ClickUp Authentication Workflow Knowledge Base
Build a Robust Knowledge Base for Authentication Workflows
Centralize your authentication protocols, token management, multi-factor setups, error handling, and troubleshooting—all in one searchable source of truth for your team.
Trusted by the best
ClickUp vs Traditional Tools
Why ClickUp is the smarter choice for authentication workflow documentation
Create a unified knowledge hub that evolves with your security needs.
With traditional tools
- Authentication info scattered across disconnected systems
- Manual updates lead to outdated or inconsistent procedures
- No direct link between workflows and security incidents
- Permission settings cause duplication and confusion
- Entirely manual creation and maintenance processes
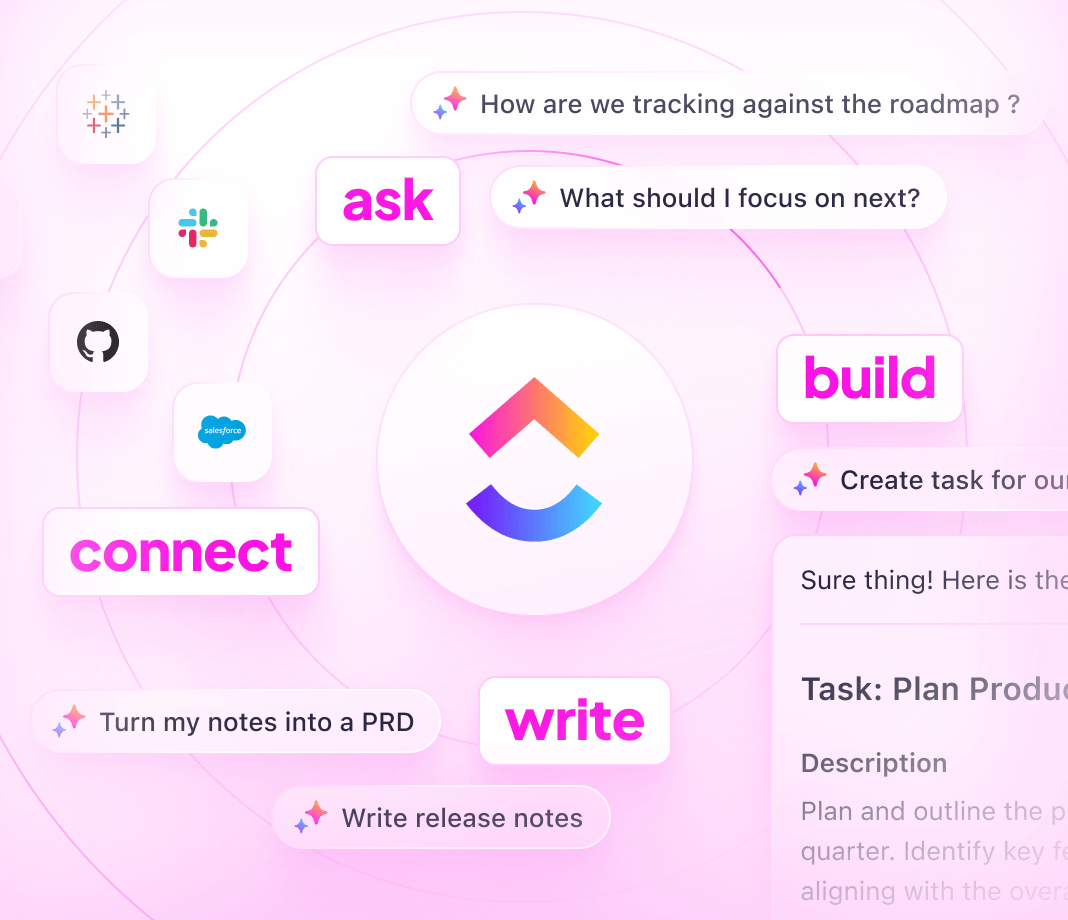
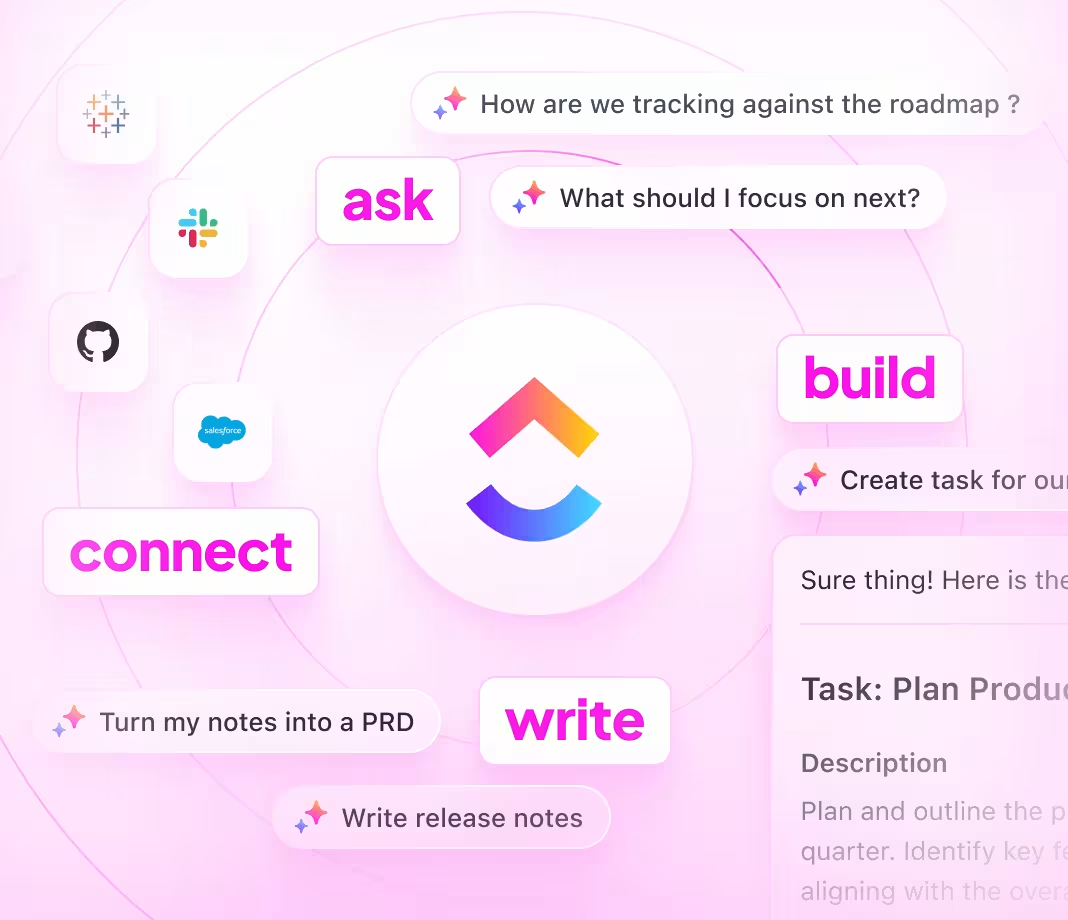
With ClickUp
- Integrate documentation with tasks and real-time collaboration
- Automatically convert documentation gaps into actionable tasks
- Link knowledge base entries directly to authentication workflows and incident reports
- Granular access controls for internal teams, partners, and public APIs
- AI-assisted drafting, summarization, and troubleshooting accelerate updates
Steps to create knowledge base
How to create a knowledge base for authentication workflows?
Follow this 6-step process to structure, maintain, and scale your authentication documentation.
1. Identify your audience and documentation objectives
- Determine who relies on authentication docs (developers, security teams, partners)
- Outline key workflows from login to token refresh and multi-factor authentication
- Assign ownership to ensure ongoing accuracy
2. Design a clear knowledge base layout
- Build a centralized hub with intuitive navigation
- Include core sections: authentication methods, token management, error codes, best practices
- Provide changelogs and update history prominently
3. Standardize authentication workflow pages
- Use consistent templates covering purpose, steps, security considerations, and examples
- Document error handling and edge cases to minimize support requests
4. Incorporate practical guides and troubleshooting content
- Add step-by-step how-tos for common authentication scenarios
- Detail troubleshooting processes for login failures and token errors
- Centralize configuration instructions and recovery procedures
5. Keep documentation current by linking to updates
- Connect knowledge base edits to workflow changes, security patches, and incident reports
- Treat documentation as an integral part of deployment cycles
- Ensure the knowledge base reflects the latest authentication standards
6. Manage access and review processes
- Set role-based permissions for internal teams, partners, and public access
- Regularly update changelogs and deprecation notices
- Collect feedback and schedule periodic reviews to maintain relevance
ClickUp Knowledge Base Benefits
Unlock streamlined knowledge management for authentication workflows
Maintain ownership, structure, and synchronization with every authentication update.
