ClickUp for Shadow IT Discovery
Navigate Shadow IT with ClickUp: Your Guide to Discovery
Identify, monitor, and manage unauthorized technology use effortlessly—turn hidden risks into clear action plans without complex tools or guesswork.
Trusted by the best
Shadow IT Discovery
Why Choose ClickUp for Shadow IT Discovery?
ClickUp offers the comprehensive solution teams need to uncover and control Shadow IT effectively. Here's how:
- Unified Platform: Centralize all IT asset tracking and discovery tasks.
- Custom Workflows: Design processes tailored to your organization's security policies.
- AI-Powered Analysis: Leverage ClickUp Brain and Brain Max to detect unusual patterns and unauthorized software.
- Collaborative Visibility: Share findings securely among IT and security teams.
- Automated Alerts: Receive notifications for new or risky Shadow IT detections.
- Secure Data Management: Keep all discovery logs and reports in one protected place.
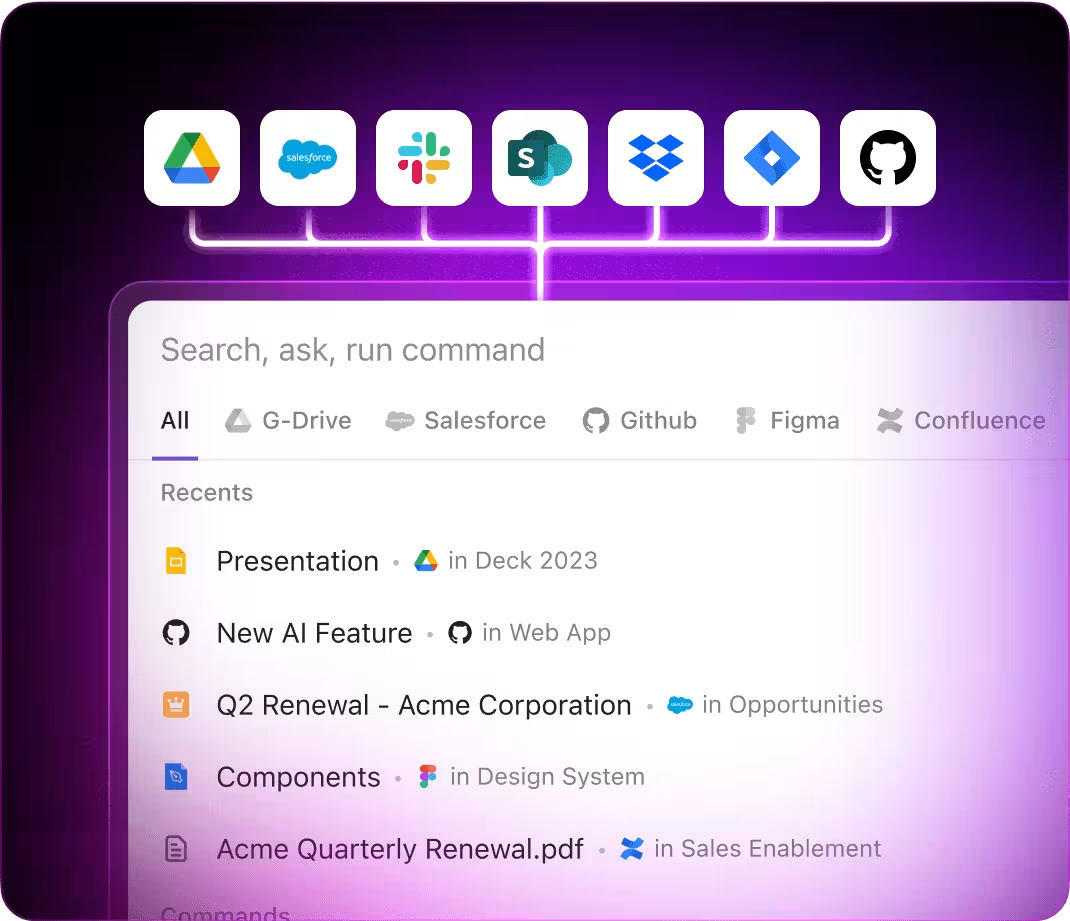
- Integrations: Connect with network monitoring, security tools, and communication apps.
- Scalable for Any Environment: Adaptable for startups to large enterprises.
