Leading CRM Software Tailored for Vulnerability Management Leads
Why Vulnerability Management Leads Rely on CRM Software
Managing vulnerabilities without a CRM is like trying to secure your network by memory alone. Critical details slip through the cracks.
Here’s what often breaks down when vulnerability leads work without structured CRM support:
- Asset and vulnerability records scatter — losing track of affected systems and risk status.
- Communication with remediation teams falters — unclear ownership and missed updates.
- Patch management timelines get murky — deadlines and compliance requirements slip away.
- Vendor and third-party coordination stalls — no unified history of interactions or open issues.
- Incident follow-ups become reactive and disorganized — no clear audit trail or accountability.
- Stakeholder reporting lacks clarity — making risk prioritization difficult.
- New team members onboard without context — no centralized repository of past vulnerabilities or decisions.
- Multiple tools cause data silos — hindering holistic security visibility.
Why Conventional Methods Fall Short for Vulnerability Management Leads
Traditional Methods
- Vulnerability data scattered across spreadsheets and emails
- No centralized communication tracking
- Manual, error-prone patch scheduling
- Unclear remediation ownership
- Limited visibility into vendor statuses
- No automated alerts or follow-ups
- Disconnected tools causing delays
- Reactive incident management
ClickUp CRM
- Single source of truth for all vulnerabilities and assets
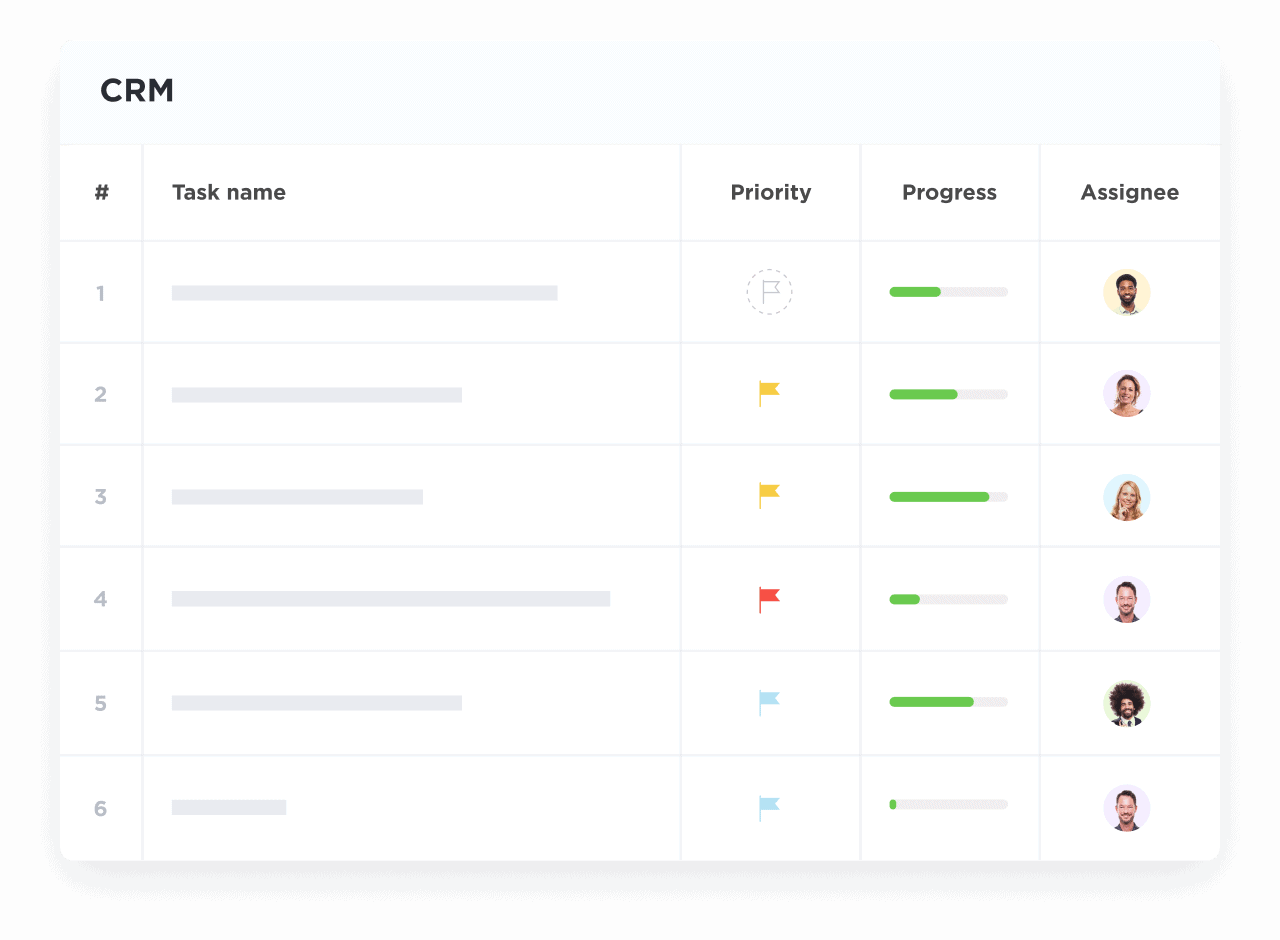
- Automated logging of communication and remediation steps
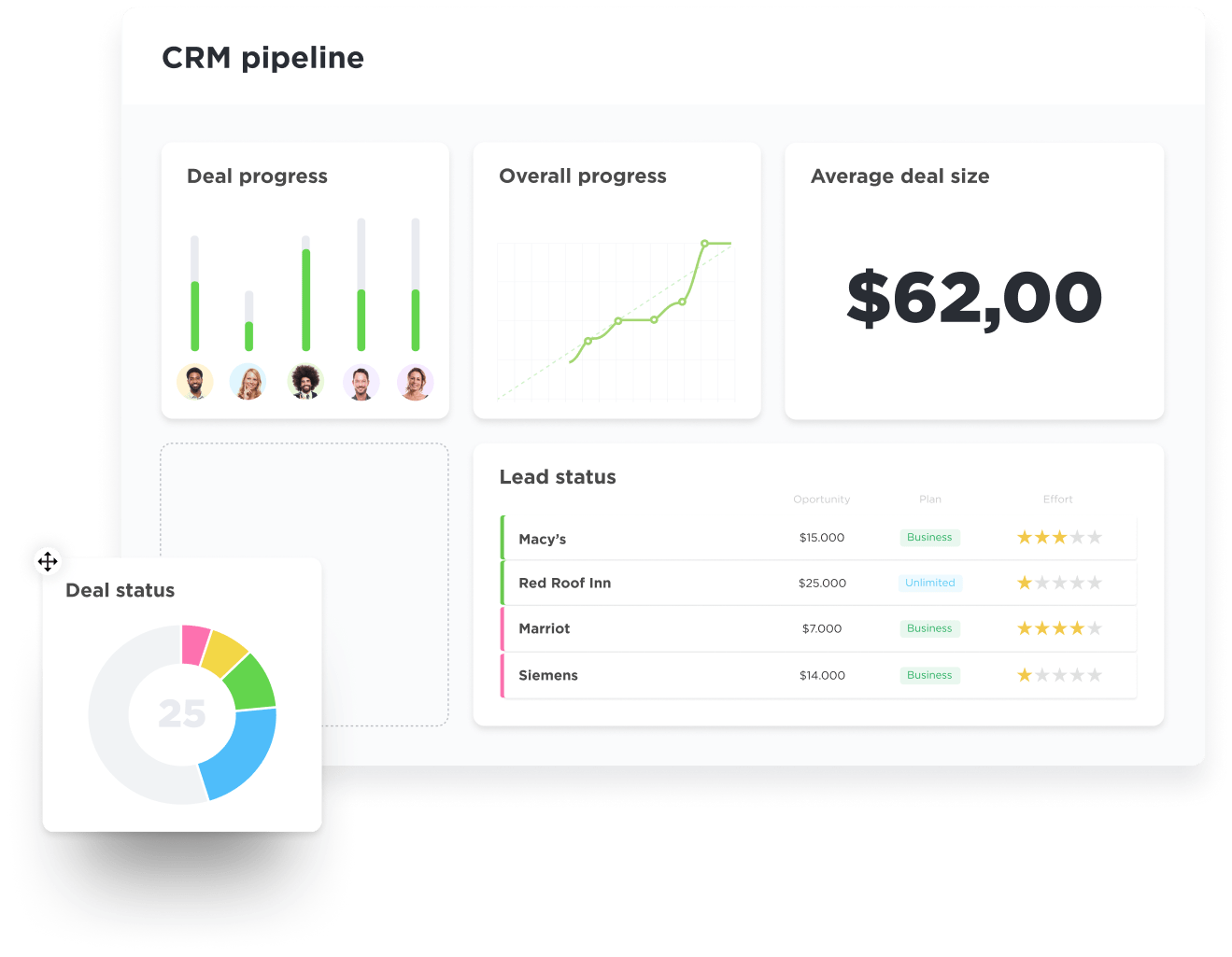
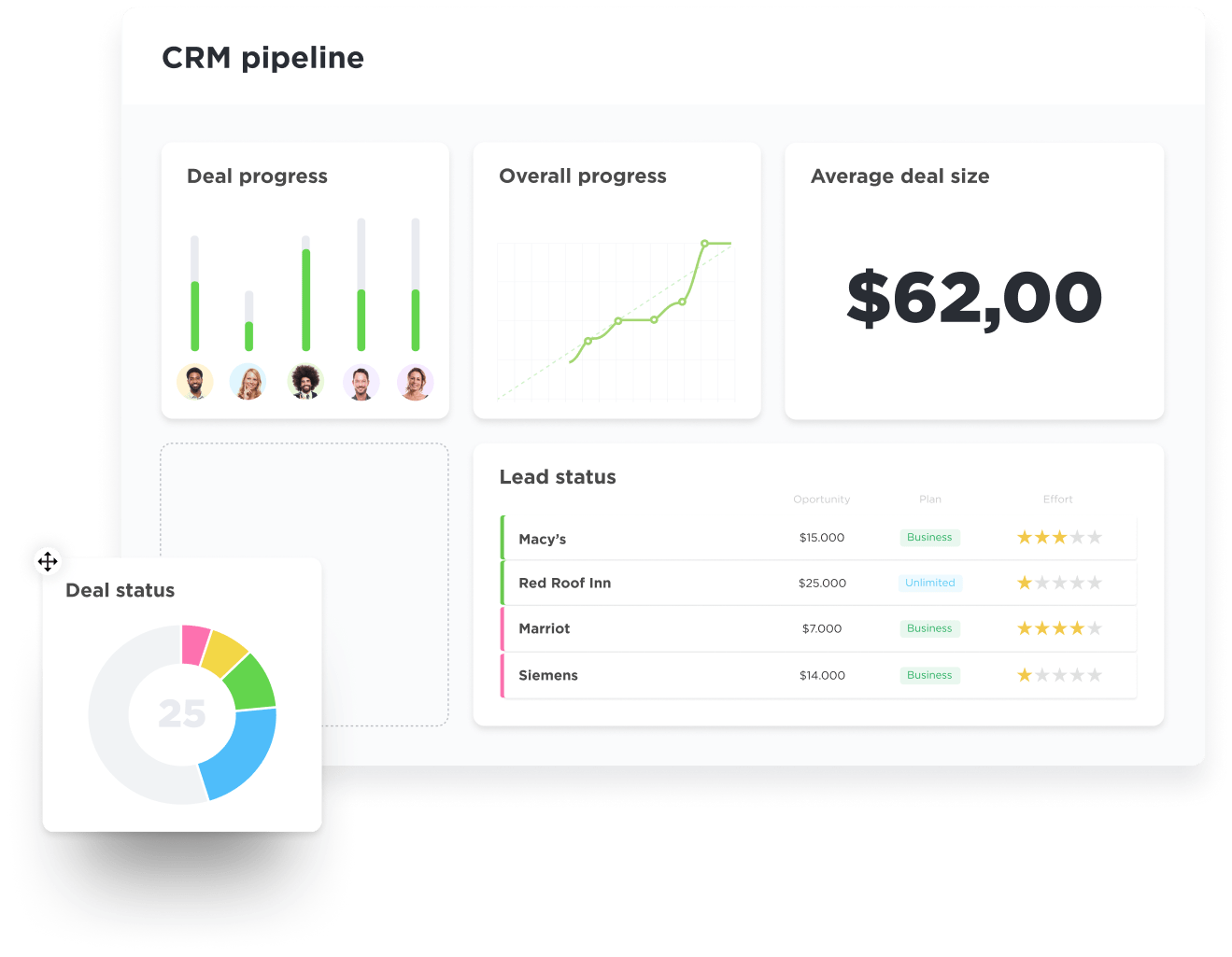
- Visual pipelines for patch and mitigation workflows
- Clear task ownership with deadlines and reminders
- Centralized vendor and third-party tracking
- Auto-generated alerts for overdue actions
- Integrated dashboards for real-time risk status
- Proactive incident follow-up and audit trails
How CRM Software Empowers Vulnerability Management Leads
Centralizing Vulnerability and Asset Data
Coordinating Remediation Efforts Across Teams
Automating Patch Management Workflows
Tracking Vendor and Third-Party Risks
Log vendor communications, risk assessments, and remediation commitments in one unified CRM record.
Maintaining Audit-Ready Incident Documentation
Document every vulnerability lifecycle step, from detection through mitigation, ensuring compliance and accountability.
Generating Real-Time Risk and Status Dashboards
Utilize ClickUp Brain and Brain Max to visualize trends, overdue tasks, and risk hotspots instantly.
Enhancing Cross-Departmental Visibility
Share up-to-date vulnerability statuses and remediation plans with leadership, IT, and compliance teams.