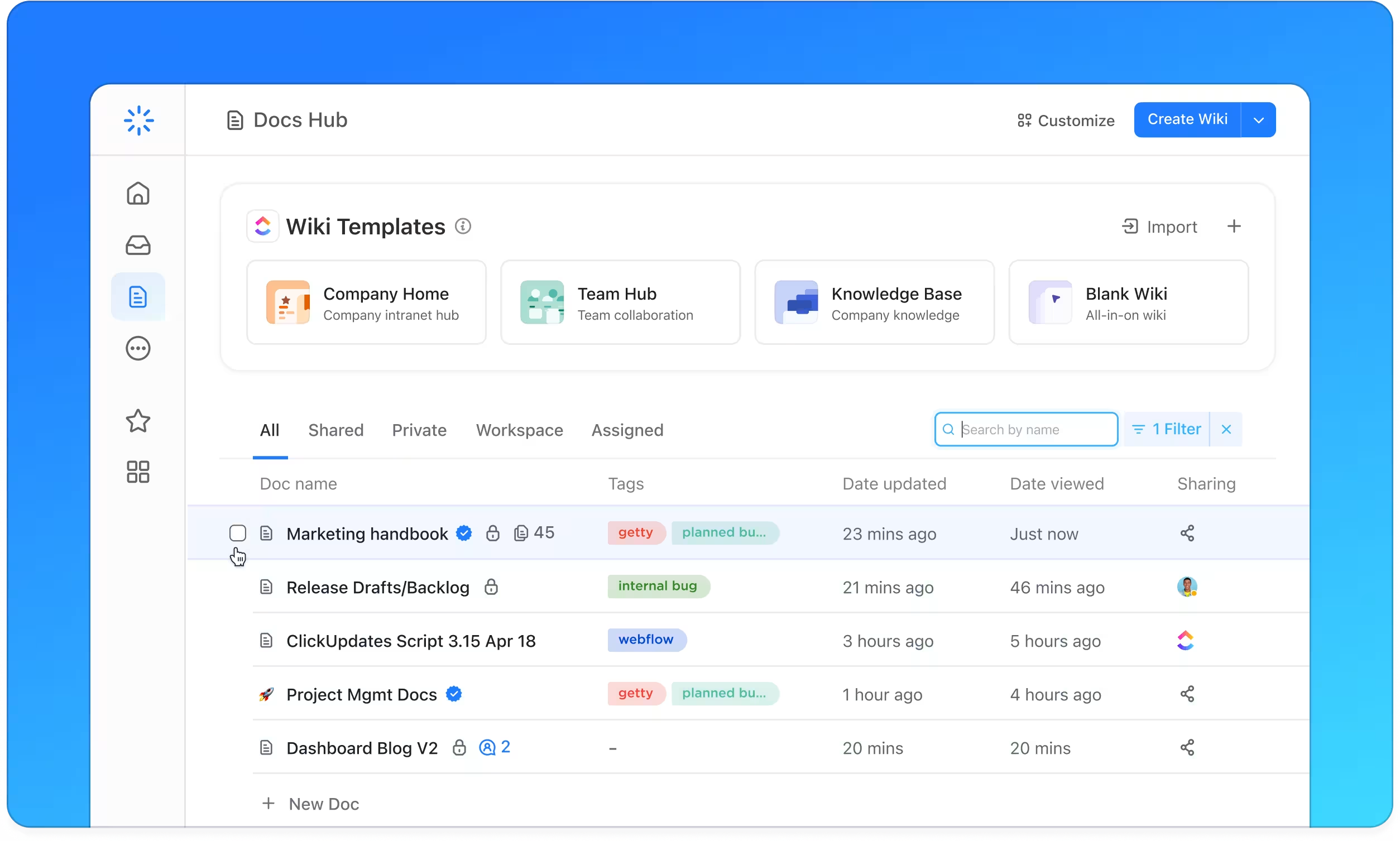
Organize
Structured authentication documentation with ClickUp Docs
- Authentication methods, Token management, MFA setups, Error handling, Changelog
- Table of contents plus nested pages for easy navigation
- Uniform page templates for consistent documentation
Why it matters: Your team finds critical security info quickly, reducing delays and errors.
Manage
Trackable ownership and workflows
- Convert documentation gaps into assigned tasks
- Assign owners, due dates, and establish review cycles
- Track documentation updates alongside development work
Why it matters: Accountability keeps your authentication knowledge base accurate and reliable.
Synchronize
Documentation connected to authentication updates
- Link docs to workflow changes, security patches, and incident postmortems
- Connect bugs and support issues directly to relevant documentation
- Integrate feedback loops to continuously improve content
Why it matters: Your knowledge base evolves in lockstep with your authentication environment.
ClickUp knowledge base for authentication workflows