ClickUp Zero-Day Exploit Knowledge Base
Build a Robust Knowledge Base for Zero-Day Exploits
Centralize intelligence on zero-day vulnerabilities, mitigation strategies, exploit details, and patch statuses—so your security team always has the most current threat insights at hand.
Trusted by the best
ClickUp vs Traditional Security Tools
Why ClickUp Excels for Zero-Day Exploit Knowledge Management
Create a unified platform that evolves with your cybersecurity needs.
With traditional tools
- Intelligence scattered across multiple platforms causing delays
- Manual updates lead to outdated or inconsistent vulnerability data
- Limited integration with incident response and threat hunting workflows
- Rigid permission models complicate collaboration among teams
- Documentation maintenance is time-consuming and prone to errors
With ClickUp
- Consolidate threat data, tasks, and collaboration in one workspace
- Instantly convert intelligence gaps into actionable tasks
- Link exploit data directly to incidents, patches, and investigations
- Flexible access controls for internal teams, partners, and stakeholders
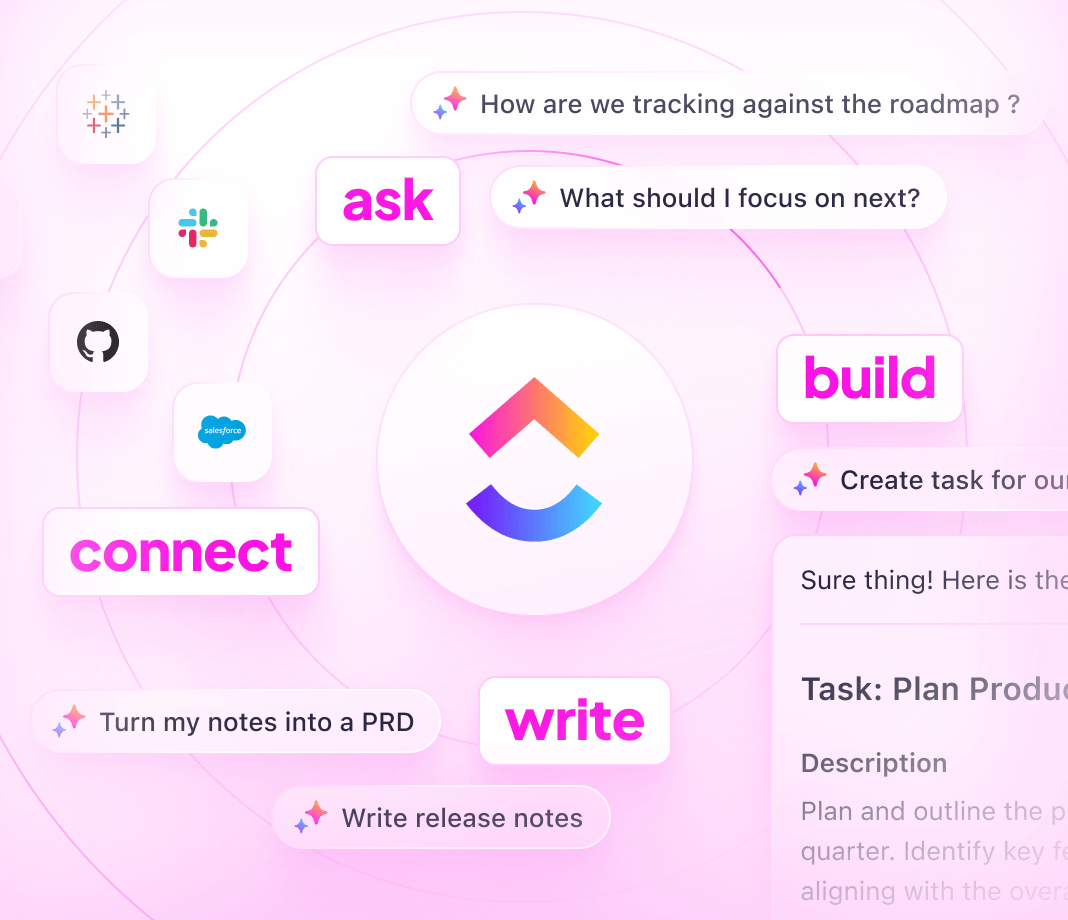
- AI-powered drafting, summarization, and threat analysis speed response
Steps to build your knowledge base
How to create a zero-day exploit knowledge base with ClickUp
Follow this 6-step approach to keep your threat intelligence structured, actionable, and current.
1. Identify your stakeholders and intelligence objectives
- Define who needs access: analysts, incident responders, management
- Clarify goals: detection, mitigation, documentation, reporting
- Assign clear ownership to maintain data quality and relevance
2. Develop a clear, navigable knowledge base framework
- Organize by exploit category, severity, affected assets, and status
- Include sections for initial discovery, analysis, mitigation, and follow-up
- Ensure easy navigation with tables of contents and subpages
3. Standardize exploit documentation for consistency
- Use uniform templates covering exploit description, indicators, impact, and remediation
- Document detection methods and CVE references
- Include real-world attack scenarios to aid understanding
4. Integrate investigative guides and response protocols
- Provide step-by-step incident handling procedures
- Include troubleshooting for detection and containment challenges
- Centralize communication templates and escalation paths
5. Link knowledge base updates to threat intelligence cycles
- Connect documentation to threat feeds, patch releases, and security alerts
- Treat updates as part of operational workflows, not afterthoughts
- Maintain accuracy as exploits evolve or new variants emerge
6. Manage permissions and continuously review content
- Control access for internal teams, external partners, and auditors
- Schedule regular reviews and incorporate user feedback
- Archive deprecated exploits and update mitigation strategies
Harness the power of ClickUp Knowledge Base
How ClickUp empowers your zero-day exploit knowledge management
Maintain structured intelligence, clear ownership, and real-time alignment with security operations.
