As an information security officer, staying ahead of potential threats and vulnerabilities is crucial to protect your organization's sensitive data. That's where ClickUp's Information Security Officers SWOT Analysis Template comes in handy!
This template allows you to conduct a comprehensive SWOT (Strengths, Weaknesses, Opportunities, and Threats) analysis of your information security programs, empowering you to:
- Identify and leverage your organization's strengths to enhance security measures
- Pinpoint weaknesses and areas for improvement to minimize risks
- Capitalize on emerging opportunities for innovation and growth in the information security landscape
- Mitigate potential threats and stay one step ahead of cyberattacks
With ClickUp's SWOT Analysis Template, you can confidently develop tailored strategies and policies to safeguard your organization's information and assets. Don't leave your security to chance, get started with ClickUp today!
Benefits of Information Security Officers SWOT Analysis Template
As an information security officer, using the SWOT analysis template can provide you with numerous benefits, including:
- Identifying and leveraging your organization's strengths in information security to maximize protection
- Identifying and addressing weaknesses in your current security measures to prevent potential breaches
- Identifying opportunities for improvement and staying ahead of emerging security threats
- Identifying potential threats and developing strategies to mitigate risks effectively
- Developing tailored strategies and policies to enhance your organization's information security program
- Ensuring compliance with industry standards and regulations
- Strengthening your organization's overall security posture and protecting sensitive data.
Main Elements of Information Security Officers SWOT Analysis Template
ClickUp's Information Security Officers SWOT Analysis template is the perfect tool to assess your security strategies and make informed decisions.
Here are the key elements of this template:
- Custom Statuses: Track progress with custom statuses such as To Do, In Progress, Pending Review, and Completed.
- Custom Fields: Utilize 4 custom fields including Worksheet Link, Completion Rate, Objective, and Timeline to organize and analyze your SWOT analysis data effectively.
- Task Views: Choose from a variety of views to gain different perspectives on your analysis, such as the Board view for a visual representation, Calendar view for a timeline overview, and Table view for detailed data analysis.
- Collaboration Tools: Enhance teamwork with features like task comments, mentions, and attachments to ensure seamless communication and documentation throughout the analysis process.
How to Use SWOT Analysis for Information Security Officers
If you're an Information Security Officer looking to assess your organization's strengths, weaknesses, opportunities, and threats, follow these steps to effectively use the SWOT Analysis Template:
1. Identify your objectives
Before you begin the SWOT analysis, clearly define your objectives. What do you hope to achieve with this analysis? Are you looking to improve your organization's security measures, identify areas of vulnerability, or explore new opportunities for growth? Knowing your objectives will help guide your analysis and ensure that you focus on the most relevant factors.
Use a Doc in ClickUp to list your objectives and keep them in mind throughout the analysis.
2. Assess your strengths
Start by evaluating your organization's internal strengths. What are you doing well in terms of information security? Are your security protocols robust? Do you have a skilled and knowledgeable team? Consider factors such as technology, resources, expertise, and processes. Identifying your strengths will give you a clear understanding of the areas where you excel.
Create tasks in ClickUp to list and categorize your organization's strengths.
3. Identify your weaknesses
Next, shift your focus to your organization's internal weaknesses. What are the areas where you could improve your information security practices? Are there any gaps in your processes or resources? Are there any skill or knowledge gaps within your team? Identifying your weaknesses will help you prioritize areas for improvement and allocate resources effectively.
Use the Board view in ClickUp to create a column for weaknesses and list them as separate cards.
4. Explore opportunities
Now, consider the external opportunities that could benefit your organization's information security efforts. Are there any emerging technologies or trends that you could leverage? Are there any partnerships or collaborations that could enhance your security measures? By identifying opportunities, you can proactively adapt and stay ahead of potential threats.
Create custom fields in ClickUp to track and prioritize external opportunities.
5. Assess threats
Finally, evaluate the external threats that could impact your organization's information security. Are there any regulatory changes or compliance requirements that you need to be aware of? Are there any emerging cyber threats or vulnerabilities that you should address? Understanding the potential threats will allow you to develop strategies to mitigate risks and protect your organization's sensitive information.
Use the Gantt chart in ClickUp to create a timeline for addressing and mitigating threats.
By following these steps and utilizing the Information Security Officers SWOT Analysis Template in ClickUp, you can gain valuable insights into your organization's information security landscape and develop strategies to enhance your security measures.
Get Started with ClickUp’s Information Security Officers SWOT Analysis Template
Information security officers can use this SWOT Analysis Template to assess the strengths, weaknesses, opportunities, and threats to their organization's information security programs.
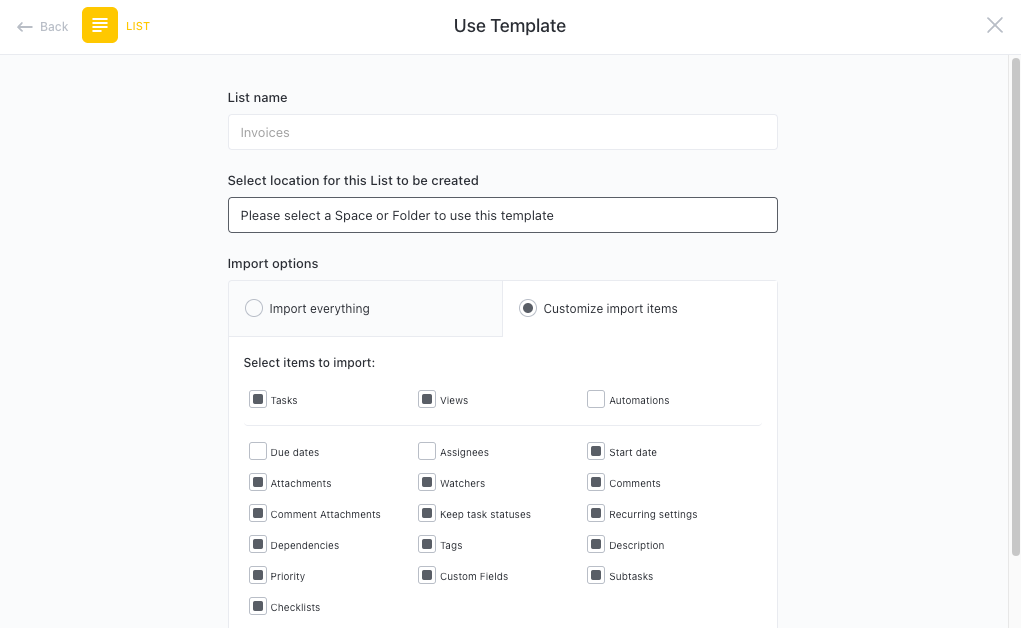
First, hit “Add Template” to sign up for ClickUp and add the template to your Workspace. Make sure you designate which Space or location in your Workspace you’d like this template applied.
Next, invite relevant members or guests to your Workspace to start collaborating.
Now you can take advantage of the full potential of this template to conduct a comprehensive SWOT analysis:
- Use the Strengths View to identify and document the internal factors that contribute to the organization's information security
- The Weaknesses View will help you identify and document the areas where the organization's information security is lacking
- Use the Opportunities View to identify and document the external factors that can be leveraged to improve the organization's information security
- The Threats View will help you identify and document the potential risks and challenges that may impact the organization's information security
- Organize your analysis into different statuses, such as Assessing, Analyzing, Implementing, and Reviewing to keep track of progress
- Update statuses as you progress through each phase of the SWOT analysis to ensure stakeholders are informed of progress
- Monitor and analyze the findings of the SWOT analysis to develop tailored strategies and policies for information security.








