Leading CRM Software for Cyber Attack Monitoring Teams
Why Cybersecurity Teams Rely on CRM Software
Monitoring cyber threats without a CRM is like hunting in the dark without a map. Critical details slip through the cracks, and response times suffer.
Here’s what typically falters when security teams manage attacks manually:
- Threat data gets siloed — missing context slows down detection and resolution.
- Incident timelines blur — unclear who handled what or when.
- Communication breakdowns — fragmented channels leave gaps in coordination.
- Stakeholder updates lag — executives and clients stay uninformed.
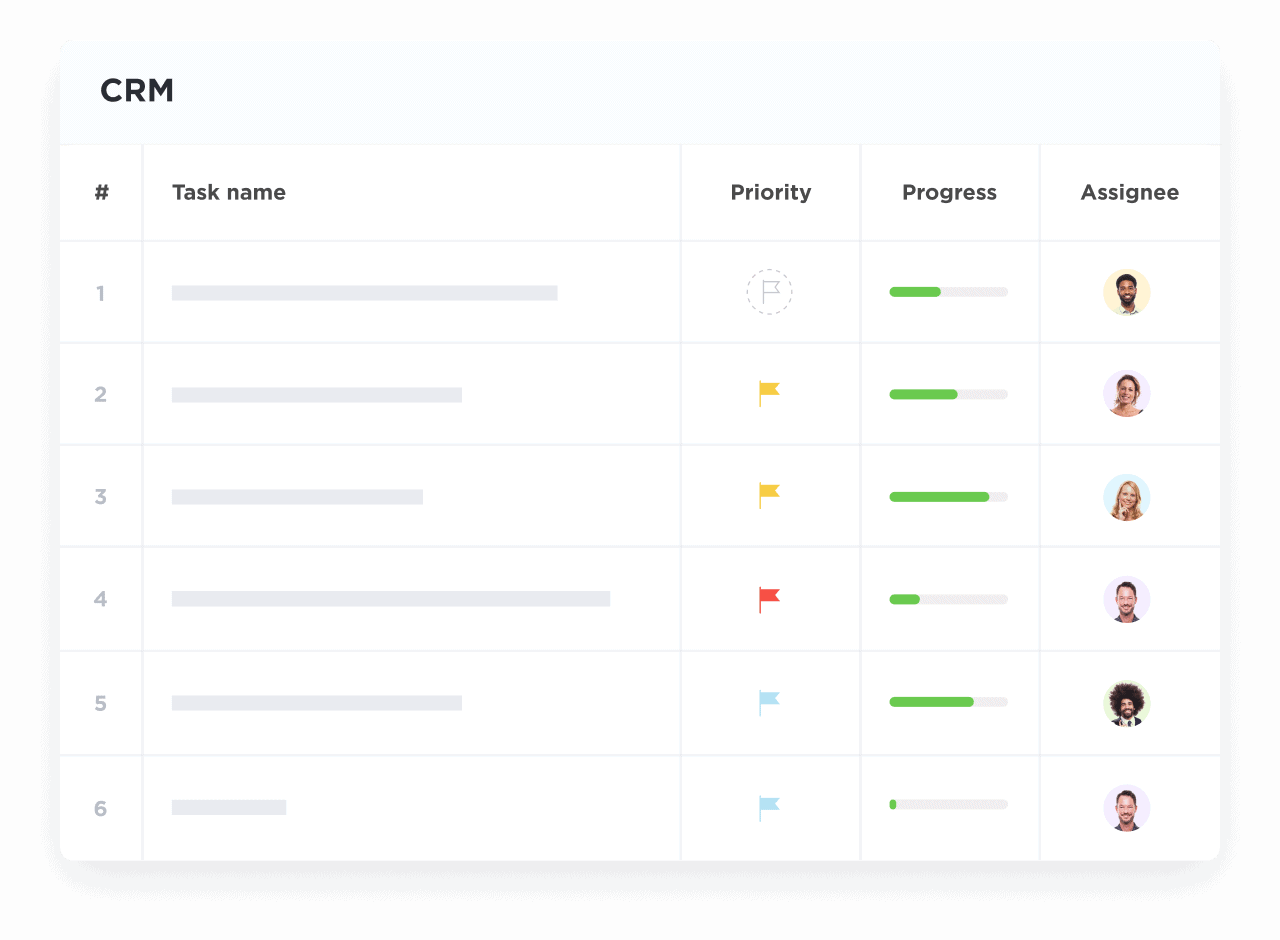
- Response tasks lack accountability — follow-ups and remediations fall behind.
