ClickUp for Threat Modeling Tasks
Master Threat Modeling with ClickUp
Identify, assess, and manage security risks proactively—streamline your threat modeling process without complex tools or fragmented workflows.
Trusted by the best
Threat Modeling Simplified
Why Choose ClickUp for Threat Modeling Tasks?
ClickUp consolidates everything you need to manage threat modeling efficiently. Here's what sets it apart:
- Unified Workspace: Map threats, vulnerabilities, and mitigations all in one place.
- Customizable Templates: Design threat models tailored to your architecture and environment.
- AI-Powered Analysis: Leverage ClickUp Brain to detect patterns and suggest risk prioritization.
- Collaborative Reviews: Facilitate team input with clear permissions and audit trails.
- Automated Follow-ups: Set reminders for risk mitigation tasks and monitor progress.
- Secure Data Handling: Keep sensitive security information protected and centralized.
- Integration Ready: Connect with your security tools and communication platforms.
- Scalable for Any Team: From startups to enterprise security operations centers.
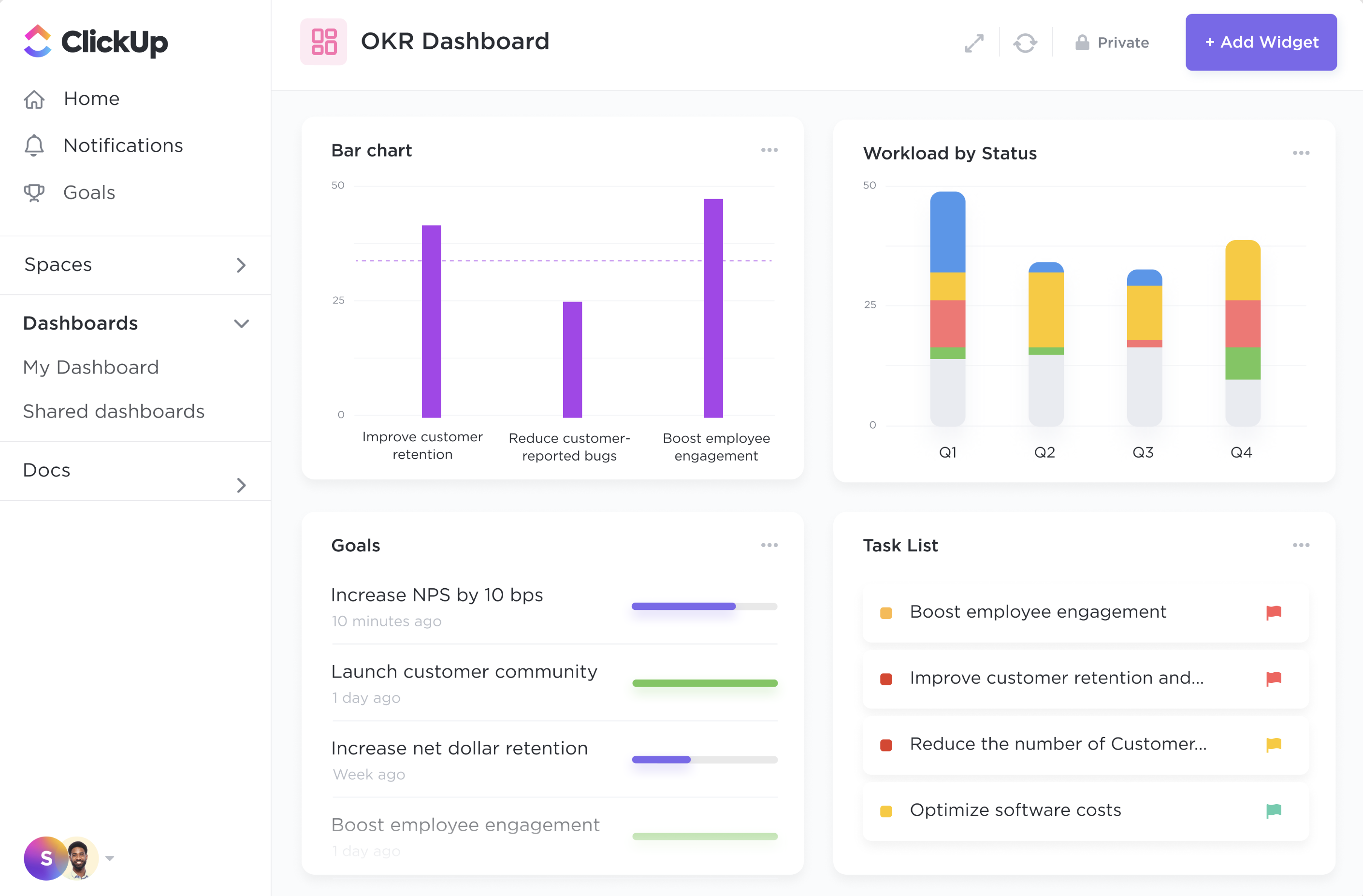
- Insightful Dashboards: Visualize risk status and threat trends with real-time metrics.
