Task Solution for Cybersecurity Experts
Task Management Software Tailored for Cyber Attack Monitoring
Centralize threat detection, coordinate response efforts, and maintain full visibility on every phase of your cyber defense operations.
Trusted by the best
Challenges in Cybersecurity Operations
Why Cyber Attack Monitoring Demands Robust Task Management
Operating without a unified system leads to missed alerts, fragmented intelligence, and operational confusion — turning critical tasks into overwhelming hurdles.
- Threat timelines become blurred — making it difficult to track incident status and response progress.
- Alert overload causes noise — irrelevant or duplicate alerts distract from real threats.
- Investigation steps lack consistency — scattered notes and missing logs hinder accurate analysis.
- Response coordination falters — unclear roles and communication gaps delay containment.
- Critical deadlines slip by — patching, reporting, and compliance timelines get overlooked.
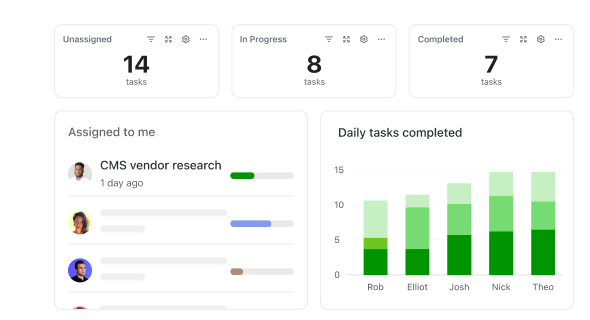
- Progress tracking is opaque — teams struggle to gauge incident resolution status.
- Communication silos form — fragmented channels hamper effective collaboration.
- Resource conflicts emerge — tool access, analyst availability, and task assignments clash, slowing response.
Conventional Approaches vs ClickUp
Why Legacy Cybersecurity Tools Fall Short
Discover how ClickUp delivers the control and clarity traditional tools lack.
Conventional Tools
- Alerts scattered across emails, tickets, and spreadsheets
- Incident notes and logs spread across platforms
- Manual tracking prone to errors and missed details
- Response roles and ownership unclear
- Deadlines for patches and compliance often missed
- Communication disjointed across channels
ClickUp Task Management
- Centralized task tracking with clear priorities and statuses
- Integrated alert and incident documentation
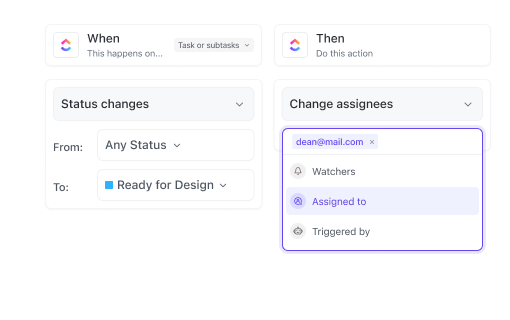
- Automated workflows and templates for consistent response
- Defined ownership with real-time team collaboration
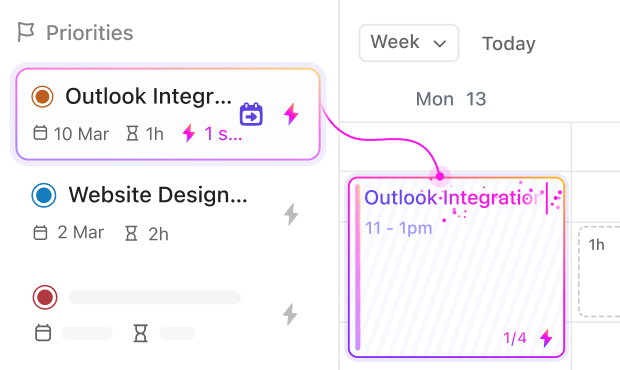
- Automated reminders and synced calendars for critical deadlines
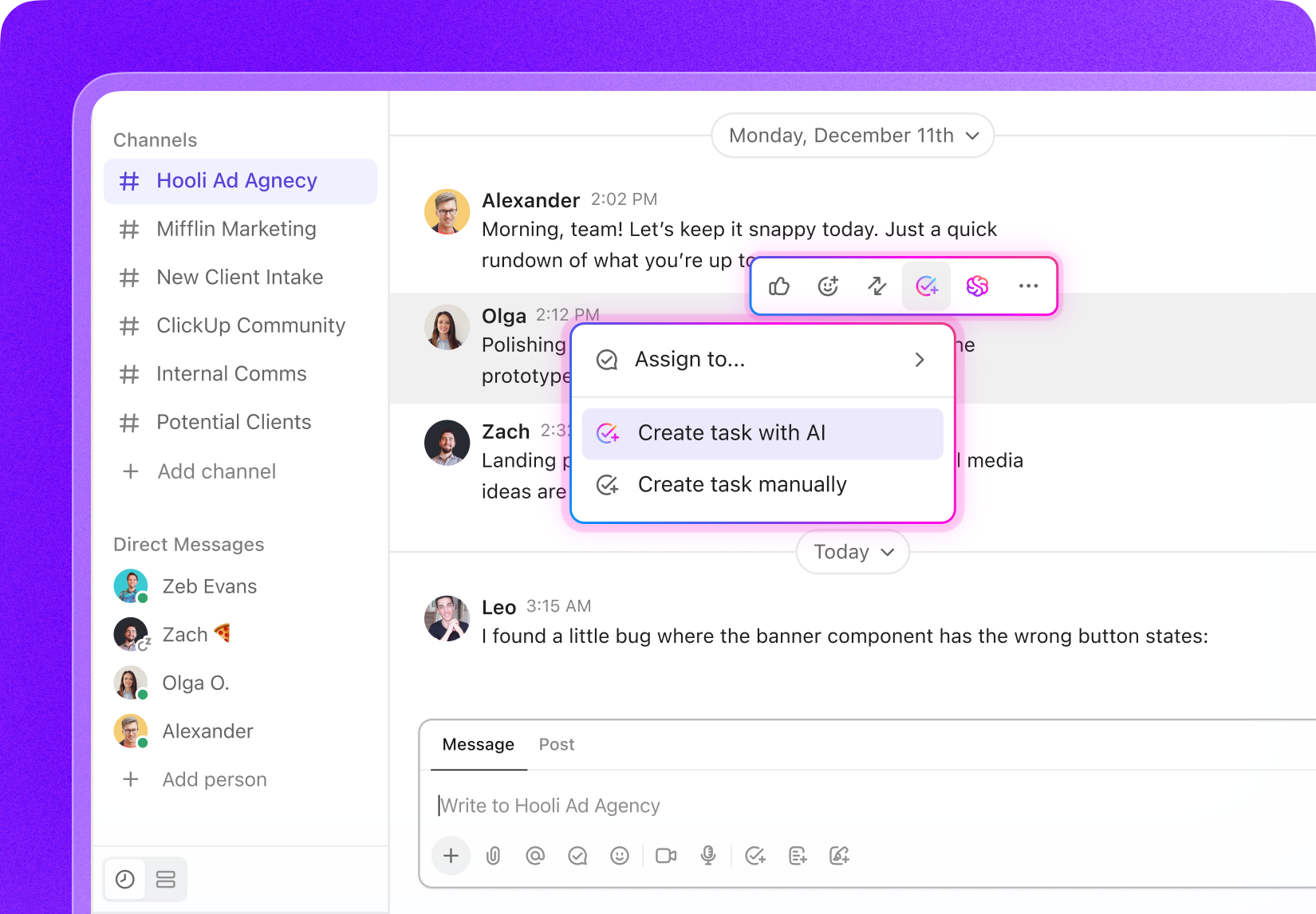
- Unified communication threads tied to tasks
Use cases
Unlocking Cyber Attack Monitoring Efficiency with Task Management
See how structured task tracking reduces confusion and accelerates response times.
#UseCase1
Consolidating Threat Intelligence and Alerts
Stop juggling scattered alerts and data feeds—ClickUp centralizes all intelligence, attaching logs and reports directly to relevant tasks or Docs.
#UseCase2
Maintaining a Transparent Incident Response Timeline
Ensure every action is logged and traceable—ClickUp keeps a comprehensive timeline of tasks, comments, and evidence from detection through resolution.
#UseCase3
Capturing Analyst Feedback and Investigation Notes