- Vendor and partner interactions scatter — complicating threat intelligence sharing.
- New analysts onboard without history — losing valuable lessons from past incidents.
- Compliance documentation becomes inconsistent — risking audits and penalties.
Why Traditional Methods Fall Short Against ClickUp Cybersecurity CRM
Legacy Approaches
- Threat data scattered across emails and spreadsheets
- No centralized incident tracking
- Manual follow-ups prone to error
- Limited visibility into response progress
- No automated reminders for compliance
- Communication fragmented across platforms
- Difficulty consolidating external vendor info
- Cumbersome reporting processes
ClickUp Cybersecurity CRM
- Unified database for all threat actors and incidents
- Real-time logging of investigations and communications
- Automated workflows and follow-up reminders
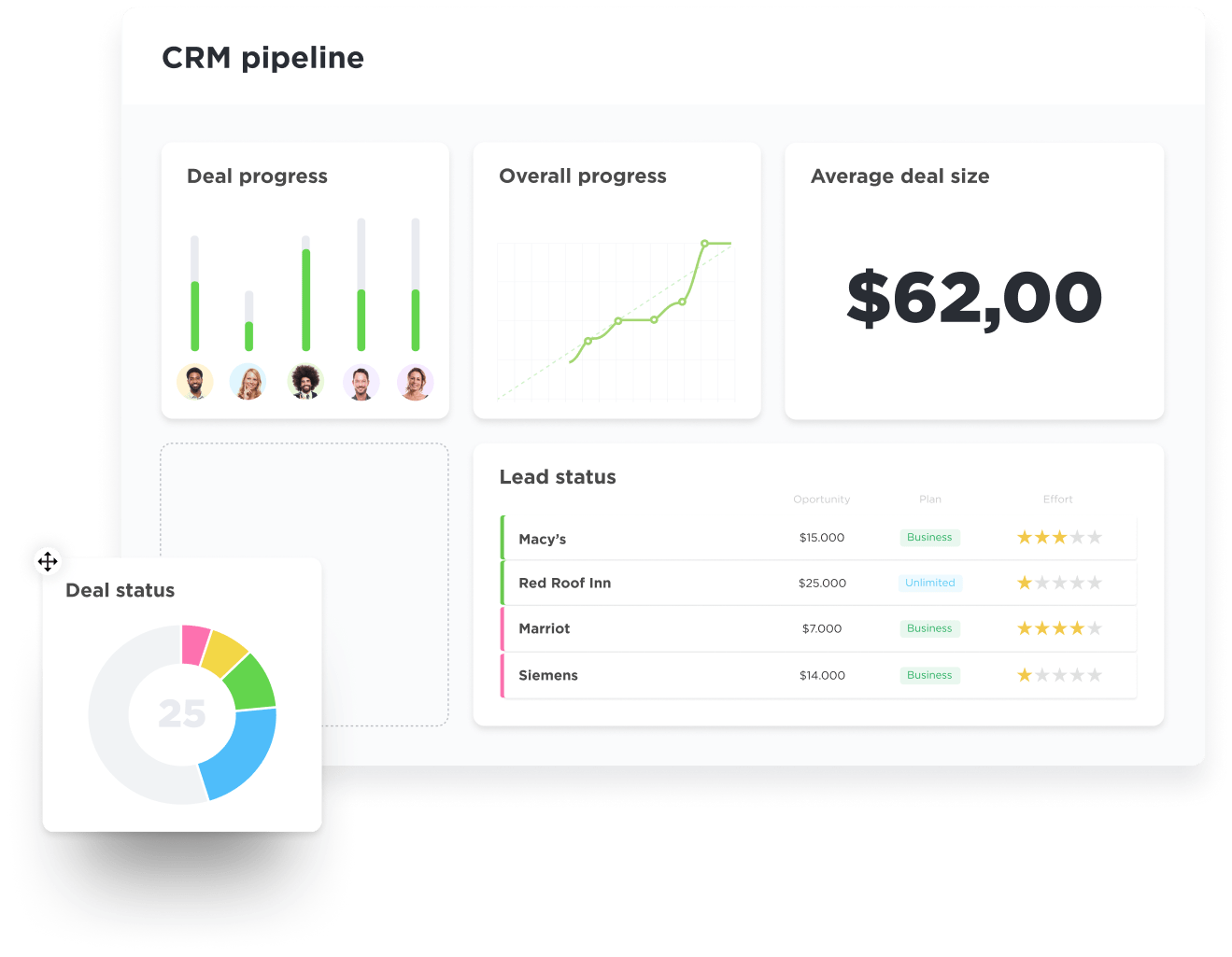
