Elevate Your Authentication Verification with the Leading CRM Software
Why Authentication Verification Demands Specialized CRM Software
Managing authentication verification without a dedicated CRM is like relying on fragmented logs and guesswork. This leads to critical security gaps and operational inefficiencies.
Common challenges faced without CRM support include:
- Verification processes become inconsistent — missing audit trails and unclear user identity status.
- Delayed response times — manual checks slow down user onboarding and access approvals.
- Scattered communication — security teams and stakeholders lack a unified platform.
- Compliance risks rise — difficulty tracking verification steps and documentation.
- User data fragmentation — identities and verification statuses stored in multiple disconnected systems.
- Lack of automation — repetitive tasks consume valuable time and increase error rates.
- Onboarding new security personnel is challenging — no centralized history or process documentation.
- Difficult collaboration across departments and vendors — causing delays and miscommunications.
Why Traditional Verification Methods Fall Short Compared to ClickUp CRM
Traditional Verification Methods
- Authentication data scattered across spreadsheets and emails
- No centralized audit trail for verification events
- Manual status updates prone to errors
- Difficult to track multi-factor authentication steps
- Communication fragmented across teams
- No automated reminders for re-verification or expiry
- Compliance documentation stored separately
- Limited visibility into user verification progress
ClickUp CRM for Authentication Verification
- Consolidate all user authentication records in a single CRM
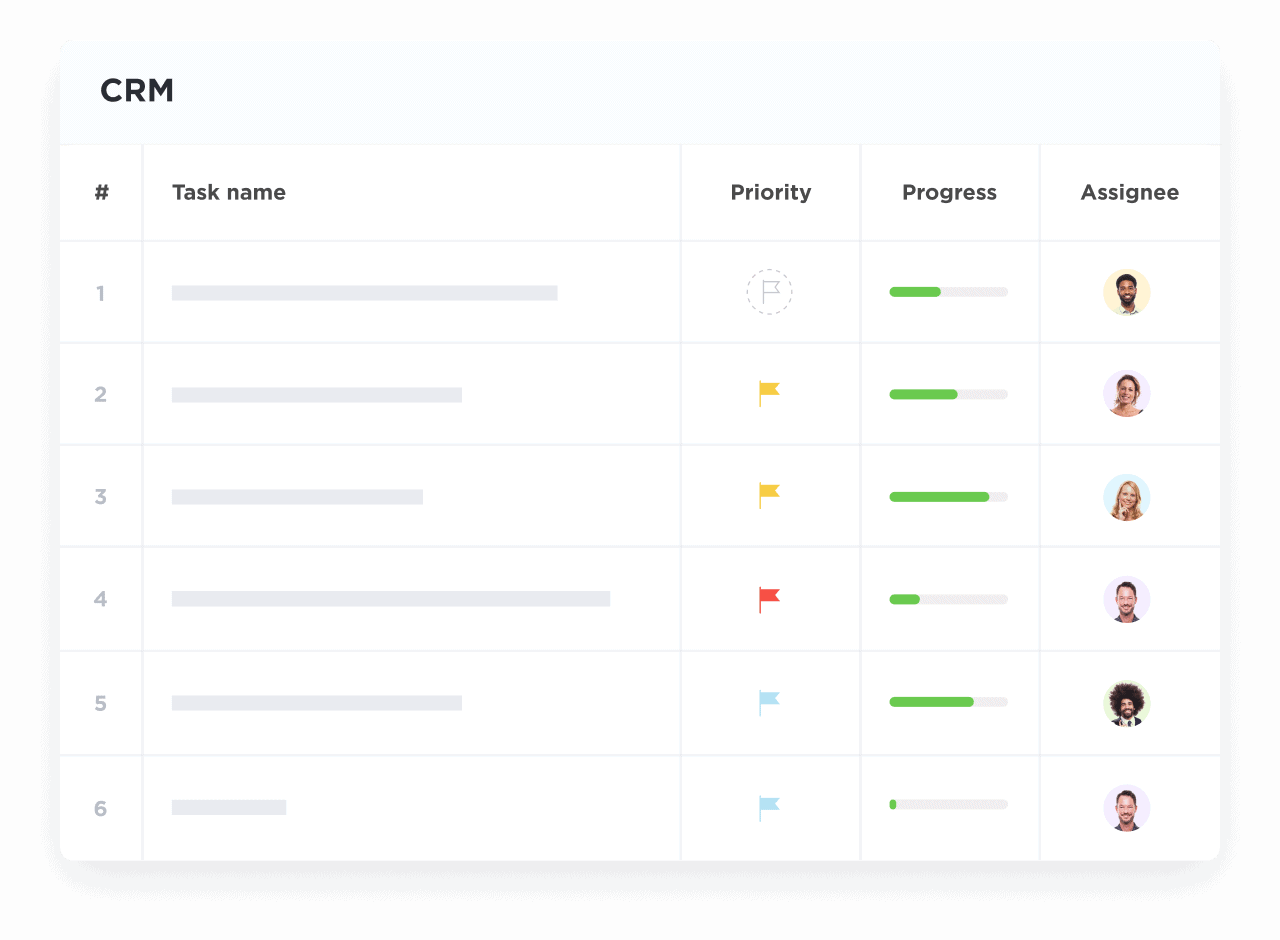
- Log verification attempts, approvals, and denials with timestamps
- Automate status updates and alerts for pending actions
- Visualize multi-factor verification pipelines
- Centralize team communication and notes
- Set automatic reminders for re-validation and compliance checks
- Attach compliance documents directly to user profiles
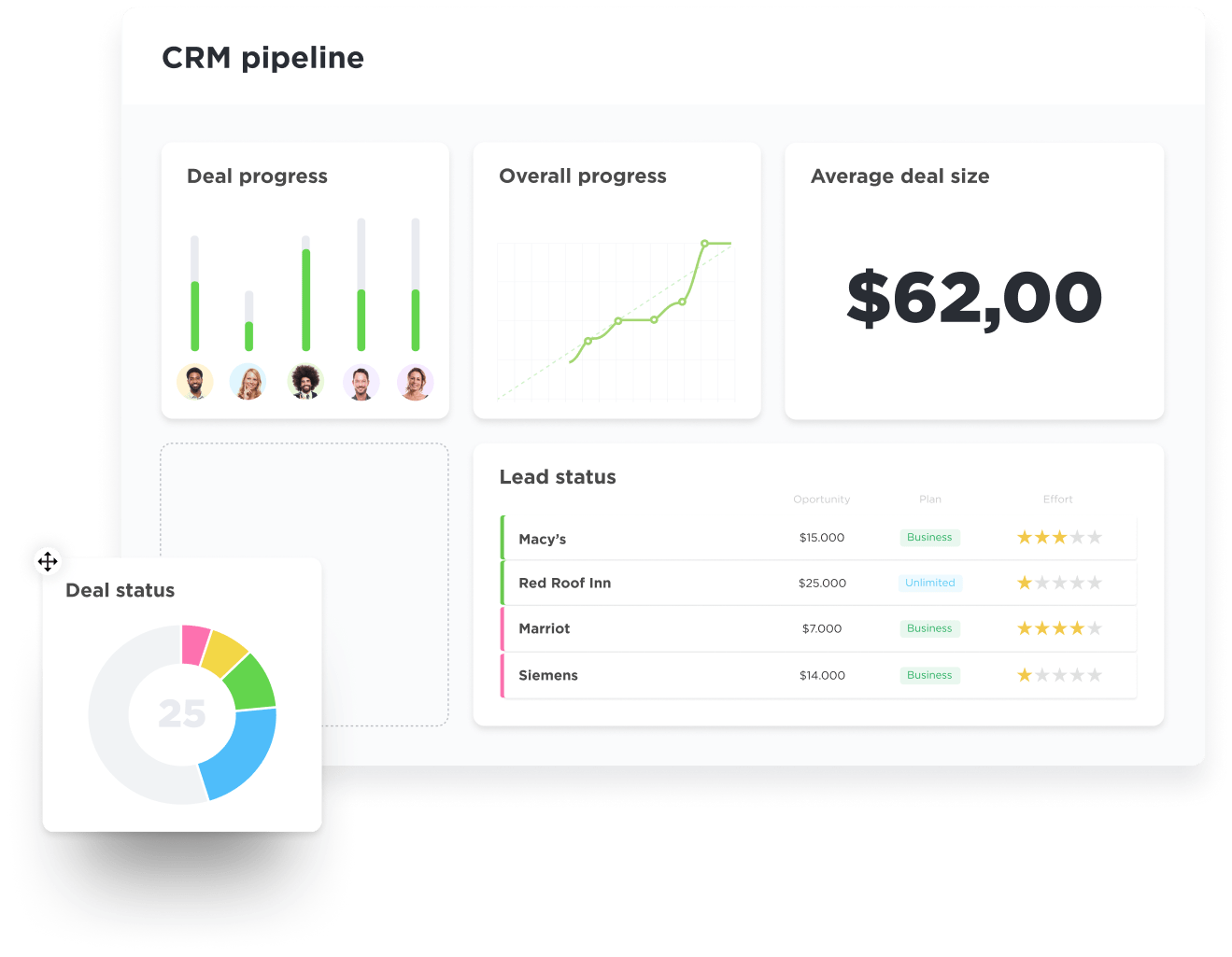