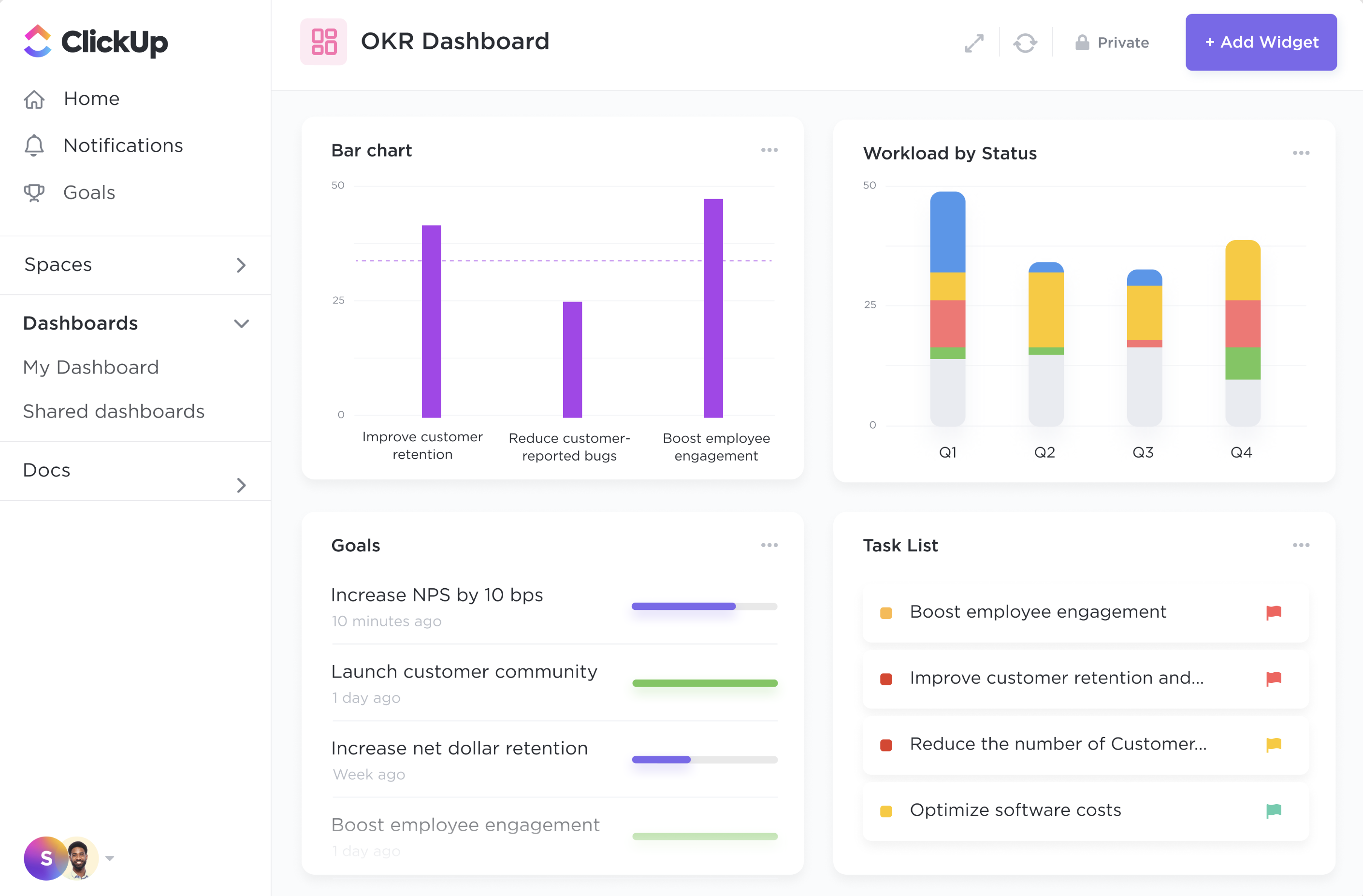
- Insightful Dashboards: Visualize Shadow IT trends and risk levels.
- Ongoing Compliance: Support audits with thorough documentation and follow-up workflows.
ClickUp vs Traditional Shadow IT Discovery
How ClickUp Elevates Shadow IT Detection Beyond Conventional Methods
A clearer, more efficient approach to managing Shadow IT risks
Traditional Methods
- Rely on manual audits and scattered spreadsheets leading to incomplete visibility
- Time-consuming data collection and analysis without automation
- Limited collaboration between IT and security teams, causing delays
- Reactive responses to incidents rather than proactive detection
- Fragmented tools that don't integrate well, increasing complexity
ClickUp
- Centralize discovery processes with customizable workflows and task management
- Utilize AI-driven insights from ClickUp Brain and Brain Max for rapid pattern recognition
- Enable real-time collaboration across teams with secure sharing and commenting
- Automate alerts and recurring scans to stay ahead of new Shadow IT threats
- Integrate seamlessly with key monitoring and security platforms for a unified defense
How ClickUp Supports You
Empower Your Team to Master Shadow IT Discovery with ClickUp
Stay ahead of hidden IT risks by streamlining discovery and management.
#HowClickUpHelps
Automated Detection Workflows
- Scheduled Scans: Set up recurring tasks to audit network devices and software.
- Custom Alerts: Get notified instantly when anomalies or unauthorized tools appear.
- AI-Powered Pattern Recognition: ClickUp Brain identifies suspicious activities across your IT environment.
- Dynamic Task Assignments: Automatically route findings to the right team members for swift action.
