Privileged Access Management Knowledge Base
Build a Centralized Knowledge Base for Privileged Access Management
Create a unified, searchable repository for policies, procedures, user roles, audit logs, and incident responses—so your security team always accesses the most current and compliant information.
Trusted by the best
ClickUp vs Traditional Solutions
Why Choose ClickUp for Your Privileged Access Management Knowledge Base
Consolidate access knowledge and governance in one adaptable workspace.
Traditional PAM Tools
- Documentation is siloed and quickly outdated
- Manual updates depend on individual memory
- Access policies disconnected from operational workflows
- Permissions duplication leads to errors and inefficiencies
- Time-consuming manual creation and revisions
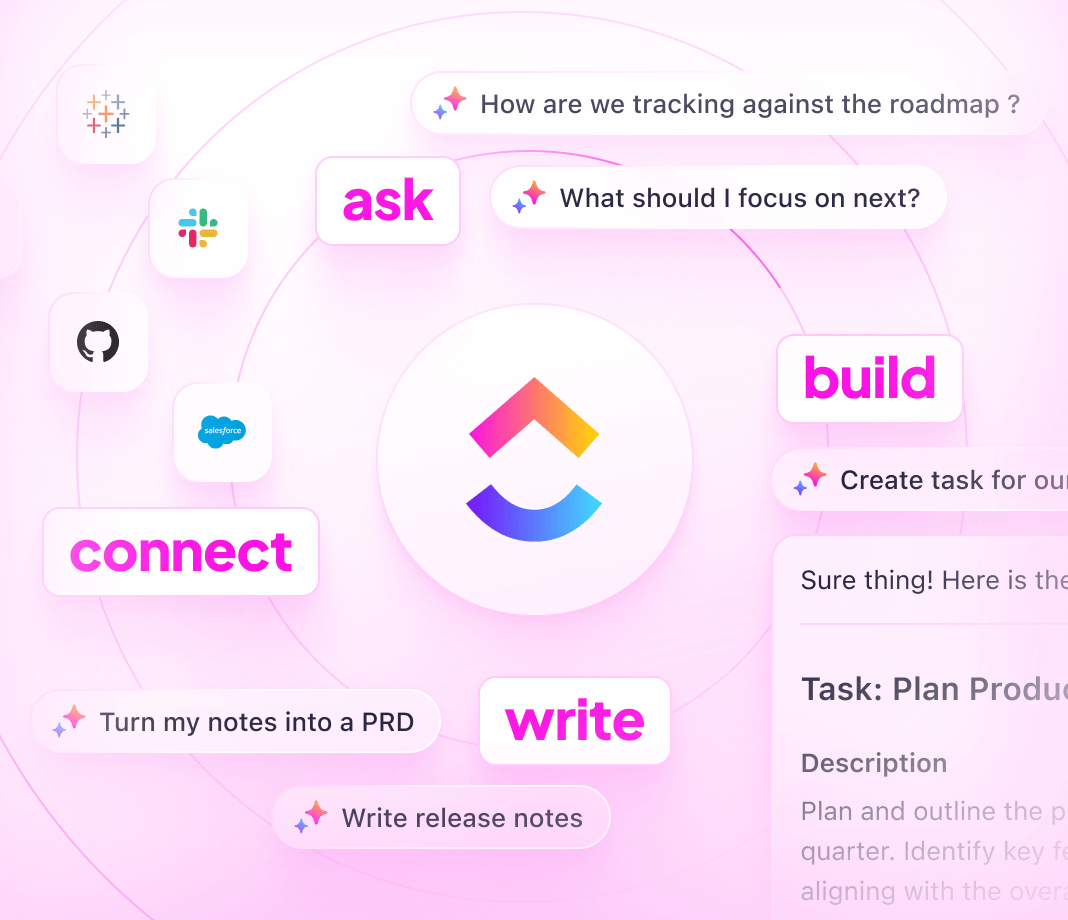
ClickUp’s Approach
- Integrates knowledge with execution (Docs, tasks, comments)
- Automatically converts documentation gaps into actionable tasks
- Links policies directly to access requests and audits
- Granular access controls for internal teams and external auditors
- AI-powered drafting, summarization, and troubleshooting accelerates upkeep
Building Your PAM Knowledge Base
Steps to Develop a Privileged Access Management Knowledge Base
Follow this 6-step framework to keep your access policies organized, discoverable, and compliant.
1. Identify stakeholders and define PAM knowledge objectives
- Determine users such as security teams, auditors, and system admins
- Outline key policy areas: access controls, credential management, incident protocols
- Assign responsibility for content accuracy and updates
2. Design a clear knowledge base structure
- Create a centralized hub with intuitive navigation
- Include sections like access policies, user roles, audit procedures, and compliance standards
- Maintain changelogs for policy revisions and deprecations
3. Standardize documentation formats for consistent PAM content
- Use templates covering policy purpose, scope, approval workflows, and exceptions
- Document authentication methods, authorization levels, and escalation paths
- Address common scenarios and edge cases to minimize confusion
4. Incorporate real-world guidance and troubleshooting steps
- Develop step-by-step guides for privilege requests and revocations
- Add troubleshooting tips for access denials and audit findings
- Centralize best practices for credential rotation and emergency access
5. Keep your PAM knowledge base current by linking to workflows
- Connect documentation updates to audit cycles, incident responses, and policy reviews
- Treat knowledge upkeep as an ongoing operational priority
- Ensure policies evolve alongside organizational changes
6. Manage permissions and sustain knowledge quality over time
- Establish access controls for internal teams, partners, and auditors
- Maintain detailed logs and version histories
- Solicit feedback and perform regular content audits to prevent drift
How ClickUp Supports Your PAM Efforts
Unlock the Power of ClickUp for PAM Knowledge Management
Ensure your privileged access documentation is organized, owned, and synchronized with security operations.
