Top AI Prompts to Secure OT Systems
AI Prompts Revolutionizing OT Security Operations
Protecting critical infrastructure goes beyond hardware—it demands vigilant, coordinated efforts behind the scenes.
Operational Technology (OT) security teams face complex challenges: monitoring diverse systems, managing incident responses, and ensuring compliance with stringent standards. AI prompts are rapidly becoming a vital asset in this landscape.
Security teams leverage AI to:
- Quickly identify emerging threats and vulnerabilities
- Generate detailed incident reports and response plans with minimal effort
- Interpret dense compliance requirements and technical guidelines
- Transform scattered logs and alerts into prioritized action items and workflows
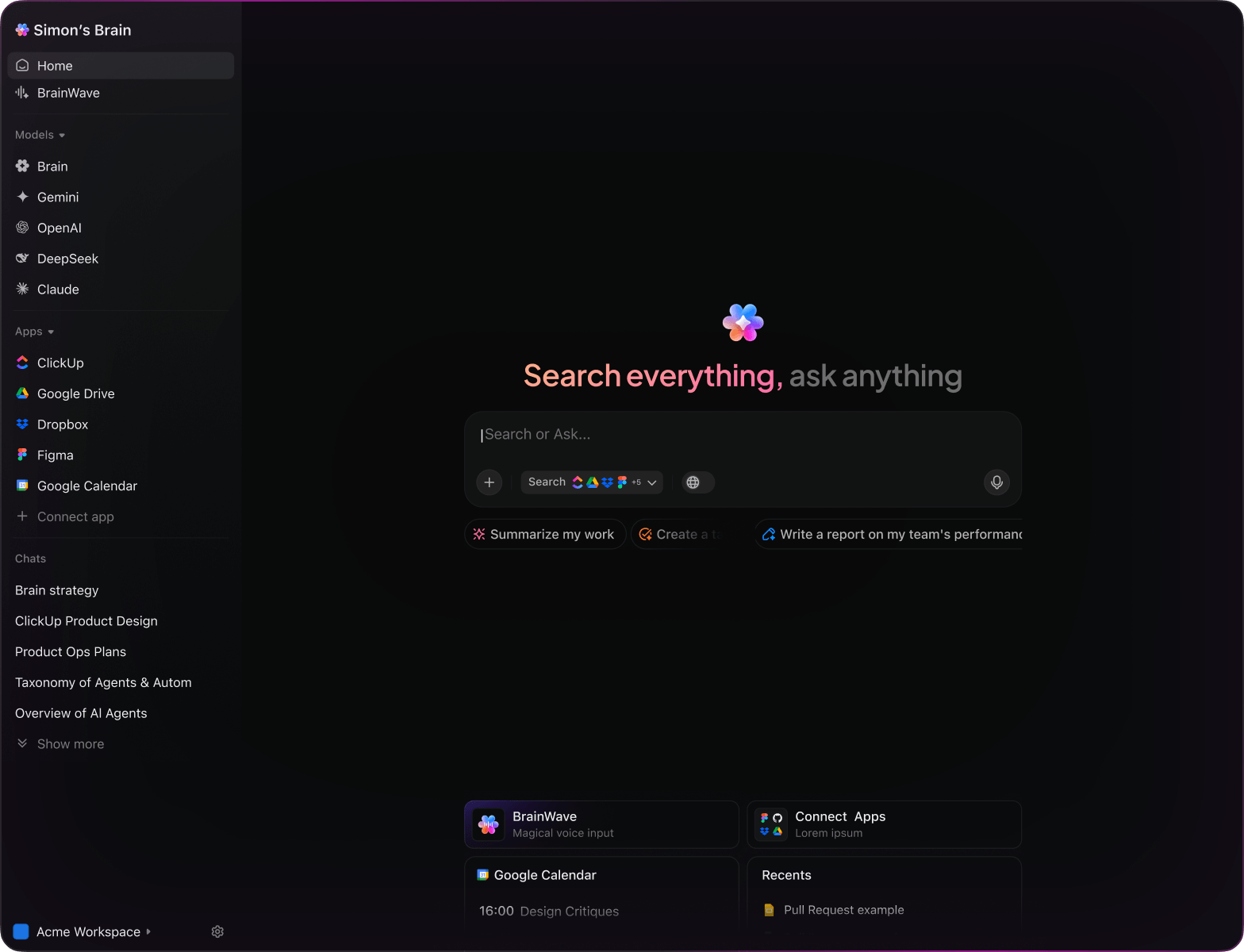
Integrated into tools like documentation, dashboards, and task trackers, AI in ClickUp Brain acts as a proactive partner—turning raw security data into clear, prioritized tasks that keep your infrastructure safe and resilient.
