Elevate Your Zero Trust Architecture with Tailored CRM
Why Zero Trust Architects Rely on Specialized CRM Solutions
Designing and maintaining zero trust environments demands precise coordination and airtight documentation. Without a CRM, critical security details can slip through the cracks.
Here’s what often breaks down when zero trust architects manage workflows manually:
- Access controls become inconsistent — tracking permissions and device trust levels without a unified system leads to gaps.
- Security policy updates get delayed — scattered notes and emails hinder timely revisions.
- Vendor and partner integrations stall — lack of centralized communication causes misalignment.
- Incident response coordination falters — unclear responsibilities and fragmented logs slow mitigation.
- Audit trails become incomplete — manual record-keeping fails to capture full context.
- Onboarding new team members is inefficient — no centralized knowledge base for protocols and contacts.
- Communication spans multiple platforms — making it hard to maintain a comprehensive security posture.
Unlock Clear Advantages Over Conventional Security Tools
Conventional Approaches
- Disparate spreadsheets and emails
- No centralized access control tracking
- Limited visibility into vendor relationships
- Manual incident coordination
- Fragmented audit documentation
- No automated reminders for policy reviews
- Communication scattered across apps
- Difficult onboarding processes
ClickUp CRM for Zero Trust
- Centralized repository for all security stakeholders
- Real-time logging of access permissions and changes
- Visual pipelines for vendor and partner integrations
- Automated workflows for incident response
- Comprehensive audit trails linked to tasks
- Scheduled alerts for policy updates and reviews
- Unified communication within secure environment
- Streamlined onboarding with knowledge bases
How CRM Software Empowers Zero Trust Architects
Centralizing Security Stakeholders and Assets
