Top AI Prompts for Network Security Teams
AI Prompts Revolutionizing Network Security Workflows
Protecting digital assets today demands more than reactive measures—it requires proactive, intelligent coordination.
From threat detection and vulnerability assessment to incident response and compliance audits, network security teams juggle countless alerts, reports, and protocols. AI prompts are now critical in managing this complexity.
Security teams leverage AI to:
- Quickly identify emerging threats and attack patterns
- Generate detailed vulnerability reports with minimal manual effort
- Interpret complex compliance requirements and standards
- Transform raw security logs into prioritized action plans and tickets
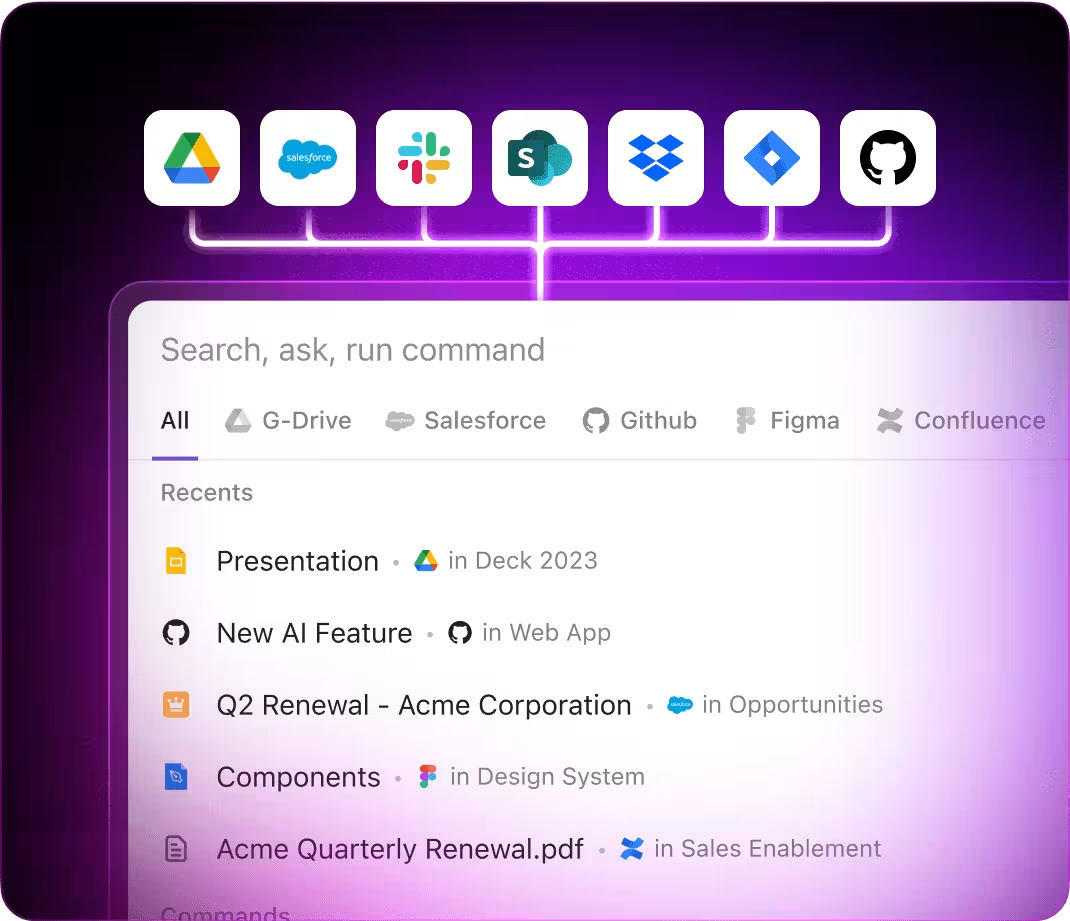
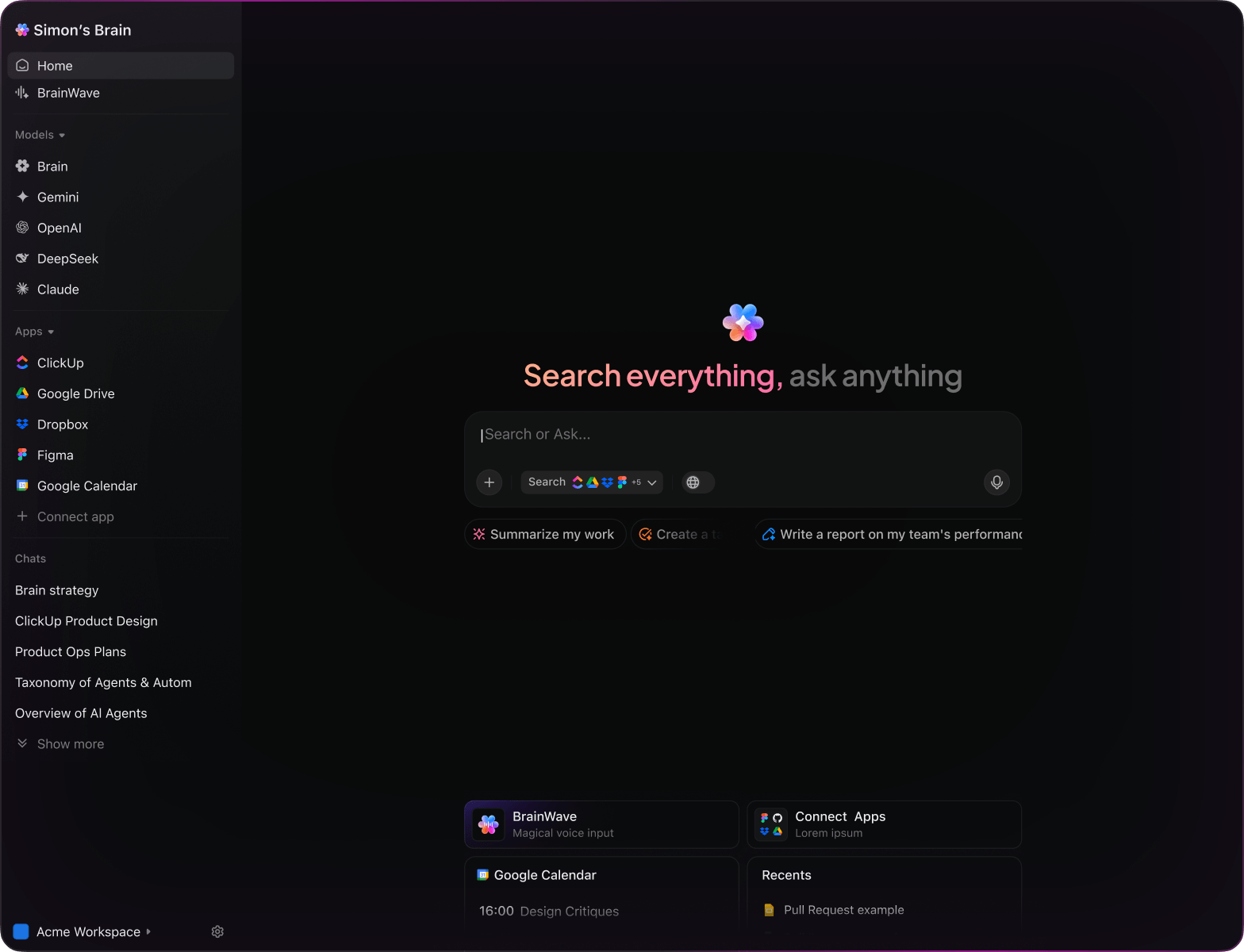
Integrated within familiar tools—such as documentation, dashboards, and task trackers—AI in platforms like ClickUp Brain acts as a strategic partner, converting scattered security data into clear, prioritized workflows.
Why ClickUp Brain Stands Out
Conventional AI Platforms
- Constantly toggling between apps to collect info
- Repeating your objectives with every query
- Receiving generic, irrelevant feedback
- Hunting through multiple systems for a single document
- Interacting with AI that only processes input
- Manually switching between different AI engines
- Merely a browser add-on without deep integration
ClickUp Brain
- Deeply connected to your projects, notes, and team activity
- Retains your previous interactions and targets
- Provides insightful, context-driven solutions
- Consolidated search spanning all your resources
- Voice command enabled with Talk to Text
- Automatically selects optimal AI: GPT, Claude, Gemini
- Dedicated Mac & Windows apps optimized for performance
15 Essential AI Prompts for Network Security Teams
Identify 5 emerging external threat vectors targeting enterprise networks, based on the ‘Q2 Threat Intelligence’ report.
ClickUp Brain Behavior: Analyzes linked intelligence documents to highlight prevalent attack patterns and vectors.
What are the latest best practices for firewall rules in mid-sized financial institutions?
ClickUp Brain Behavior: Gathers insights from internal policy documents; Brain Max can supplement with industry standards if accessible.
Draft a playbook section for ransomware attack mitigation referencing ‘Incident Response Guidelines’ and recent case studies.
ClickUp Brain Behavior: Extracts critical steps and protocols from linked resources to create a structured response plan.
Summarize performance and security differences between OpenVPN and WireGuard using ‘VPN Evaluation Q1’ data.
ClickUp Brain Behavior: Collates technical metrics and qualitative assessments from internal reports into a concise comparison.
