Secure Your Operations with Advanced CRM Software
Why Security Operations Centers Rely on CRM Software
Managing security threats and response workflows without a CRM is like trying to defend your network blindfolded. Critical details slip through the cracks fast.
Here’s what often breaks down when SOCs rely on manual tracking:
- Incident response gets delayed — unclear ownership and fragmented communication slow down resolution.
- Threat intelligence becomes disorganized — vital contacts and indicators scattered across tools.
- Vendor and partner coordination falters — no centralized record of agreements, escalations, or updates.
- Audit trails are incomplete or missing — complicating compliance and post-incident reviews.
- Team collaboration feels disconnected — information silos and missed handoffs.
- Onboarding new analysts is inefficient — no comprehensive history or context available.
- Communication spans emails, chats, and spreadsheets — making it hard to reconstruct timelines.
- Alert fatigue increases — no streamlined tracking and prioritization of ongoing cases.
Why Traditional Security Tools Fall Short Compared to ClickUp CRM
Legacy Security Tools
- Contacts and incidents scattered across emails and spreadsheets
- No centralized incident history or communication logs
- Limited visibility into threat lifecycle
- Manual tracking of vendor interactions
- Fragmented audit and compliance records
- No automated follow-ups or reminders
- Siloed team collaboration
- Difficult onboarding for new analysts
ClickUp CRM
- Centralize all security contacts and threat data in one platform