Streamlining Regulatory Compliance Reporting
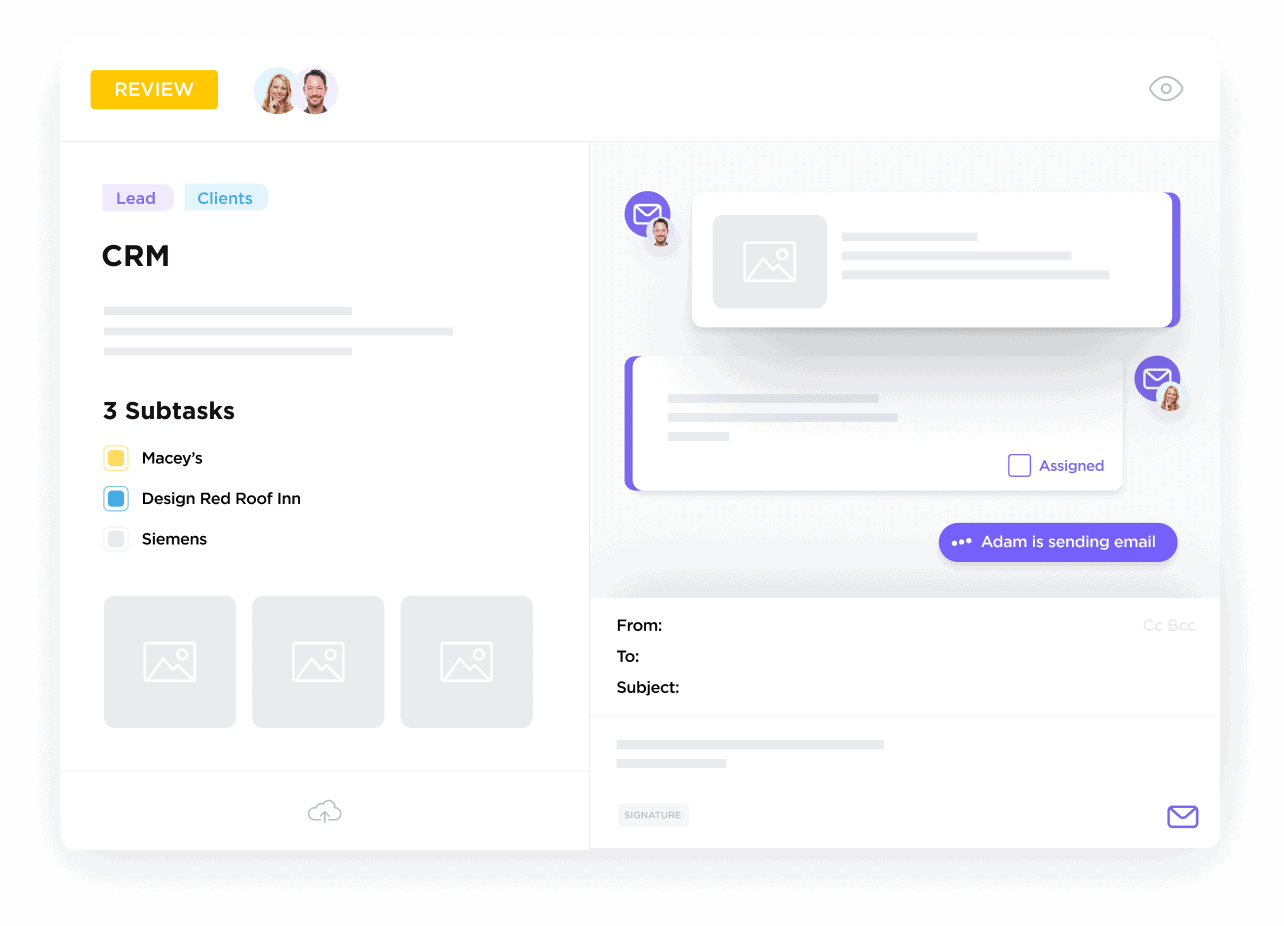
Converting Security Meetings Into Actionable Tasks
Attach meeting notes, assign owners, and track follow-ups to ensure no discussion point is lost.
Who Gains the Most from ClickUp CRM in Vulnerability Management?
Ideal for security leads managing complex vulnerability landscapes, cross-team coordination, and compliance demands.
If You Lead Vulnerability Management in Large Enterprises
If You Manage Security in Mid-Sized Organizations
If You Are a Compliance or Risk Officer
Practical Benefits of ClickUp CRM for Vulnerability Oversight
Build a Single Source of Truth for Vulnerabilities
Log every asset, vulnerability detail, and risk rating with customizable fields and activity timelines.
Visualize Remediation Pipelines
Track patch cycles, mitigation stages, and approvals with intuitive boards and timelines.
Log Communication and Incident History
Keep emails, calls, and notes attached to each vulnerability for full context.
Turn Security Discussions into Action Items
Convert meeting notes and chat into tasks with owners, due dates, and automated reminders.
Integrate Documentation and Evidence
Attach vulnerability scans, compliance reports, and vendor responses directly to CRM records.
Stay Ahead with Intelligent Alerts and Dashboards
Leverage ClickUp Brain and Brain Max for predictive insights and real-time risk monitoring.