Analyst insights evolve rapidly, but ClickUp captures all feedback with comments, mentions, and version history to maintain context and clarity.
#UseCase4
Preventing Protocol Deviations During Incident Handling
Incident response templates, checklists, and dependencies in ClickUp ensure every step is followed precisely and documented for compliance.
#UseCase5
Tracking Compliance and Reporting Requirements
Manage regulatory deadlines and reporting workflows with custom fields, checklists, and automated reminders so nothing is overlooked.
#UseCase6
Streamlining Complex Forensic Analysis Workflows
Manage multi-stage forensic investigations with task dependencies and clear statuses to avoid premature actions and preserve evidence integrity.
#UseCase7
Meeting Patch Management and Vulnerability Remediation Deadlines
Track every vulnerability, remediation task, and deadline with Gantt views and centralized documentation to prevent security gaps.
#UseCase8
Reducing Alert Fatigue and Duplicate Investigations
ClickUp tracks alert investigations with tags and filters so teams avoid redundant work and focus on true threats.
#UseCase9
Turning Security Briefings into Actionable Tasks
Convert meeting discussions into clear tasks with owners, checklists, and deadlines to drive timely security improvements.
Key Beneficiaries
Who Benefits Most from ClickUp in Cyber Attack Monitoring
Designed for cybersecurity teams seeking unified visibility and streamlined operations.
If you’re a SOC Analyst
ClickUp helps you manage alerts, investigations, and incident escalations efficiently without losing context or missing critical steps.
If you’re a Threat Intelligence Specialist
Organize threat data, track analysis workflows, and coordinate with response teams seamlessly in one platform.
If you’re a Cybersecurity Manager
Gain oversight across teams, track compliance tasks, and ensure timely incident handling without juggling multiple tools.
How ClickUp Supports Your Cyber Defense
How ClickUp Accelerates Every Cyber Attack Monitoring Step
Manage incidents, vulnerabilities, and compliance without switching platforms.
Centralize Everything
Store literature, datasets, protocols, drafts, and grant docs in one workspace — no more scattered files.
Plan Research in Phases
Break projects into proposal, literature review, experiments, analysis, and writing with task lists and Gantt timelines.
Standardize Experiments & Fieldwork
Use templates and checklists for repeatable, error-free lab or field procedures.
Collaborate Across Teams
Assign tasks to co-authors, lab members, or collaborators. Shared boards and dashboards keep everyone aligned.
Turn Meetings Into Actionable Tasks
Convert supervisor or lab meetings into tasks with owners, checklists, and deadlines.
Stay on Top of Deadlines & Funding
Track grants, conferences, and submissions with automated reminders and calendars.