Why ClickUp Brain Stands Apart
Conventional AI Platforms
- Constantly toggling between apps to collect necessary data
- Repeatedly clarifying your security objectives
- Receiving generic, irrelevant feedback
- Hunting through multiple platforms for a single report
- Interacting with AI that lacks proactive engagement
- Manually switching between different AI engines
- Merely another add-on without deep integration
ClickUp Brain
- Deeply integrated with your OT tasks, documentation, and team communications
- Retains your security priorities and past interactions
- Provides detailed, context-aware guidance
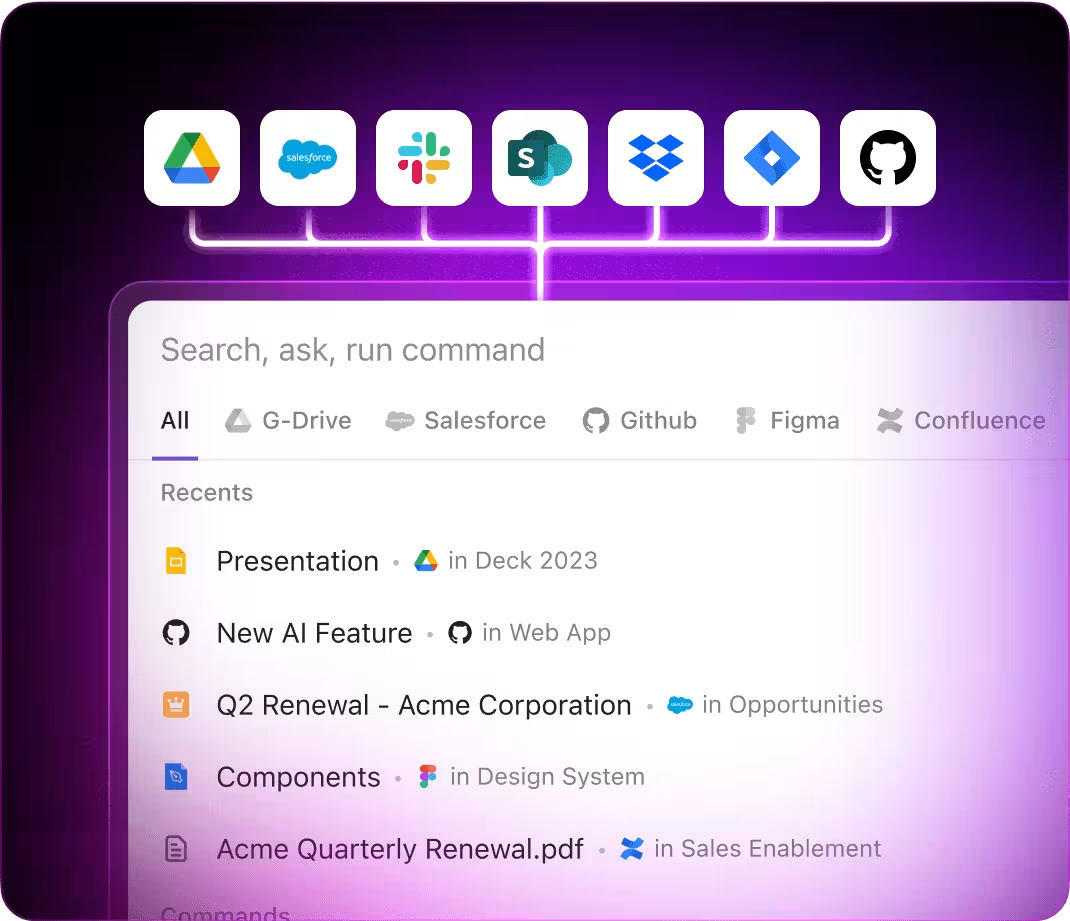
- Offers comprehensive search across all your operational tools
- Supports voice commands with Talk to Text for hands-free use
- Automatically selects the optimal AI model: GPT, Claude, Gemini
- Available as a native Mac & Windows app optimized for performance
15 Essential AI Prompts for OT Security Teams
Identify 5 security framework approaches for industrial control systems, based on the ‘OT Security Framework 2025’ document.
ClickUp Brain Behavior: Analyzes linked documents to extract and propose strategic security frameworks tailored for OT environments.
What network segmentation methods are currently favored in critical infrastructure OT setups across North America?
ClickUp Brain Behavior: Gathers insights from internal reports; Brain Max can supplement with relevant external data if accessible.
Draft a risk assessment plan for SCADA systems following guidelines in the ‘Risk Management Protocol’ and previous audit notes.
ClickUp Brain Behavior: Pulls key points from linked documents to create a structured and actionable risk assessment template.
Summarize performance benchmarks between Snort and Suricata IDS using our ‘IDS Evaluation Q2’ report.
ClickUp Brain Behavior: Extracts comparative data and presents a concise summary highlighting strengths and weaknesses.