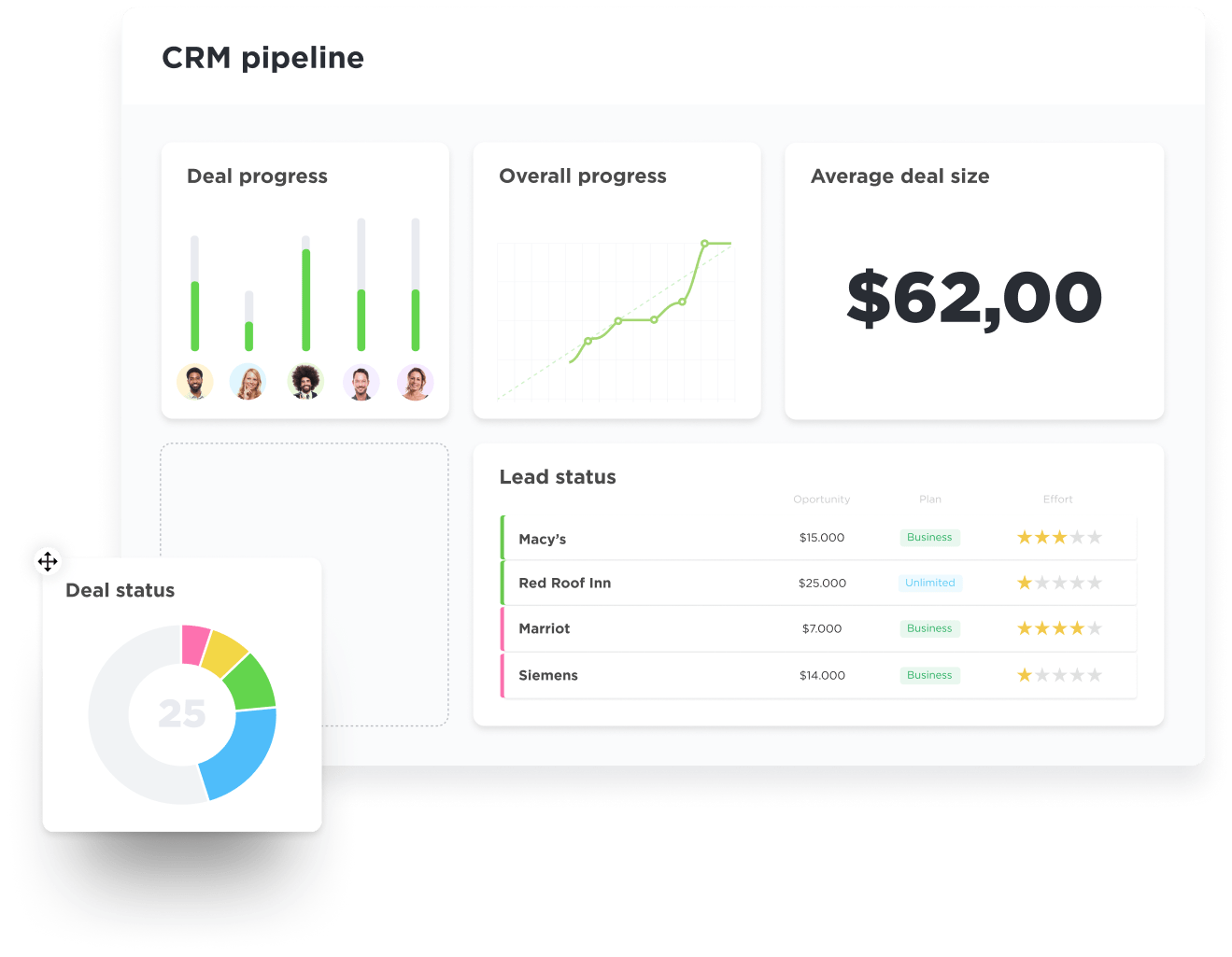
- Visual incident pipelines to monitor progress
- Compliance tracking and audit-ready documentation
- Secure collaboration across teams and partners
- Integration with external threat intelligence feeds
- Custom dashboards to highlight critical risks
How CRM Software Empowers Cyber Attack Monitoring
Centralizing Threat Intelligence & Stakeholder Info
Managing Incident Response Pipelines
Automating Alert Follow-Ups & Notifications
Logging Forensic & Investigation Notes
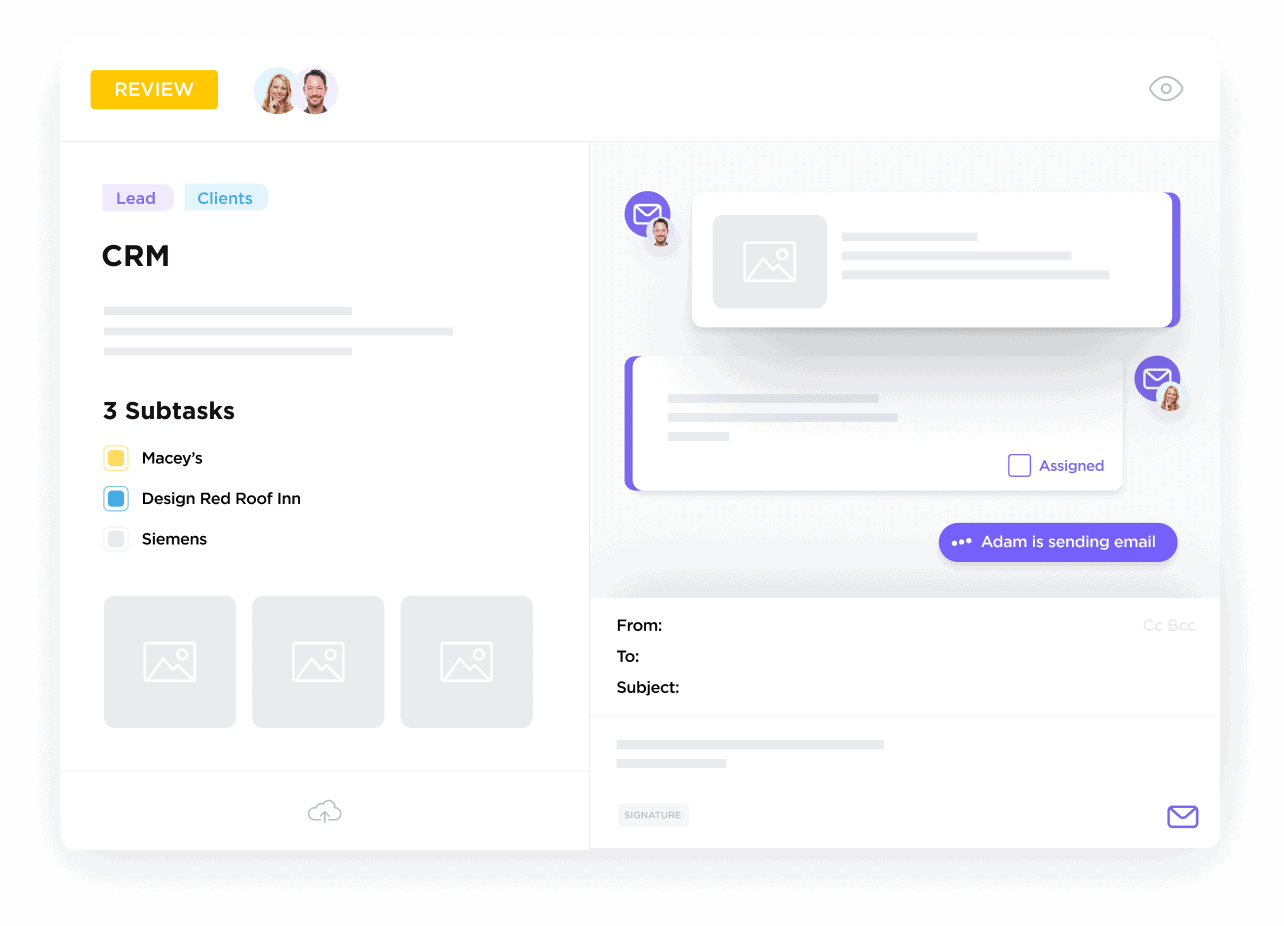
Document every analysis, hypothesis, and finding directly linked to incidents for auditability and knowledge sharing.
Coordinating Cross-Department Collaboration
Enable seamless communication between IT, legal, PR, and external partners through shared tasks and timelines.
Tracking Vendor & Security Tool Interactions
Maintain records of third-party engagements, patch status, and support tickets to streamline resolutions.