- Log communications, decisions, and evidence in detailed timelines
- Visualize incident and threat progression with pipelines
- Automate alerts, statuses, and vendor follow-ups
- Link tasks, comments, and investigation steps seamlessly
- Gain comprehensive dashboards for threat and response management
- Attach files and logs directly to CRM records
- Set automatic reminders to prevent missed actions
How CRM Software Elevates Security Operations Centers
Centralizing Incident and Threat Stakeholders
Managing Incident Response Pipelines
Automating Vendor and Partner Communications
Preserving Audit Trails & Compliance Records
Coordinating Multi-Shift & Remote Teams
Tracking Security Tools and Asset Vendors
Integrating Threat Intelligence Sources
Enhancing Incident Debriefings and Lessons Learned
Turning Alerts Into Coordinated Actions
Who Benefits Most from ClickUp CRM in Security Operations Centers
Tailored for SOC analysts, incident managers, threat intelligence teams, and security vendors overwhelmed by fragmented data and workflows.
For Incident Response Teams Across Multiple Locations
For Security Analysts Monitoring Threats
For SOC Managers Coordinating Vendors and Partners
How ClickUp CRM Transforms Security Operations Workflows
Create a Comprehensive Security Contact Repository
Store analysts, vendors, partners, and threat intelligence sources with detailed activity logs.
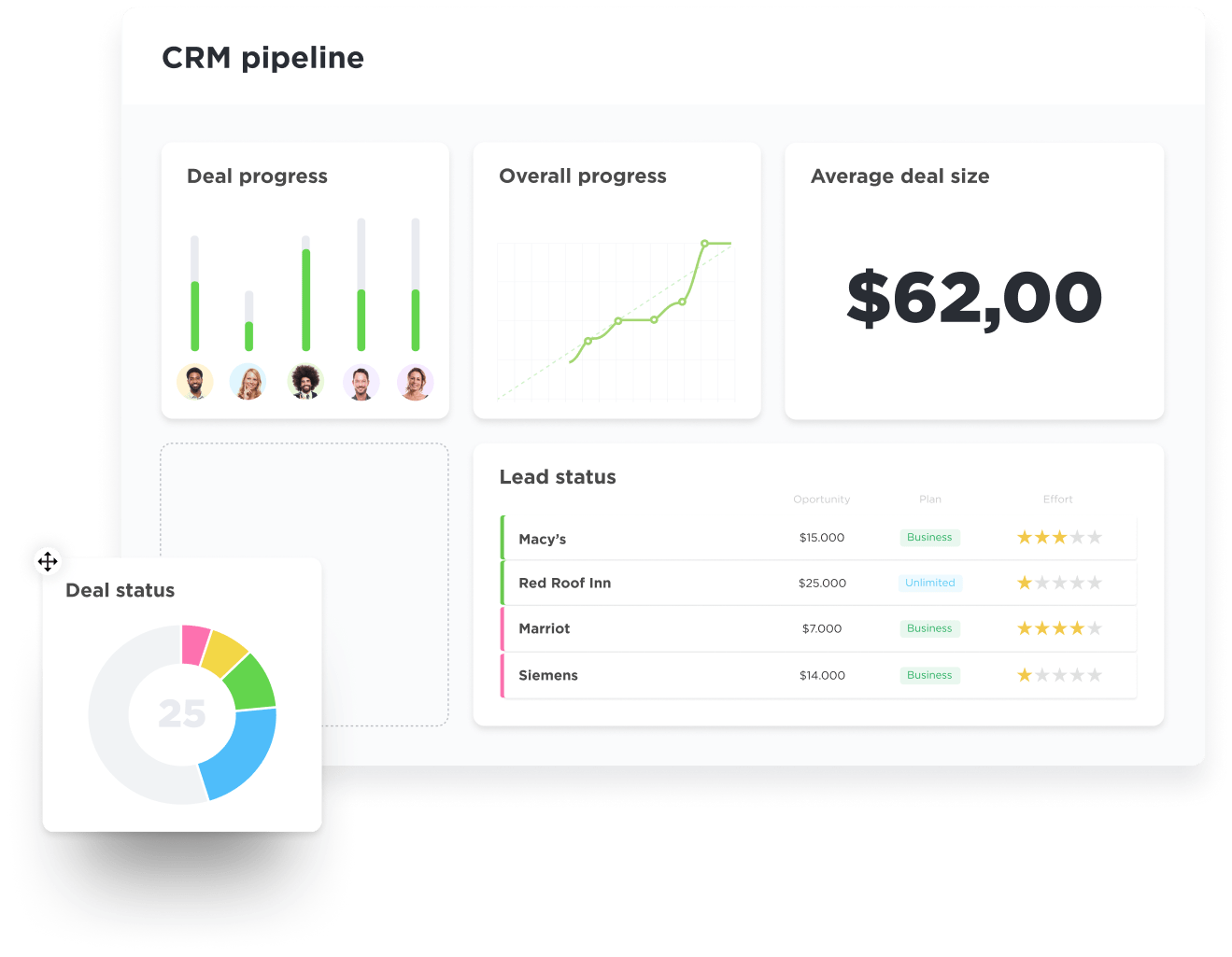
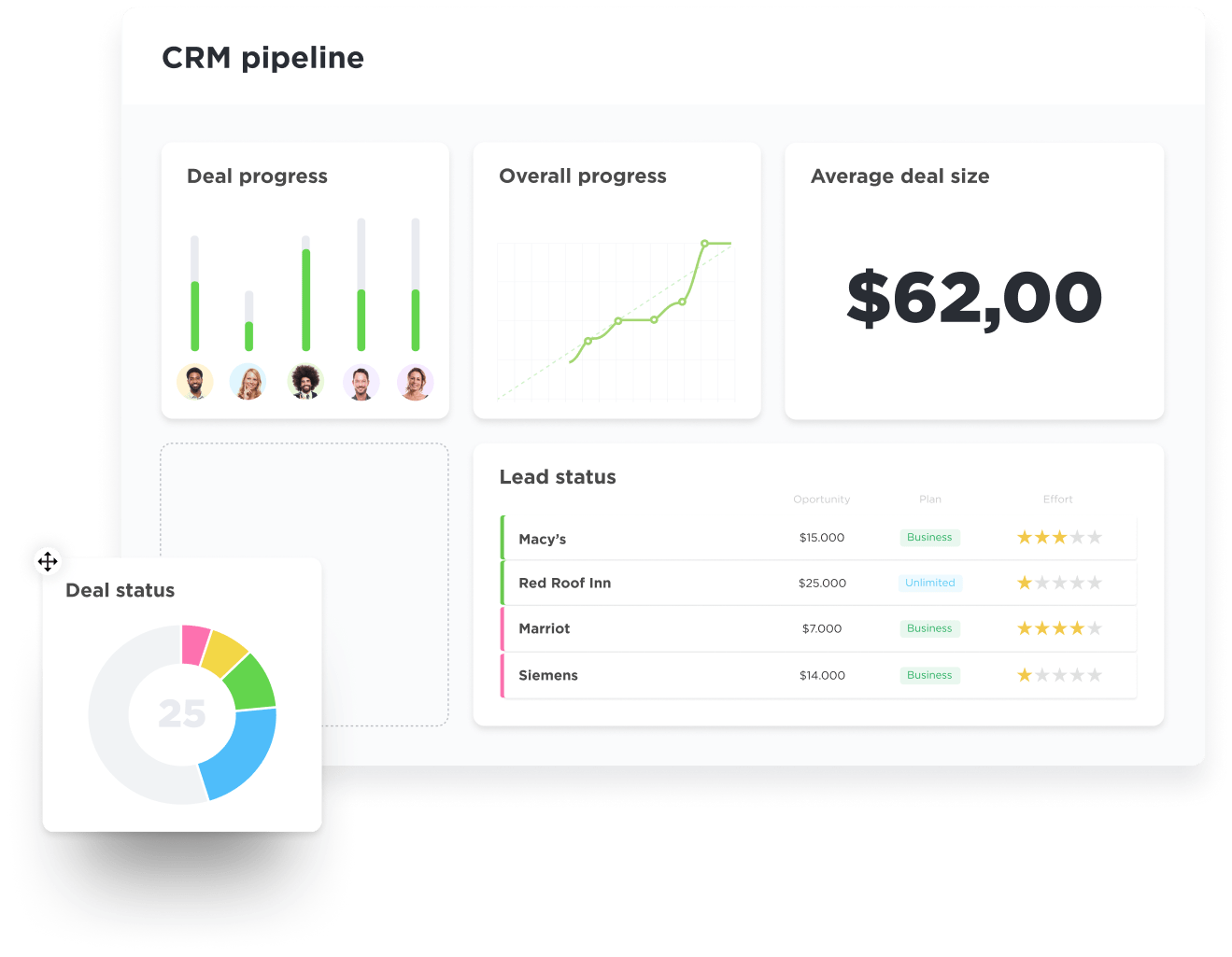
Visualize Incident and Threat Progression
Use customizable pipelines to track investigation stages, response priorities, and resolution timelines.
