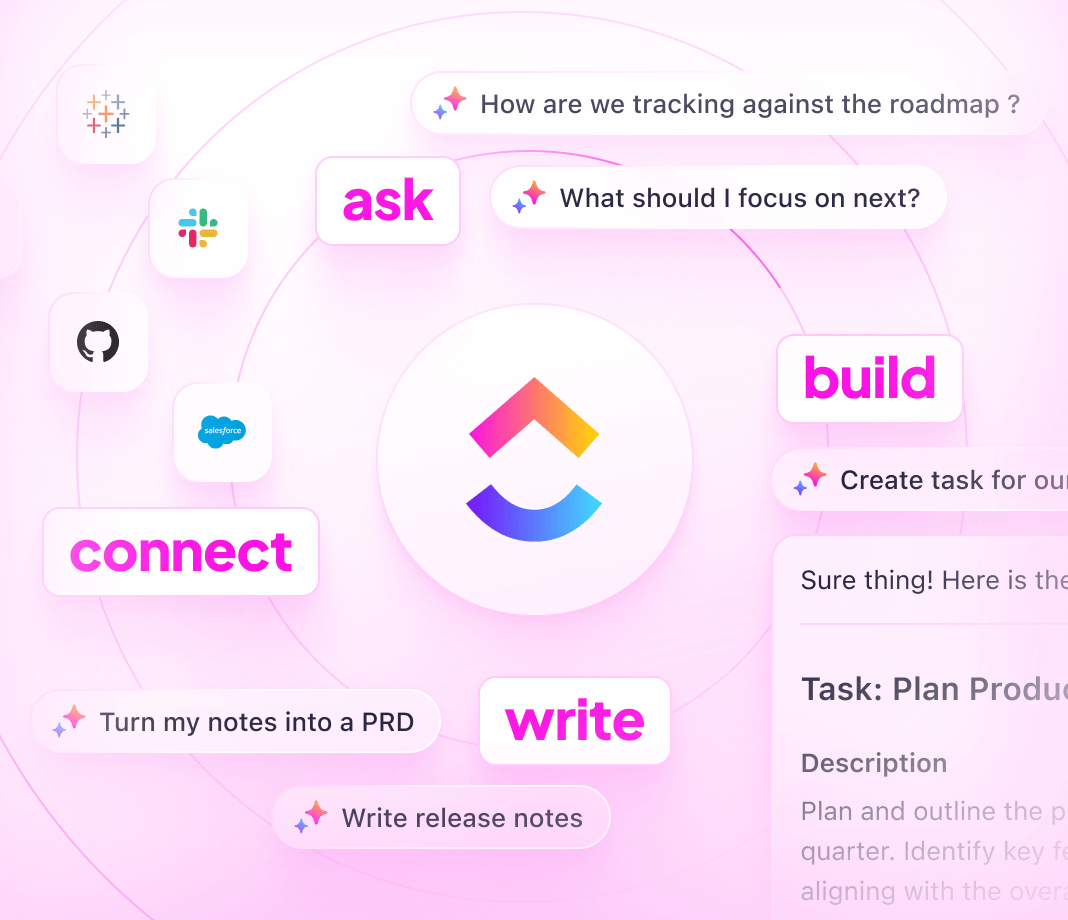
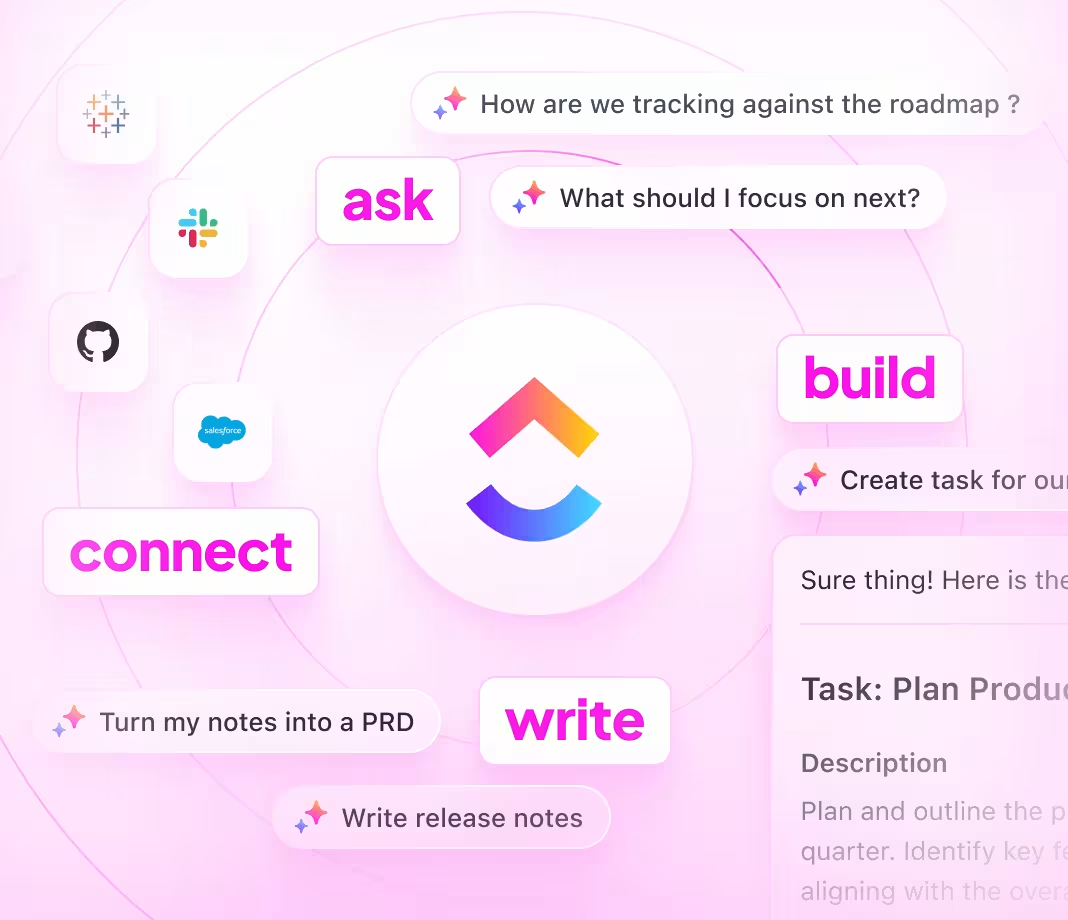
- Leverage ClickUp Brain, 4.0, and Brain Max for AI-driven insights and summaries
- Accelerate threat analysis and response with integrated tools
Building your cybersecurity knowledge base
How to establish a knowledge base for cybersecurity threats
Follow these 6 essential steps to create a resilient and actionable threat intelligence repository.
1. Identify stakeholders and define intelligence objectives
- Determine teams using the knowledge base: SOC, threat intel, incident response
- Clarify goals: detection, analysis, mitigation, compliance
- Assign ownership to maintain accuracy and relevance
2. Design a clear structure for cybersecurity threat data
- Develop sections for threat types, TTPs, indicators, vulnerabilities, and remediation
- Use nested pages and tags for quick navigation
- Ensure changelogs and update history are easy to access
3. Standardize threat entries for consistent analysis
- Adopt uniform templates covering threat description, tactics, affected assets, and references
- Include MITRE ATT&CK mappings and severity ratings
- Document detection methods and common indicators to reduce investigation time
4. Incorporate real incident reports and response playbooks
- Add detailed case studies and lessons learned
- Embed step-by-step response guides and escalation paths
- Centralize threat hunting procedures and detection rules
5. Keep knowledge base current by linking to live security events
- Connect documentation updates to ongoing incidents and vulnerability disclosures
- Treat knowledge updates as part of daily security operations
- Maintain accuracy as threat landscape evolves
6. Manage access and maintain continuous improvement
- Control permissions for internal teams and trusted partners
- Schedule regular reviews and incorporate feedback
- Use analytics to identify knowledge gaps and optimize content
Harness ClickUp's capabilities
How ClickUp supports building your cybersecurity threat knowledge base
Empower your security teams with structured, connected, and AI-enhanced knowledge management.