Managing Access Control Policies
Coordinating Incident Response Efforts
Tracking Vendor and Partner Compliance
Maintaining Audit Trails and Documentation
Onboarding Security Teams Efficiently
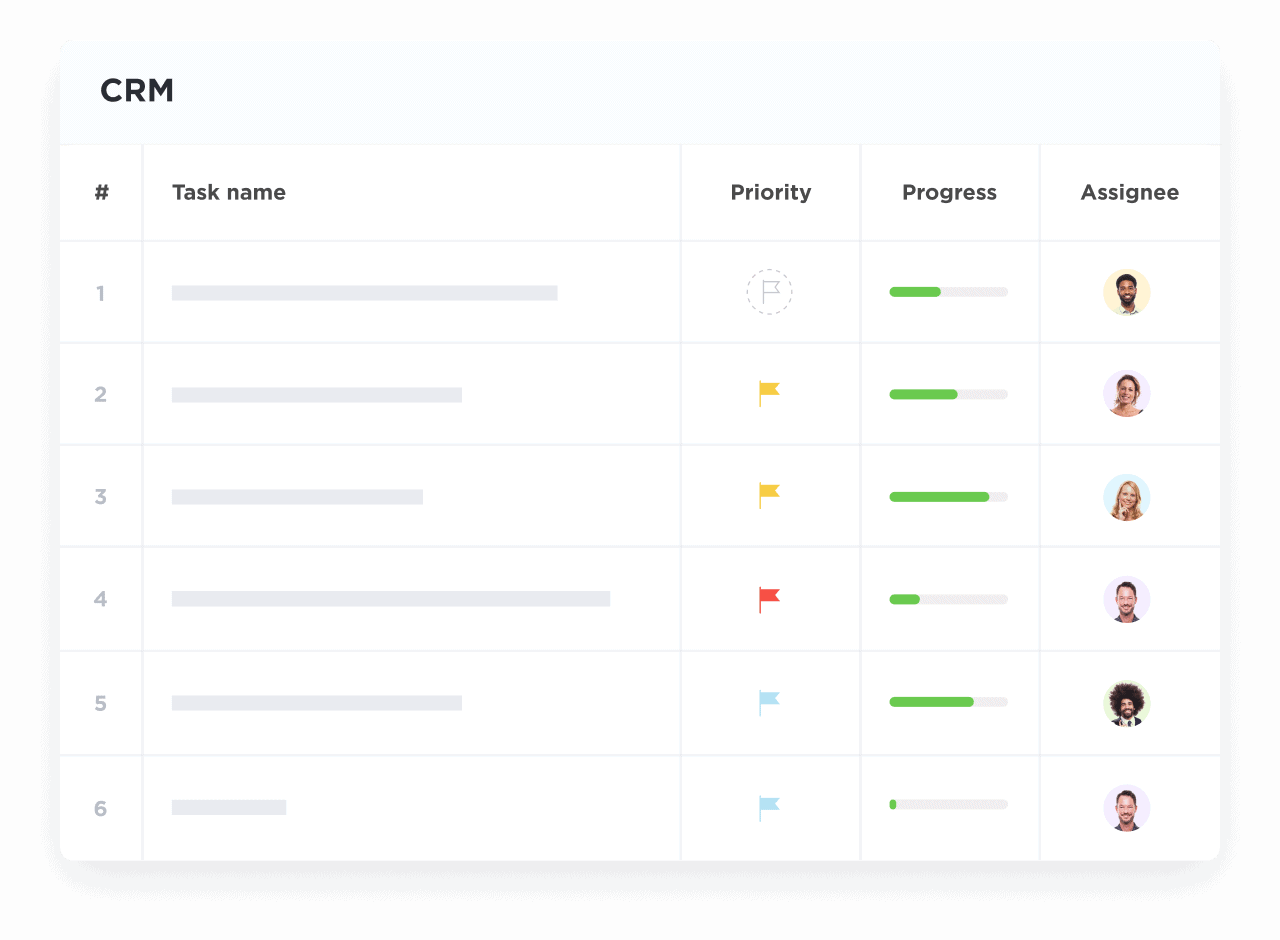
Synchronizing Multi-Team Security Initiatives
Automating Routine Security Checks
Transforming Security Meetings into Action Plans
Who Benefits Most from ClickUp CRM in Zero Trust Architecture
For Security Architects Leading Enterprise Deployments
For Network Security Engineers
For Compliance Officers and Auditors
How ClickUp CRM Simplifies Zero Trust Architecture
Create a Single Source of Truth for Security Stakeholders
Centralize all users, devices, vendors, and partners with detailed profiles and activity histories.
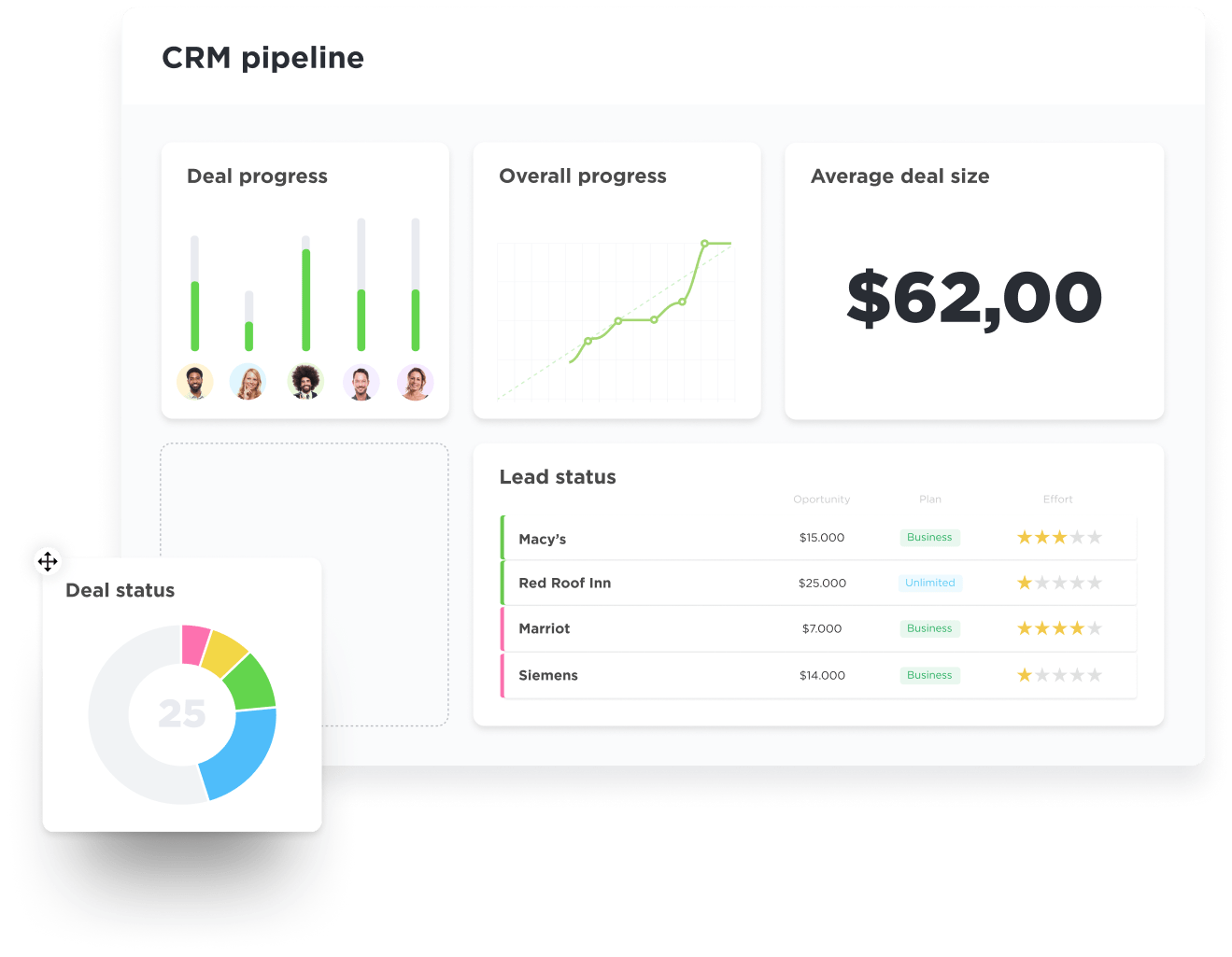
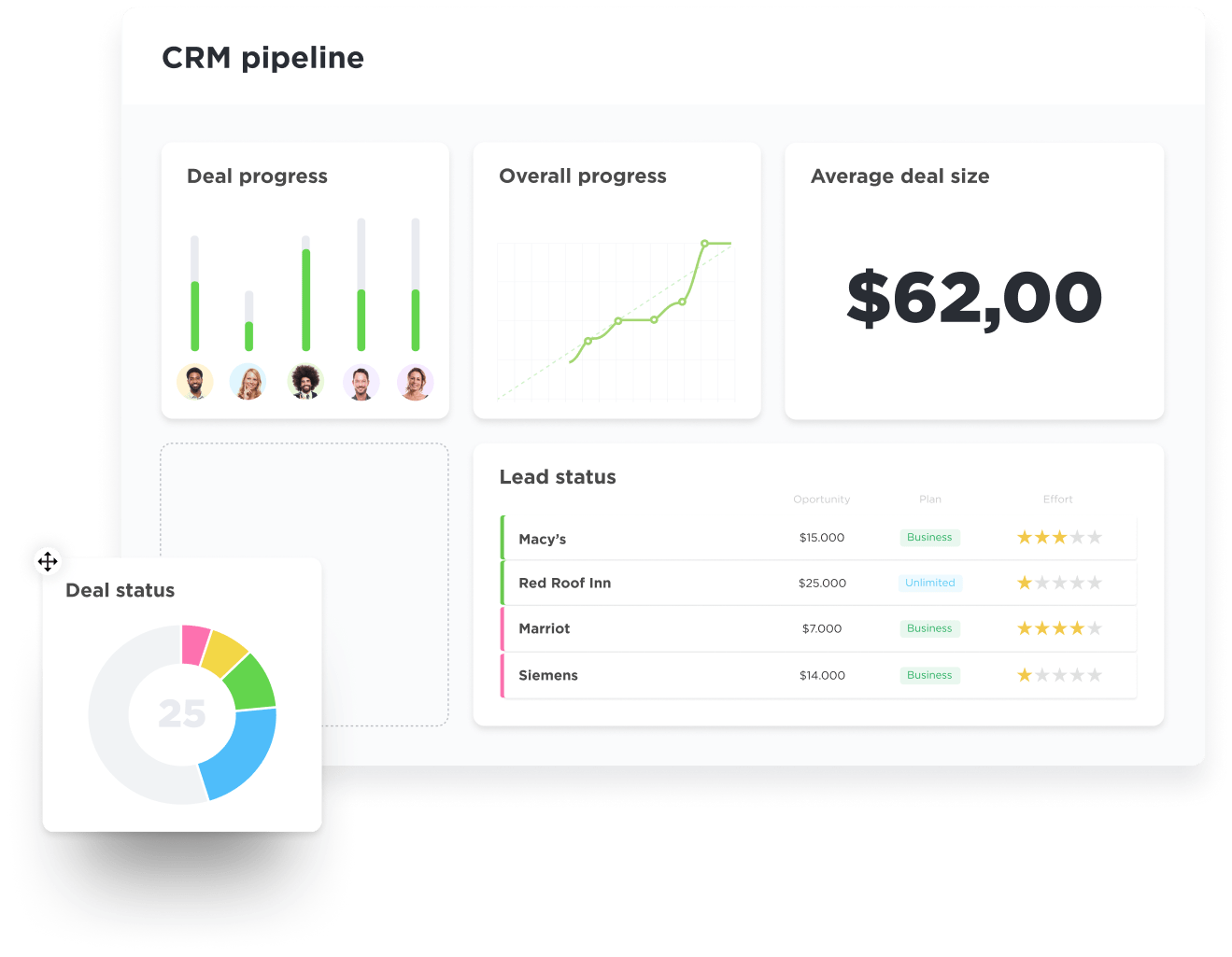
Visualize Access and Policy Lifecycles
Map out approval workflows, deployment stages, and audit checkpoints with intuitive pipelines.