Identify top endpoint security solutions used in OT environments, referencing R&D findings and vendor specifications.
ClickUp Brain Behavior: Scans internal documents to list prevalent tools along with their noted capabilities and limitations.
From the ‘NERC CIP Compliance’ document, create a checklist for mandatory security controls.
ClickUp Brain Behavior: Extracts regulatory requirements and formats them into a clear, actionable checklist within a task or document.
Outline 3 emerging authentication methods in OT systems from post-2023 security research and technology reviews.
ClickUp Brain Behavior: Identifies recurring themes and innovations from linked research materials.
From the ‘Operator Feedback Q1’ report, summarize key preferences for control panel interfaces.
ClickUp Brain Behavior: Reviews survey data to highlight common user interface desires and pain points.
Write concise and user-friendly alert copy for anomaly detection screens using the tone guidelines in ‘SecurityTone.pdf’.
ClickUp Brain Behavior: Extracts style cues from the document and generates multiple alert message options.
Highlight major changes in IEC 62443 standards for 2025 and their implications for system design.
ClickUp Brain Behavior: Synthesizes updates from internal compliance documents; Brain Max can add public regulatory insights if available.
Develop placement and sizing standards for security status indicators, referencing region-specific compliance documents.
ClickUp Brain Behavior: Extracts relevant rules and measurements from internal files to produce a compliance-focused guideline.
Build a step-by-step incident response checklist using US ICS-CERT 2025 protocols and our internal response plans.
ClickUp Brain Behavior: Parses protocol documents and organizes tasks by priority and incident phase.
Evaluate patch management strategies across Siemens, Schneider Electric, and Honeywell using our competitive analysis files.
ClickUp Brain Behavior: Summarizes documented approaches into an easy-to-digest comparison chart or brief.
What new security technologies are gaining traction in OT environments since 2023?
ClickUp Brain Behavior: Aggregates trend data from internal research summaries, whitepapers, and recent reports.
Highlight main usability challenges reported in Southeast Asia OT security feedback, including interface and alerting concerns.
ClickUp Brain Behavior: Extracts and ranks user-reported problems from surveys, feedback logs, and support tickets.
Operational Technology Security: Harnessing ClickUp Brain
ChatGPT Security Prompts
- Outline a 5-step risk assessment summary focusing on critical infrastructure vulnerabilities.
- Compose incident response communication templates emphasizing clarity and urgency.
- Propose 3 network segmentation strategies to enhance OT system isolation and resilience.
- Develop a detailed workflow for integrating anomaly detection in SCADA systems.
- Compare recent OT breach case studies and extract key prevention tactics for future protocols.
Gemini Security Prompts
- Design 3 dashboard layouts for real-time OT threat monitoring based on operator feedback.
- Suggest innovative alerting mechanisms prioritizing critical event visibility and operator response.
- Create a conceptual mood board for a secure control room interface highlighting usability and clarity.
- Recommend ergonomic workstation setups for security analysts to reduce fatigue and improve focus.
- Build a comparative table of OT security tools focusing on detection capabilities, integration, and scalability.
Perplexity Security Prompts
- Identify 5 emerging cybersecurity frameworks for OT environments and evaluate their applicability.
- Provide a comparative analysis of intrusion detection technologies tailored for industrial networks.
- Summarize global trends in OT threat intelligence sharing and adoption rates.
- List 5 innovative access control solutions for critical OT assets ranked by effectiveness.
- Review past OT cyber incidents and distill top 3 lessons to inform next-gen defense strategies.
ClickUp Brain Security Prompts
- Transform this incident report into prioritized remediation tasks with assigned owners and deadlines.
- Extract key action items from security audit notes and generate follow-up tasks within ClickUp.
- Evaluate annotated network diagrams and produce a checklist for compliance verification.
- Compile a task list from cross-department discussions on firewall policy updates including urgency levels.
- Summarize penetration test findings and create actionable bug fixes and improvement tasks in ClickUp.
Transform Initial Thoughts Into Clear Plans
- Convert scattered observations into detailed security protocols swiftly.
- Generate innovative strategies by analyzing previous incident reports.
- Build custom templates to accelerate your operational workflows.
Brain Max Boost: Quickly access historical security data, audit logs, and team notes to fuel your next safeguard plan.
Accelerate OT Security Coordination
- Break down intricate security protocols into manageable tasks.
- Transform vulnerability assessments into assignable action items.
- Automatically produce audit logs and incident summaries without extra effort.
Brain Max Boost: Instantly access historical threat data, device configurations, or compliance records across your operations.
Harness AI Prompts to Elevate Operational Technology Security
Instantly Develop Robust Security Strategies
Security teams explore diverse defense tactics quickly, make informed choices, and prevent analysis paralysis.