Monitoring Compliance & Reporting Deadlines
Stay audit-ready by tracking regulatory requirements, evidence collection, and timely report submissions.
Visualizing Threat Landscape and Trends
Use ClickUp dashboards to spot patterns, recurring vulnerabilities, and response effectiveness at a glance.
Turning Incident Debriefs into Actionable Tasks
Capture lessons learned and assign improvements with clear ownership and deadlines to strengthen defenses.
Who Benefits Most from ClickUp Cybersecurity CRM
Ideal for security teams overwhelmed by alerts, complex incidents, and coordination challenges.
For Security Operations Centers (SOCs)
ClickUp CRM provides a centralized command center to monitor threats and orchestrate responses across global teams.
For Incident Response Teams
Manage investigations, evidence, and communication flows efficiently to reduce dwell time and impact.
For Cybersecurity Analysts & Researchers
Track vulnerabilities, threat actor profiles, and collaborate on intelligence analysis within one platform.
How ClickUp CRM Strengthens Cyber Attack Monitoring
Consolidate Threat Data
Centralize alerts, logs, and actor profiles in ClickUp CRM, enriched by Brain’s AI-powered insights.
Visualize Incident Pipelines
Use customizable boards to map detection, analysis, containment, and recovery stages.
Automate Routine Tasks
Set up Brain Max automations for alerts, escalations, and compliance reminders.
Collaborate Across Teams
Share intelligence and assign investigation tasks seamlessly with built-in communication tools.
Monitor Compliance Progress
Track regulatory requirements and documentation status to stay audit-ready.
Analyze & Adapt Proactively
Leverage Brain’s predictive analytics to identify emerging threats and optimize response strategies.