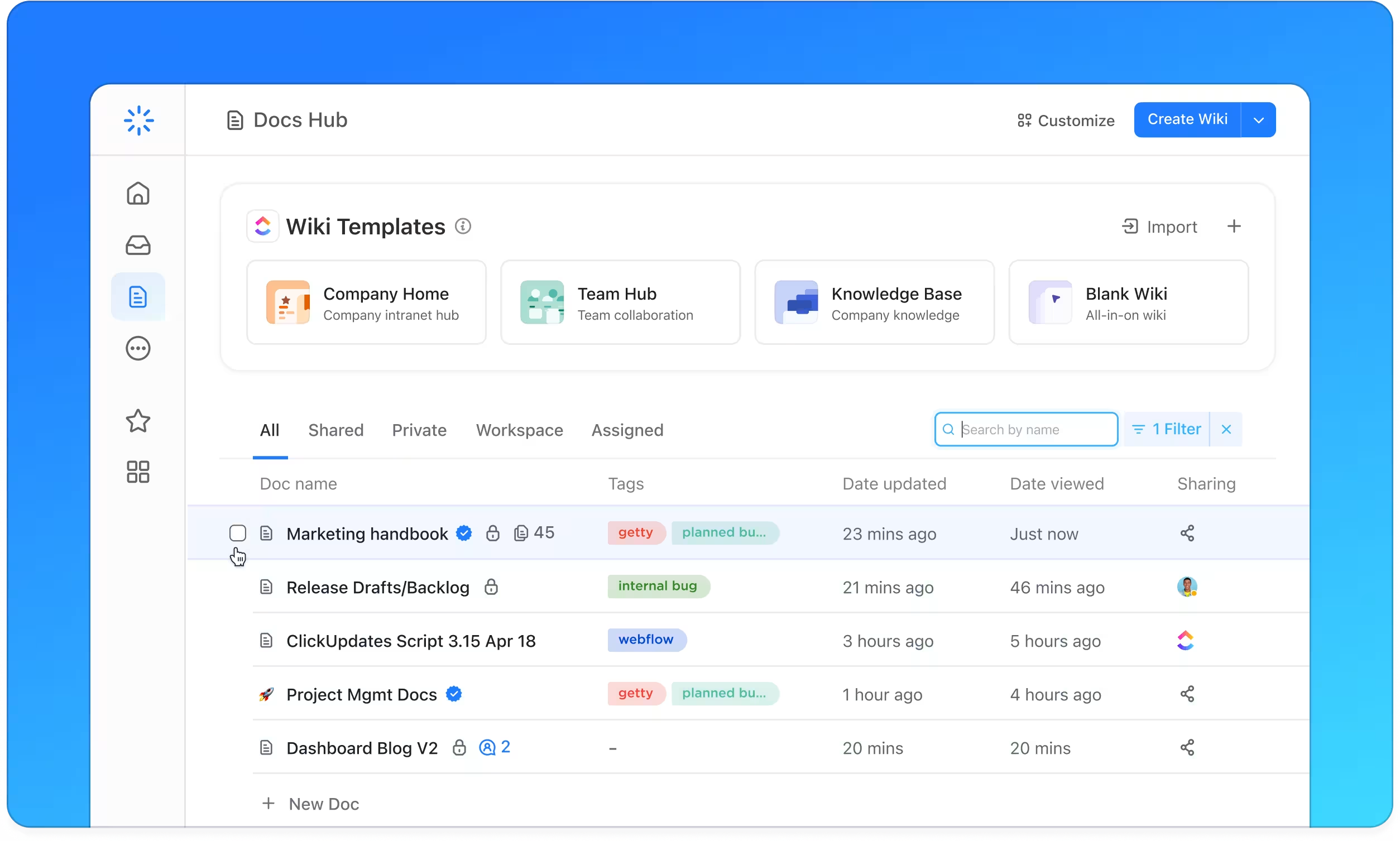
Organize
Structured PAM Documentation with ClickUp Docs
- Access policies, user roles, audit logs, incident response plans
- Table of contents with nested pages for easy navigation
- Consistent policy templates across all documentation
Why it matters: Teams find critical information quickly, reducing risk and improving compliance.
Manage
Clearly Assigned Ownership and Review Processes
- Identify content owners and set review schedules
- Convert documentation gaps into tasks with deadlines
- Monitor progress using familiar task management tools
Why it matters: Accountability ensures your knowledge base remains accurate and trustworthy.
Integrate
Connect Documentation to Security Workflows and Audits
- Link policies to access requests, audit findings, and incident reports
- Align documentation updates with compliance cycles
- Capture feedback and support issues directly within docs
Why it matters: Documentation stays current and relevant as your security posture evolves.
ClickUp PAM Knowledge Base