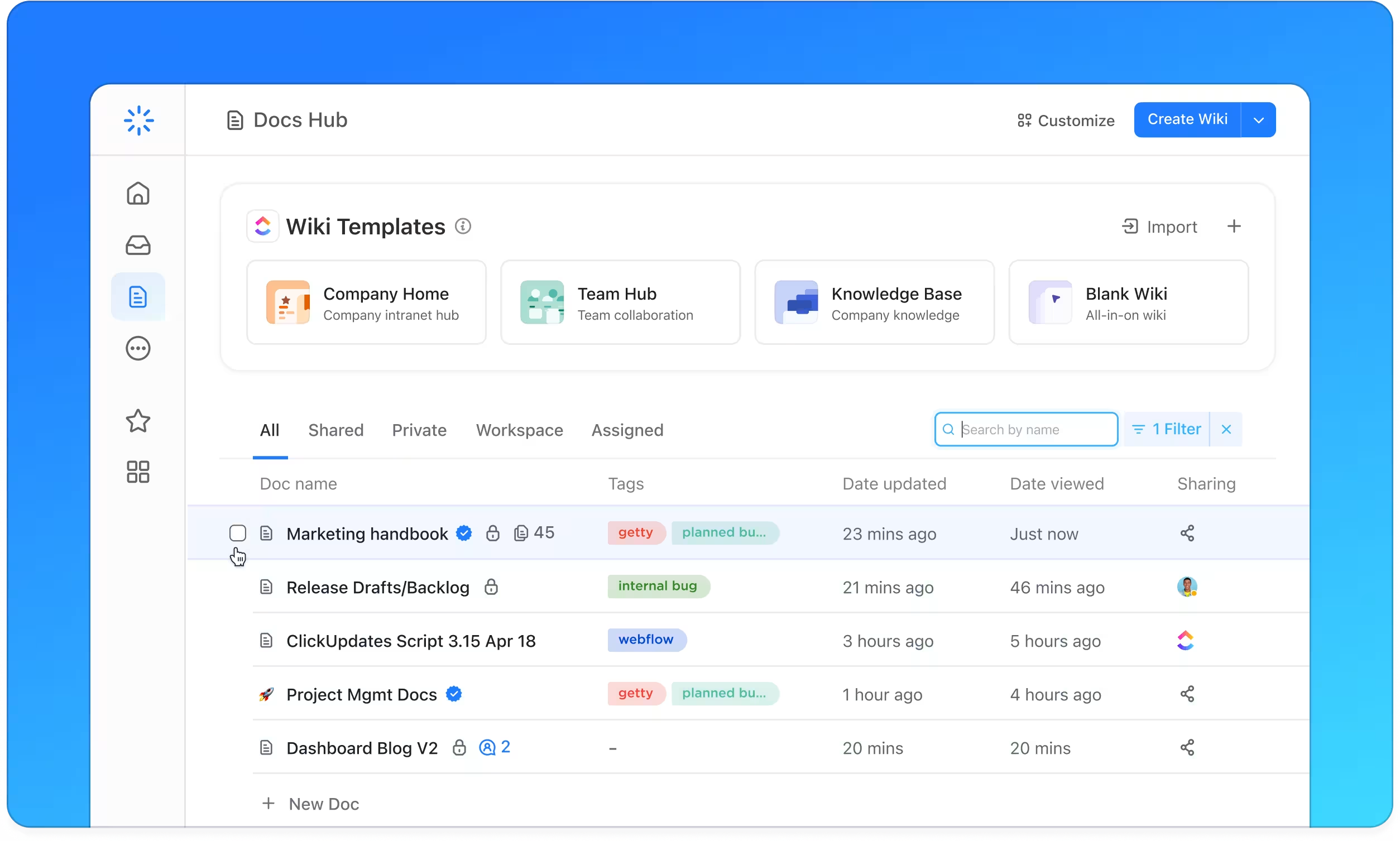
Organize
Structured threat intelligence with ClickUp Docs
- Categorize by threat actor, campaign, vulnerability, and mitigation
- Use nested pages and linked documents for intuitive navigation
- Standardize entries with templates including MITRE ATT&CK and CVE references
Why it matters: Analysts find critical information quickly, enabling faster incident detection and response.
Assign and track
Clear ownership and update cycles
- Convert intelligence gaps into tasks with due dates and assignees
- Schedule regular content reviews and audits
- Monitor progress within the same platform as security operations
Why it matters: Ensures knowledge stays accurate and actionable, reducing risk of outdated information.
Integrate
Connect documentation with active security workflows
- Link knowledge base entries to incident tickets, threat alerts, and remediation tasks
- Correlate intelligence updates with vulnerability disclosures and security patches
- Use AI features like Brain Max to auto-summarize incidents and generate threat briefs
Why it matters: Keeps your knowledge base dynamic and aligned with evolving threats and responses.
Cybersecurity Knowledge Base with ClickUp