#HowClickUpHelps
Insightful Risk Analysis
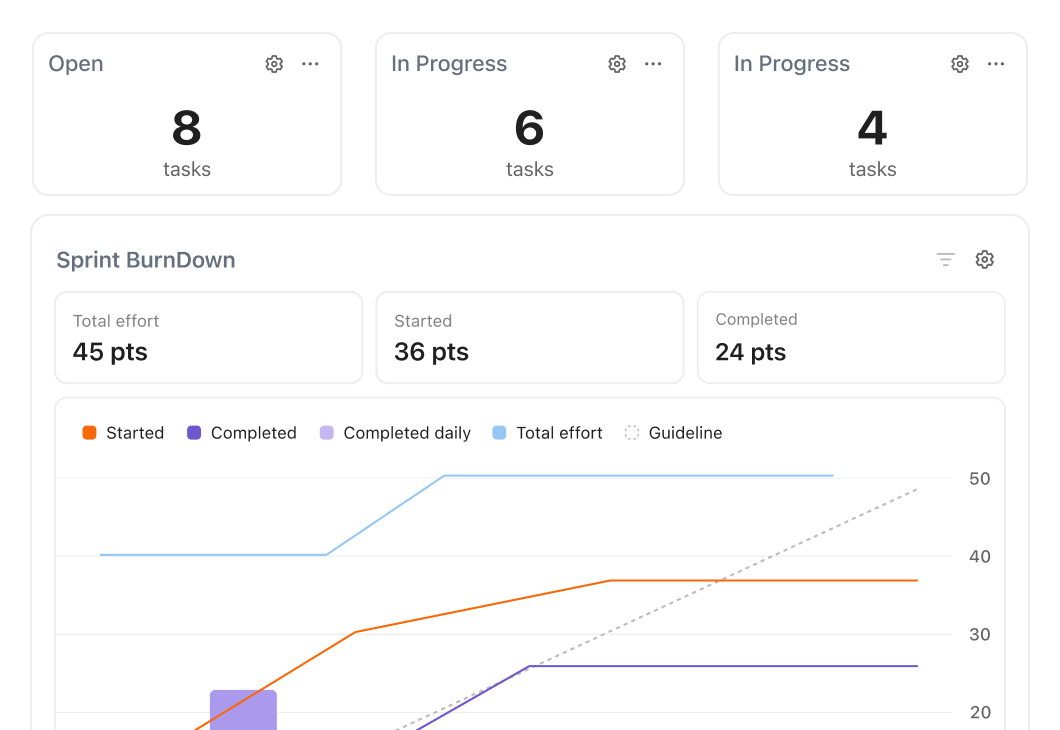
- Comprehensive Dashboards: Visualize Shadow IT trends and hotspots in real time.
- Brain Max Summaries: Generate concise reports highlighting key risks and mitigation steps.
- Prioritized Action Lists: Focus on the most critical issues with AI-driven ranking.
- Integrated Compliance Tracking: Monitor policy adherence and audit readiness effortlessly.
#HowClickUpHelps
Collaborative Incident Management
- Centralized Communication: Discuss findings, assign tasks, and track resolutions within ClickUp.
- Role-Based Access: Share sensitive data securely across IT, security, and management.
- Documentation & Audit Trails: Keep detailed logs of discovery processes and response actions.
- Real-Time Updates: Stay informed with instant notifications on task progress and changes.
#HowClickUpHelps
Proactive IT Governance
- Automated Policy Enforcement: Use workflows to ensure compliance with IT standards.
- Continuous Monitoring: Keep discovery ongoing with automated schedules and AI checks.
- Training & Awareness Tracking: Assign and monitor staff education on Shadow IT risks.
- Growth-Driven Insights: Leverage data to refine security strategies and reduce vulnerabilities.
Key Beneficiaries
Who Gains the Most from ClickUp's Shadow IT Discovery?
From IT teams to security officers, discover how ClickUp drives effective Shadow IT management
IT Managers
Gain Full Visibility and Control Over Shadow IT
- Manual tracking leads to missed risks. ClickUp Brain accelerates discovery by aggregating data and highlighting irregularities.
- Difficult to coordinate responses across teams. Central dashboards and task automation ensure timely remediation and accountability.
Security Analysts
Turn Discovery into Actionable Intelligence
- Analyzing scattered data wastes valuable time. Brain Max synthesizes findings into clear risk assessments.
- Lack of collaboration slows incident response. Secure shared spaces and comment threads keep teams aligned and informed.
Implementation Blueprint
Step-by-Step Process to Conduct Shadow IT Discovery in ClickUp
Follow these proven steps to uncover and manage unauthorized IT effectively.
1. Customize Discovery Templates
Create tailored checklists and forms for your network and software audits.
2. Automate Data Collection Tasks
Schedule recurring scans and assign tasks automatically to relevant teams.
3. Monitor Progress with Dashboards
Track audit completion, anomalies found, and response status in real time.
4. Leverage AI for Analysis
Use ClickUp Brain and Brain Max to interpret data and highlight potential risks.
5. Convert Insights into Tasks
Assign remediation actions, policy updates, and training through actionable tasks.
6. Maintain Continuous Oversight
Set up automated reminders and follow-ups to ensure ongoing compliance.