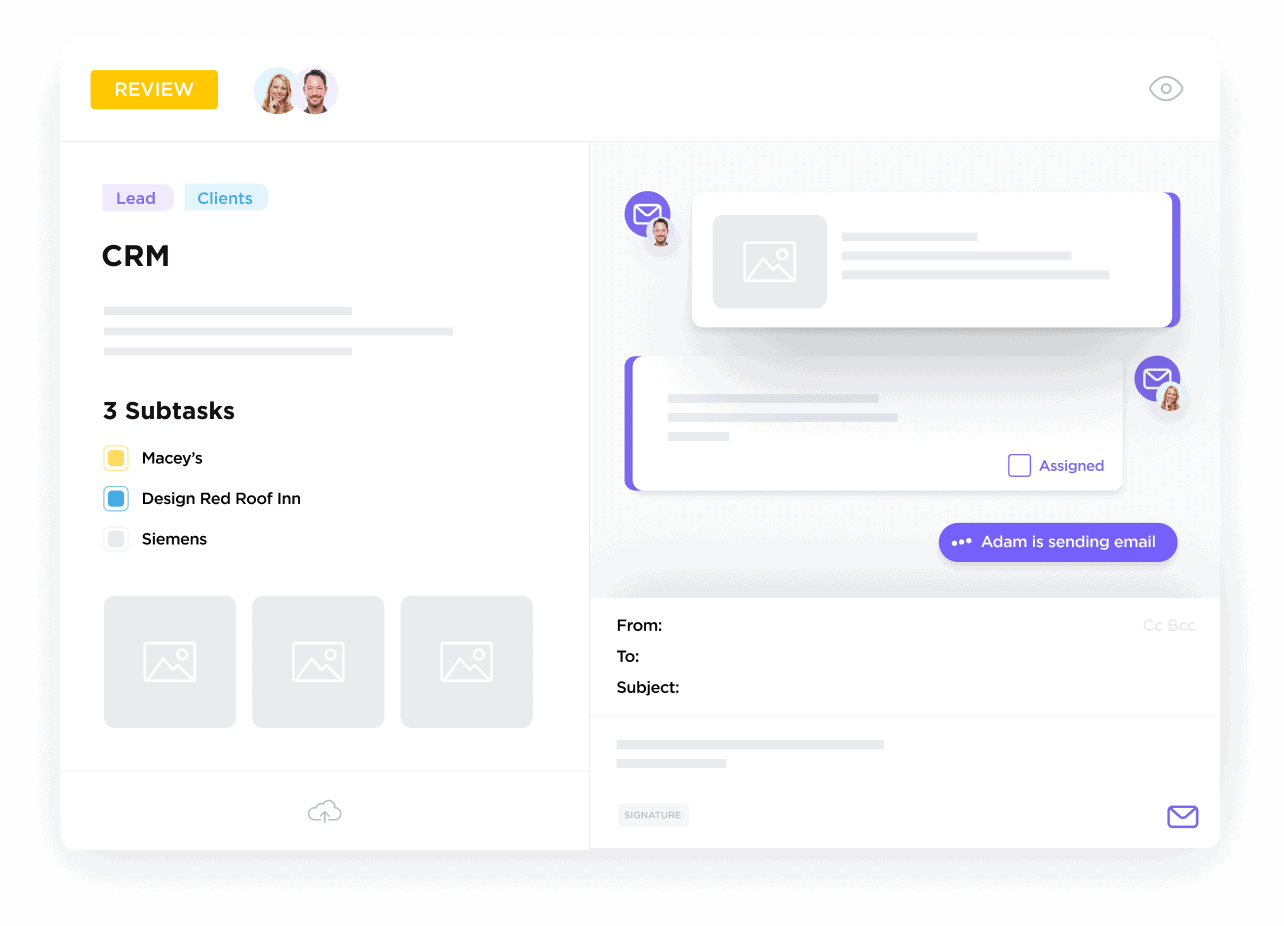
Log Communications and Evidence Seamlessly
Attach emails, call notes, logs, and files directly to incident records to maintain context.
