In the world of cybersecurity, staying one step ahead of potential threats is crucial. That's why having a solid Penetration Testing Standard Operating Procedure (SOP) is essential for any organization. With ClickUp's Penetration Testing SOP Template, you can ensure that your team is equipped with the right tools and processes to identify vulnerabilities and strengthen your security measures.
This template empowers your team to:
- Follow a step-by-step guide for conducting thorough penetration tests
- Document findings, remediation steps, and recommendations in a centralized location
- Collaborate seamlessly with stakeholders to address vulnerabilities and improve security posture
Whether you're a seasoned cybersecurity professional or just starting out, ClickUp's Penetration Testing SOP Template will help you streamline your processes and protect your organization from potential threats. Get started today and fortify your defenses like never before!
Benefits of Penetration Testing SOP Template
Penetration testing is crucial for identifying vulnerabilities in your systems and ensuring the security of your organization. With the Penetration Testing SOP Template, you can:
- Streamline the process of conducting penetration tests, saving time and effort
- Standardize procedures and ensure consistency across all tests
- Improve the effectiveness of your tests by following a proven methodology
- Enhance communication and collaboration between team members involved in the testing process
- Mitigate risks by identifying and addressing vulnerabilities before they can be exploited
- Maintain compliance with industry regulations and security standards
Main Elements of Penetration Testing SOP Template
ClickUp's Penetration Testing SOP Template is designed to help you create a standardized operating procedure for conducting penetration testing.
This Doc template contains all the necessary sections and content to guide your team through the process. It also includes ClickUp features such as:
- Custom Statuses: Customize the statuses to reflect the different stages of your penetration testing process, such as Planning, Execution, and Reporting.
- Custom Fields: Add custom fields to categorize and track important information, such as the target system, vulnerabilities found, and remediation actions.
- Custom Views: Utilize different views like List, Board, or Calendar to organize and manage your penetration testing projects effectively.
- Project Management: Enhance your penetration testing process with ClickApps like Dependencies, Tags, Priorities, and Automations to streamline workflows and ensure efficient collaboration.
How to Use SOP for Penetration Testing
When conducting a penetration test, it's important to have a clear and organized plan in place. Follow these six steps to effectively use the Penetration Testing SOP Template in ClickUp:
1. Define scope and objectives
Before starting any penetration test, it's crucial to clearly define the scope and objectives of the test. Determine which systems, networks, or applications will be tested and what specific goals you want to achieve. This will help ensure that the test remains focused and aligned with your security needs.
Use custom fields in ClickUp to document the scope and objectives of your penetration test.
2. Conduct reconnaissance
The next step is to gather information about the target environment. This includes identifying potential vulnerabilities, weaknesses, and entry points. Conduct thorough research and reconnaissance to understand the target's infrastructure, applications, and potential attack vectors.
Use the Whiteboards feature in ClickUp to brainstorm and collect information during the reconnaissance phase.
3. Perform vulnerability assessment
Once you have gathered the necessary information, it's time to conduct a vulnerability assessment. This involves scanning the target environment for known vulnerabilities and weaknesses. Identify any potential security flaws that could be exploited during the penetration test.
Utilize the Automations feature in ClickUp to schedule vulnerability scans and track the results.
4. Exploit vulnerabilities
In this step, you will attempt to exploit the identified vulnerabilities to gain unauthorized access or control over the target system. Use various penetration testing techniques and tools to simulate real-world attacks and assess the effectiveness of your security measures.
Create tasks in ClickUp to track the progress of each vulnerability exploitation attempt.
5. Document findings and generate reports
Throughout the penetration test, it's essential to document all findings and observations. This includes detailing the vulnerabilities discovered, the steps taken to exploit them, and any successful or unsuccessful attempts. Additionally, generate comprehensive reports that provide an overview of the test, its results, and recommendations for remediation.
Use the Docs feature in ClickUp to create detailed reports and securely store all relevant documentation.
6. Review and remediate
After completing the penetration test, it's crucial to review the findings and collaborate with stakeholders to develop a plan for remediation. Address the identified vulnerabilities and implement necessary security measures to strengthen your systems and prevent future attacks.
Utilize the Goals feature in ClickUp to set targets and track progress in remediating the vulnerabilities discovered during the penetration test.
By following these six steps and utilizing the Penetration Testing SOP Template in ClickUp, you can conduct effective penetration tests and ensure the security of your systems and data.
Get Started with ClickUp's Penetration Testing SOP Template
Security teams can use this Penetration Testing SOP Template to streamline and standardize their penetration testing processes.
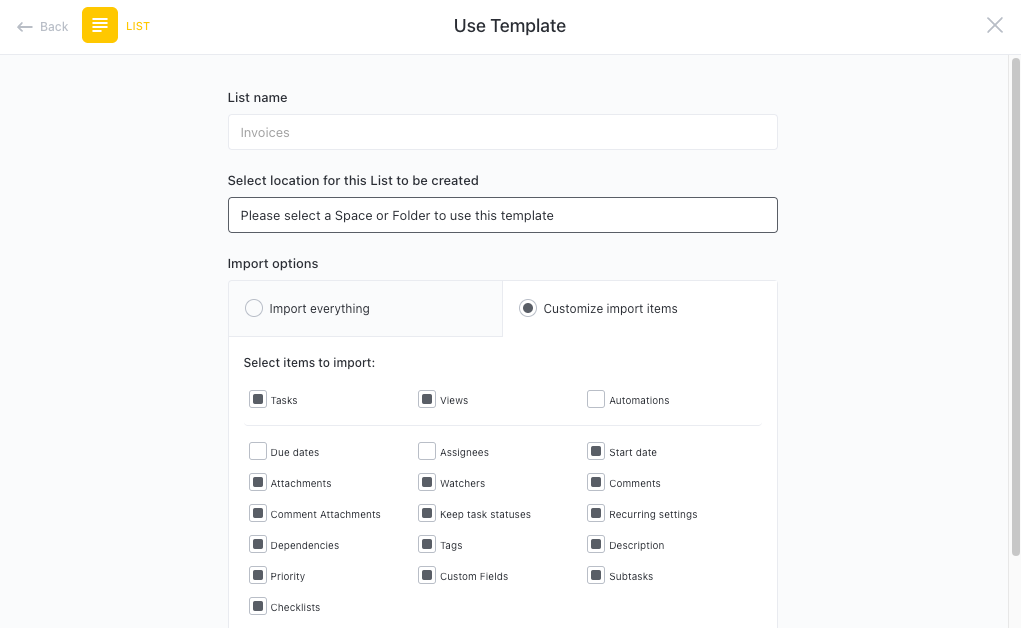
First, hit “Add Template” to sign up for ClickUp and add the template to your Workspace. Make sure you designate which Space or location in your Workspace you’d like this template applied.
Next, invite relevant members or guests to your Workspace to start collaborating.
Now you can take advantage of the full potential of this template to conduct effective penetration tests:
- Create a Checklist for pre-engagement activities, such as scoping and obtaining necessary permissions
- Use a Gantt chart view to plan and schedule each phase of the penetration testing process
- Assign tasks to team members for vulnerability scanning and exploitation
- Utilize a Board view to track the progress of each vulnerability
- Set up recurring tasks to ensure regular vulnerability assessments
- Collaborate using Comments to discuss findings and propose remediation strategies
- Create a Table view to analyze and prioritize vulnerabilities based on severity
- Generate Dashboards to monitor overall testing progress and identify areas of improvement
- Use Automations to streamline repetitive tasks and notifications for real-time updates
- Document the entire testing process in a comprehensive SOP using Docs