List the most effective encryption algorithms for data at rest in cloud environments, referencing R&D and compliance documents.
ClickUp Brain Behavior: Scans internal sources to identify commonly recommended algorithms and their security notes.
From the ‘Annual Security Audit’ document, create a checklist for network device configuration reviews.
ClickUp Brain Behavior: Extracts audit criteria and formats them into actionable checklist items within a task or document.
Identify 3 emerging trends in multi-factor authentication from post-2023 security conference papers and internal research.
ClickUp Brain Behavior: Detects recurring themes and innovations from linked documents and notes.
Summarize key findings from the ‘Phishing Simulation Q1’ report regarding employee susceptibility and training gaps.
ClickUp Brain Behavior: Reviews survey data and feedback to highlight common vulnerabilities and improvement areas.
Write clear and engaging reminders for password hygiene using tone guidelines from ‘SecurityTone.pdf’.
ClickUp Brain Behavior: Adapts tone and style from the document to produce varied message drafts suitable for internal communications.
Summarize recent changes in GDPR data breach notification requirements and their implications for network monitoring.
ClickUp Brain Behavior: Reviews compliance documents and highlights key adjustments affecting security operations.
Generate guidelines for segmenting critical assets in corporate networks, referencing internal architecture and compliance standards.
ClickUp Brain Behavior: Extracts segmentation principles and compliance notes to form a clear standards checklist.
Develop a checklist for external penetration tests using OWASP and internal security policy documents.
ClickUp Brain Behavior: Identifies test scopes and criteria from PDFs and internal folders, organizing them by risk area.
Summarize features and effectiveness of leading endpoint protection platforms using competitive analysis reports.
ClickUp Brain Behavior: Synthesizes comparative data into an easy-to-digest summary or table format.
What are the main security concerns for IoT devices deployed in industrial networks since 2022?
ClickUp Brain Behavior: Aggregates findings from research notes, threat reports, and vulnerability assessments.
Summarize common user access control weaknesses found in recent audits of Southeast Asian clients.
ClickUp Brain Behavior: Extracts and prioritizes reported issues from audit reports, feedback forms, and tagged incident tickets.
LLMs vs. Workflow Intelligence: How ClickUp Brain Secures Networks
Prompts for ChatGPT
- Outline a 5-point security protocol brief based on recent network vulnerability reports.
- Compose incident response communication emphasizing clarity, urgency, and mitigation steps.
- Generate 3 alternative firewall rule sets for a corporate network and explain their protection benefits.
- Draft a stepwise procedure for deploying multi-factor authentication across remote teams.
- Compare last 3 penetration test results and summarize key weaknesses to address in upcoming audits.
Prompts for Gemini
- Propose 3 network segmentation strategies tailored for a mid-sized enterprise.
- List innovative threat detection techniques focusing on real-time anomaly identification.
- Create a risk assessment summary highlighting critical assets, vulnerabilities, and mitigation plans.
- Suggest optimized VPN configurations for secure remote access and rank by security level.
- Develop a comparison chart for three endpoint protection solutions emphasizing scalability and ease of management.
Prompts for Perplexity
- Identify 5 emerging encryption standards and evaluate their applicability in corporate networks.
- Provide a comparative analysis of intrusion detection systems focusing on accuracy and resource use.
- Summarize global cybersecurity regulations impacting data protection and compliance.
- Generate a list of 5 best practices for secure cloud network architecture and rank by effectiveness.
- Review recent network breach case studies and extract top 3 lessons for improving defenses.
Prompts for ClickUp Brain
- Transform this security audit report into prioritized remediation tasks with assigned teams and deadlines.
- Summarize threat intelligence meeting notes and create follow-up action items with responsible owners.
- Analyze network traffic logs and generate a checklist of suspicious activities needing investigation.
- Compile a task list from cross-department discussions on firewall rule updates, including urgency levels.
- Summarize penetration test feedback and produce actionable tasks for patch management and system hardening.
Transform Initial Thoughts into Solid Plans
- Convert scattered notes into polished security protocols quickly.
- Generate innovative strategies by analyzing previous threat responses.
- Develop standardized templates to accelerate each security initiative.
Brain Max Boost: Effortlessly retrieve historical incident reports, team feedback, and security documentation to fuel your upcoming defense plans.
Accelerate Network Security Collaboration
- Break down intricate security meetings into straightforward tasks.
- Transform audit findings into actionable assignments effortlessly.
- Automatically produce compliance reports and incident summaries without extra effort.
Brain Max Boost: Instantly access historical threat data, vulnerability analyses, or firewall configurations across your security projects.
How AI Prompts Enhance Every Phase of Network Security
Instantly Develop Robust Defense Strategies
Security teams explore diverse protection methods quickly, make informed choices, and prevent analysis paralysis.