- Continuous Improvement: Turn threat insights into actionable security enhancements.
ClickUp vs Traditional Practices
Why ClickUp Transforms Threat Modeling Workflows
Comparing Conventional Methods with ClickUp's Modern Approach
Traditional Threat Modeling
- Disparate data across spreadsheets, docs, and emails complicate tracking
- Manual risk assessments consume extensive analyst time
- Static reports hinder collaborative updates and visibility
- Follow-up tasks and mitigations often missed or delayed
- Linking threats to security controls is inconsistent and error-prone
ClickUp
- Centralize all threat data, assessments, and mitigation plans in one platform
- Use AI insights from ClickUp Brain to prioritize and summarize risks rapidly
- Enable transparent collaboration with role-based access and comment threads
- Automate scheduling of mitigation reminders and compliance checks
- Connect threat models to compliance goals and security metrics effortlessly
Unlock Security Clarity
How ClickUp Elevates Your Threat Modeling Process
Organize, analyze, and remediate threats efficiently with a streamlined approach.
#HowClickUpHelps
Automated Risk Identification
- AI-Powered Detection: ClickUp Brain scans your inputs to highlight potential threat patterns.
- Custom Templates: Adapt models to your infrastructure and threat landscape.
- Real-Time Updates: Stay current with evolving risks and newly discovered vulnerabilities.
- Scheduled Reviews: Automate recurring threat assessments to maintain security posture.
#HowClickUpHelps
Comprehensive Risk Analysis
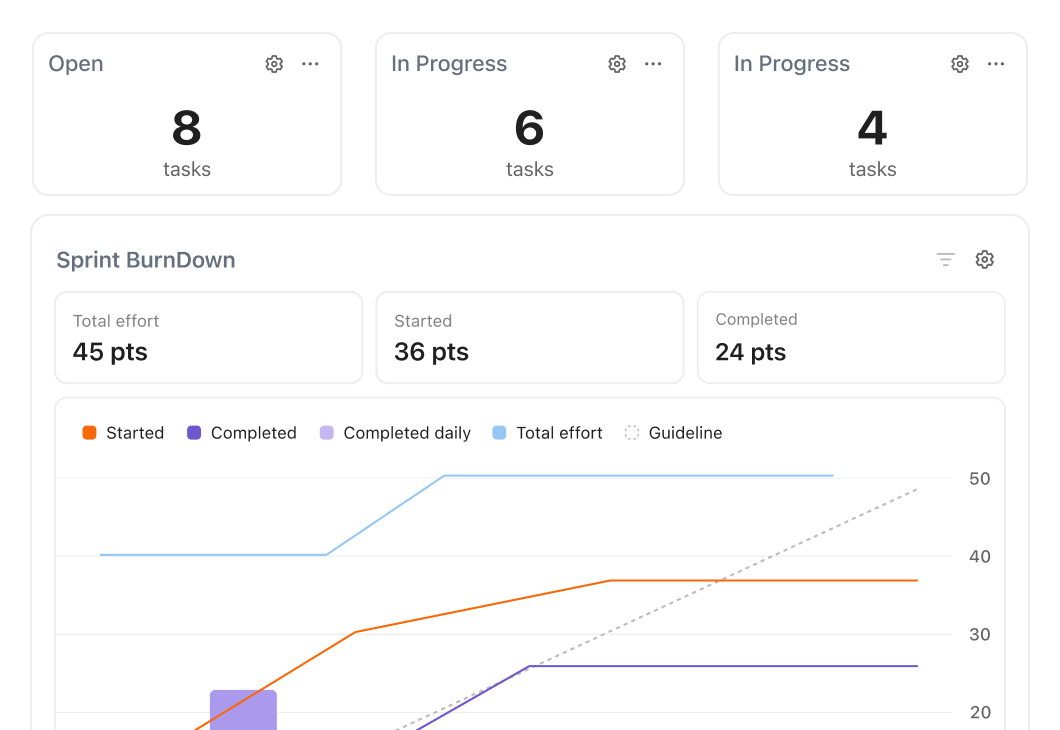
- Insightful Dashboards: Visualize risk levels and mitigation statuses across assets.
- Prioritization Tools: Rank threats by impact and likelihood using AI-driven scoring.
- Collaborative Comments: Facilitate team discussions directly within threat tasks.
- Link to Controls: Associate threats with security measures and compliance standards.
#HowClickUpHelps
Collaborative Mitigation Planning
- Assign Responsibilities: Designate tasks to security engineers, developers, and stakeholders.
- Track Progress: Monitor remediation efforts with clear timelines and dependencies.
- Alerts & Notifications: Receive real-time updates on mitigation status changes.