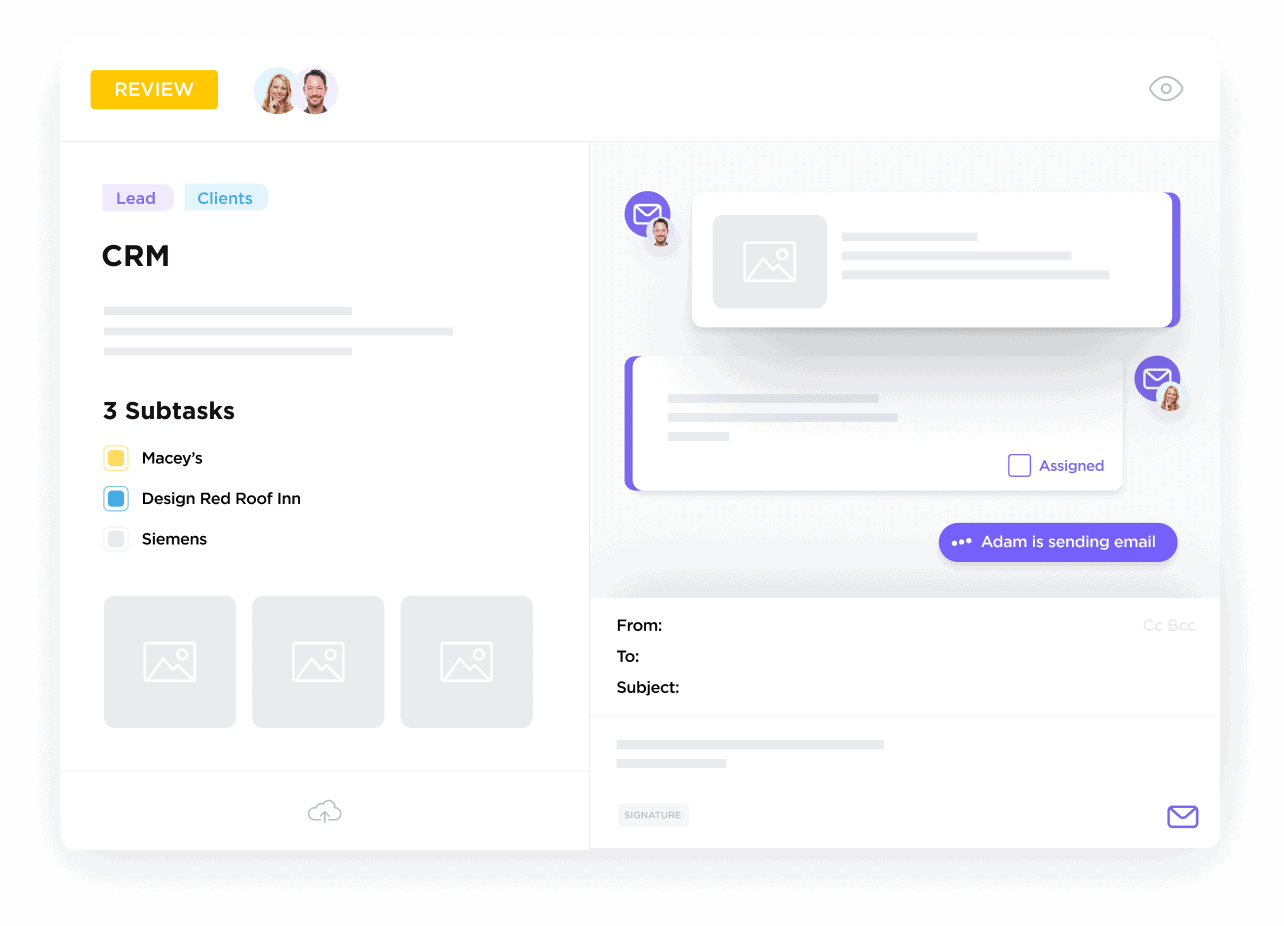
Record and Track All Communications and Changes
Keep logs of policy revisions, incident communications, and authorization changes linked to relevant tasks.
Turn Security Discussions into Action Items
Assign tasks with deadlines and priorities to ensure swift implementation and accountability.
Integrate Documentation and Evidence Seamlessly
Attach compliance reports, incident logs, and protocol documents directly within CRM records.
Stay Ahead with Automated Alerts and Dashboards
Receive timely reminders for reviews, renewals, and security assessments, all tracked in custom dashboards.