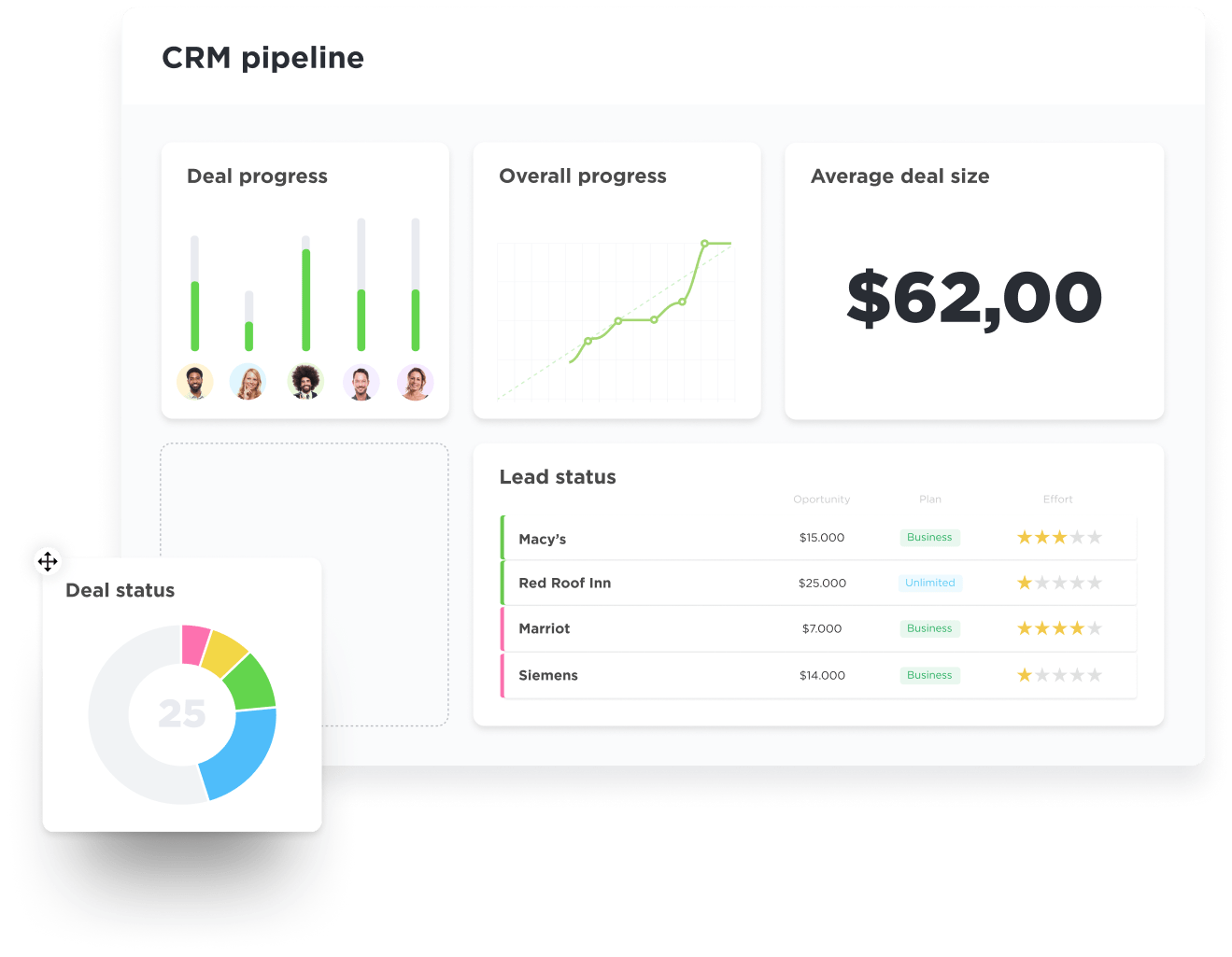
- Gain real-time dashboards for security oversight
How CRM Software Enhances Authentication Verification Workflows
Centralizing User Identity and Verification Data
Automating Multi-Factor Authentication Processes
Tracking Compliance Documentation and Expiration
Coordinating Security Team Collaboration
Managing Vendor and Third-Party Verifications
Auditing Authentication Events with Full Traceability
Onboarding New Security Staff Efficiently
Monitoring User Access and Privilege Changes
Generating Insights with ClickUp Brain and Brain Max
Who Benefits Most from ClickUp CRM for Authentication Verification
Ideal for security teams, compliance officers, and organizations managing complex user authentication demands.
If You’re a Security Operations Team Lead
Streamline coordination across verification agents, automate routine checks, and maintain audit-ready records effortlessly.
If You’re a Compliance Manager
Ensure all authentication processes meet regulatory standards with centralized documentation and timely alerts.