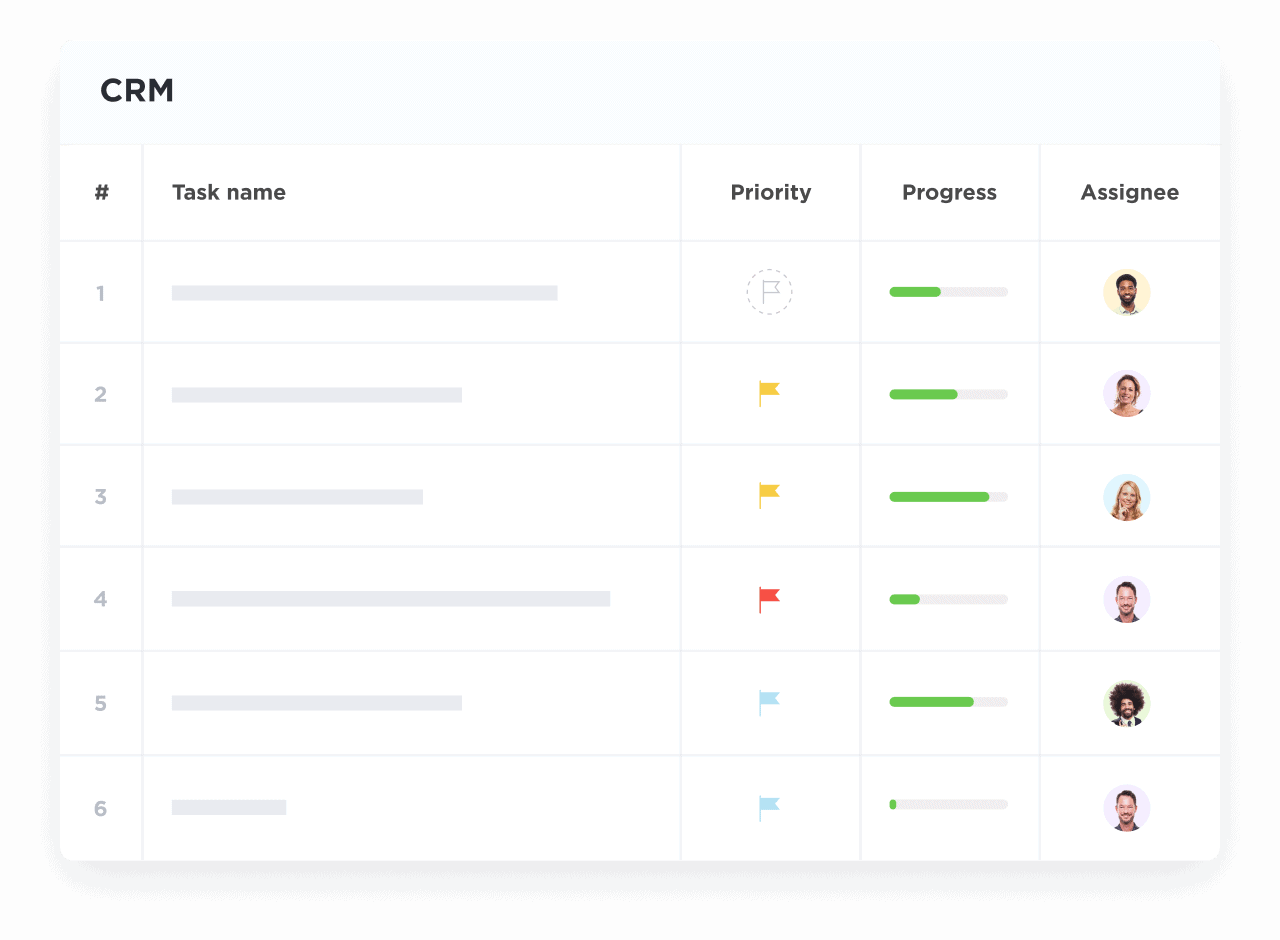
Convert Alerts into Actionable Tasks
Assign follow-ups with owners, deadlines, and automated reminders to drive accountability.
Integrate Documentation and Compliance Artifacts
Attach policies, audit reports, and regulatory documents to relevant cases for easy reference.
Stay Ahead with Dashboards and Reminders
Monitor open incidents, vendor SLAs, and team workloads to prevent lapses and bottlenecks.