- Documentation Hub: Store all relevant evidence, policies, and reports in one place.
#HowClickUpHelps
Continuous Security Enhancement
- AI-Driven Recommendations: ClickUp Brain suggests next steps based on threat data.
- Goal Alignment: Tie threat mitigation to organizational security objectives.
- Performance Metrics: Measure improvements over time with detailed analytics.
- Audit Readiness: Prepare for compliance evaluations with automated reporting.
Key Beneficiaries
Who Gains the Most from Using ClickUp for Threat Modeling?
Identify the roles that benefit significantly from streamlined threat modeling.
Security Analysts
Turn Complex Data Into Clear Risk Insights
- Juggling multiple threat reports and sources is overwhelming. ClickUp Brain distills complex threat data into concise summaries, enabling focused risk management.
- Difficult to track mitigation progress across teams. Centralized dashboards provide real-time visibility into ongoing remediation efforts and outstanding risks.
Development Teams
Integrate Security Early and Stay Aligned
- Lack of visibility into security risks delays fixes. ClickUp links threat tasks to development workflows, ensuring timely mitigation.
- Security feedback often feels disconnected. Collaborative tools allow developers to discuss and resolve threats efficiently within ClickUp.
Implementation Blueprint
6 Steps to Master Threat Modeling with ClickUp
A structured approach to embed threat modeling seamlessly into your security operations.
1. Create Tailored Threat Templates
Design forms and checklists specific to your assets and risk profiles.
2. Map Threats and Vulnerabilities
Use custom fields and relationships to document and link threat components.
3. Assign Ownership Automatically
Leverage AI to distribute tasks to the right security and development team members.
4. Monitor Threat Status in Dashboards
Visualize risk levels, mitigation progress, and overdue items in real time.
5. Use AI to Analyze and Prioritize Risks
ClickUp Brain scans data to highlight critical threats and suggest remediation paths.
6. Automate Follow-Up and Reviews
Schedule reassessments and send reminders to keep your threat model current.