If You’re an IT Administrator
Manage user access, monitor verification status, and integrate authentication data across systems seamlessly.
How ClickUp CRM Transforms Authentication Verification
Create a Centralized Authentication Database
Aggregate all user identities, verification statuses, and related documents into one secure CRM platform.
Visualize Verification Pipelines Clearly
Track each step of multi-factor authentication and verification stages with intuitive visual workflows.
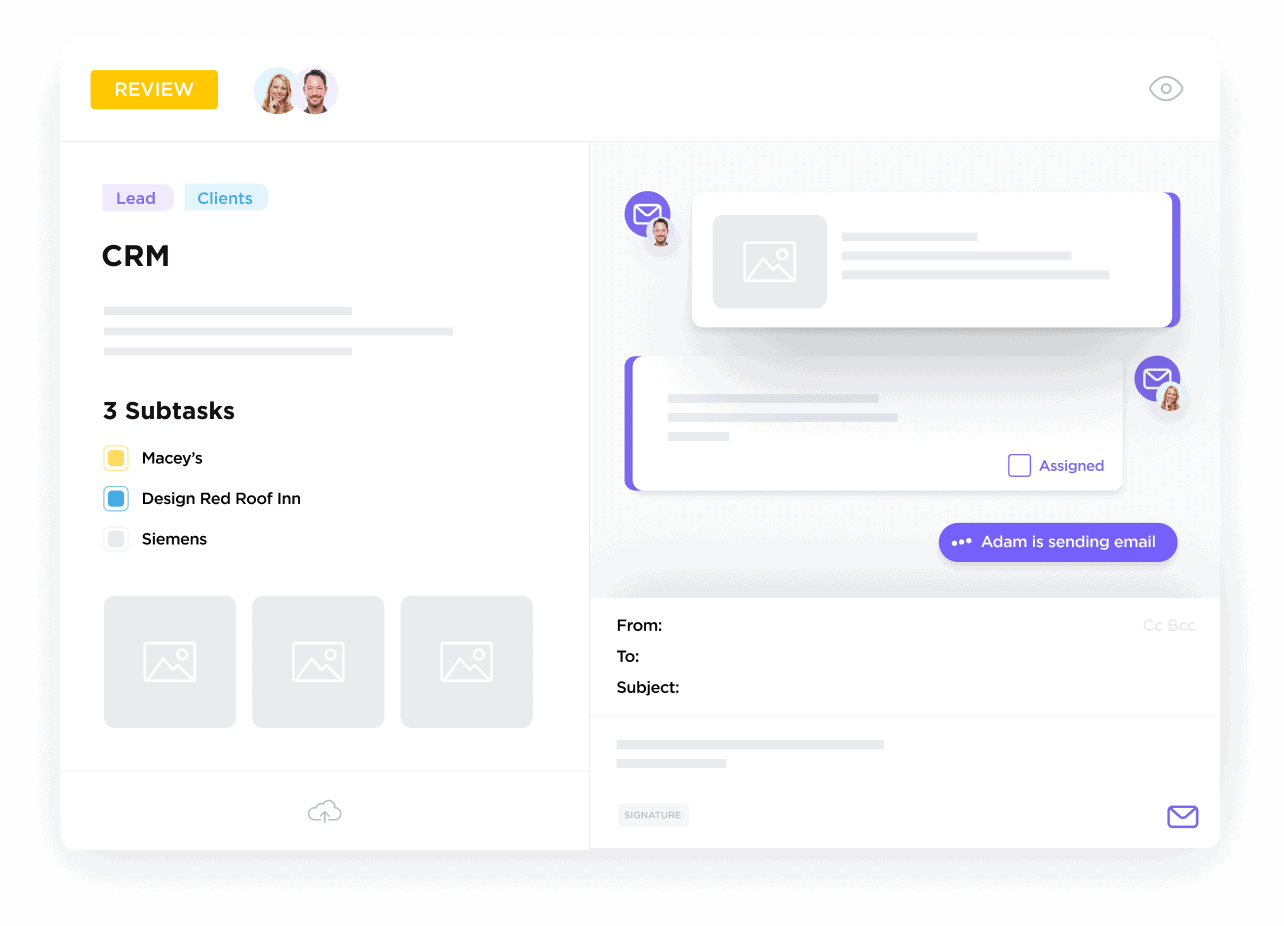
Maintain Complete Communication Logs
Log calls, emails, and decisions linked directly to user verification profiles.
Turn Verification Steps into Automated Tasks
Assign follow-ups, manage deadlines, and automate reminders to keep security tight.
Attach Compliance and Identity Documents
Keep all essential verification files, consents, and audit reports linked and accessible within the CRM.