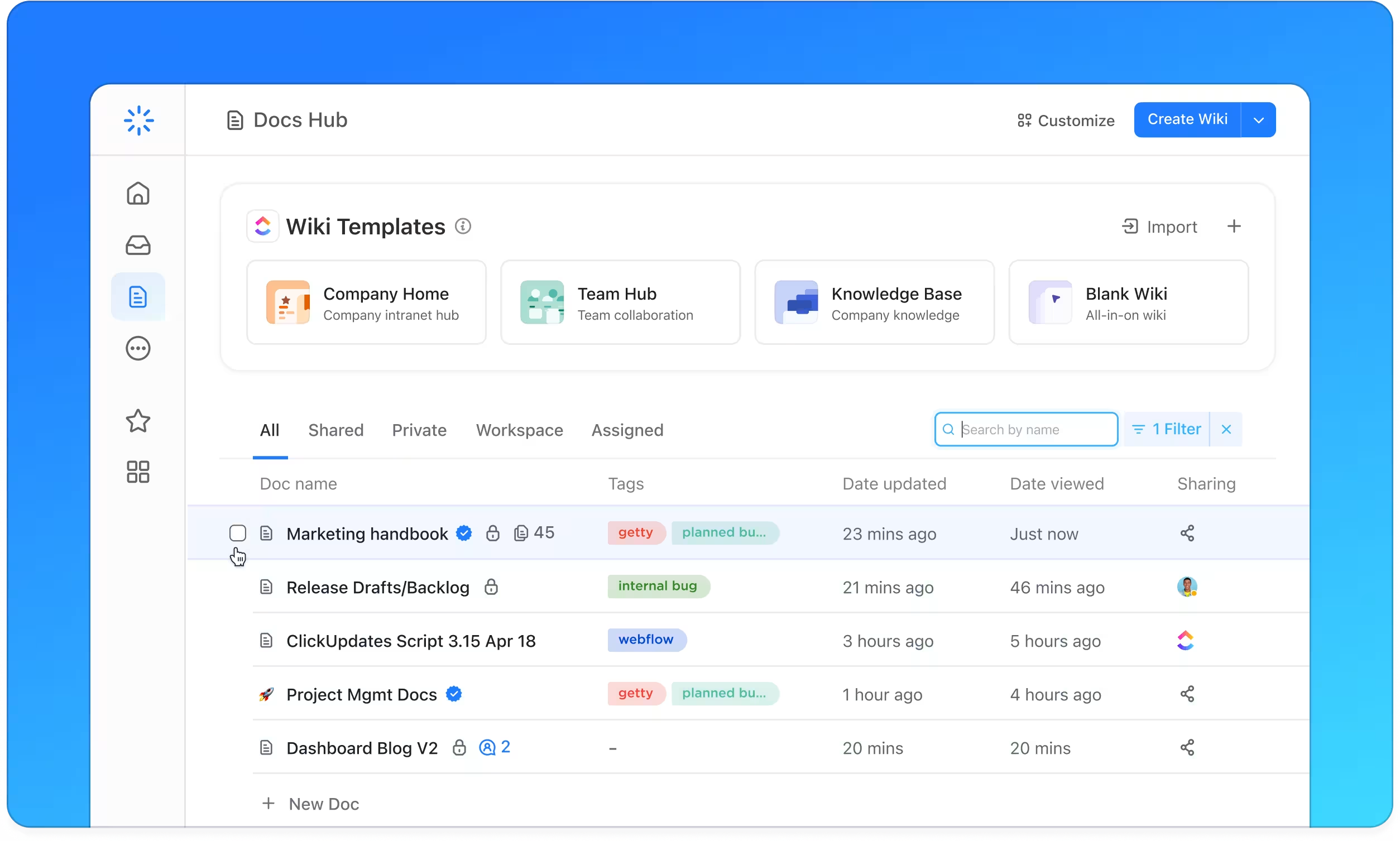
Organize
Structured zero-day exploit intelligence with ClickUp Docs
- Categorize exploits by type, severity, affected systems, and lifecycle stage
- Use comprehensive tables of contents and nested pages for quick reference
- Apply consistent documentation templates for clarity
Why it matters: Analysts find critical information faster, reducing time to response.
Accountability
Clear ownership with actionable tracking
- Convert intelligence gaps into assigned tasks with due dates
- Define owners for documentation sections and reviews
- Monitor updates and progress alongside incident workflows
Why it matters: Knowledge stays current because responsibility is visible and managed.
Synchronize
Documentation linked directly to threat response events
- Associate exploit details with incident tickets, patch deployments, and alerts
- Track feedback from investigations and postmortems
- Ensure documentation evolves with real-world threat dynamics
Why it matters: Intelligence remains relevant and actionable as threats change.
Zero-day exploit knowledge base FAQs